First Responder UAS Triple Challenge – Shields Up! Securing UAS Navigation & Control (UAS 3.3)

Challenge overview
The purpose of the First Responder Unmanned Aircraft System (UAS) Shields Up! Challenge (UAS 3.3) was to identify UAS cybersecurity threats and to build innovative countermeasures for those threats. Specifically, contestants were asked to frame their threats and countermeasures concerning the disruption and preservation of UAS navigation and control to prevent mission failure:
- UAS Navigation: the ability of the UAS to successfully move between two points within 3D (three dimensional) airspace.
- UAS Control: the ability for a pilot-controlled UAS to successfully maintain flight control within a 3D airspace.
Contestants were required to demonstrate attacks on open-source software and encouraged to use innovation and creativity when designing their countermeasures. Possible solutions included but were not limited to:
- Updates and/or modifications to existing open-source software
- Newly developed software
- Newly developed hardware
- Secure UAS configuration guidance.
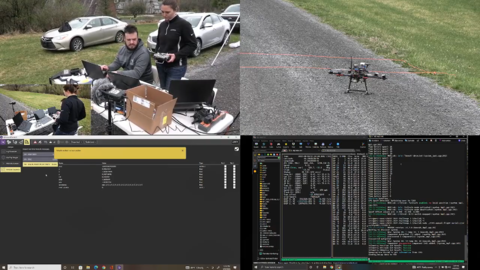
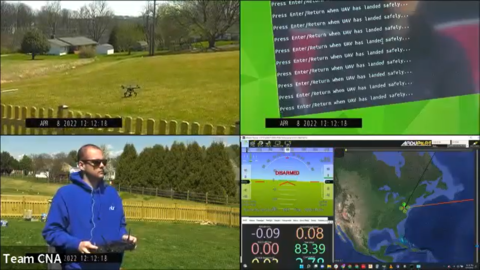
Based on concept papers (Stage 1) and demonstration videos (Stage 2), the contestants who met the evaluation criteria and had an operational UAS were selected to participate in the final live competition (Stage 3), which took place remotely at the home location of each contestant with a challenge proctor and videographer. The final deliverable for each contestant was a live demonstration of the attack and countermeasure using web conferencing tools to show judges the final solution. The contestants described their mission scenario, provided a technical summary of their solution, and demonstrated a successful attack and countermeasure of the UAS navigation and control software in the context of a real public safety mission.
Challenge results
Each of the three finalists were able to demonstrate unique and novel attacks against their UAS, and each were able to showcase innovative solutions mitigating those attacks. One team’s defense against a Video Signal Hijacking attack combined preventative and counter mechanisms to ensure an appropriate response to a successful attack. Using cryptographic transmission and strategic drone design, the team minimized the impact of Video Signal Hijacking attempts using commercially available technology. Another team’s BFDI-AP (Brute Force Default Identification - Automated Prevention) system identified and automatically corrected vulnerable UAS GCS (ground control station) settings and then emailed the operator notification of changes made or further actions needed. The team’s system can easily be integrated into public safety UAS systems and expanded to include new hardware in the future. The third team successfully demonstrated the close-range GPS (Global Positioning System) Spoofing attack. This team presented a low-cost and viable approach that uses information from existing onboard sensors and additional low-cost sensors to determine a suitable navigation solution to spoofing attacks presented at close range. All three solutions demonstrated vulnerabilities in UAS software design that may affect first responder missions and worthy of publicizing to public safety agencies.
For more information on winning solutions, click on the team names in the Stage 3 chart below. For more information on the overarching First Responder UAS Triple Challenge, including the other two challenges, please visit: 2021 First Responder UAS Triple Challenge | NIST.
Challenge winners by stage
Stage 3: live test and evaluation winners
| Winner | Amount |
|---|---|
| Team ARCC from Penn State University | $30,000 |
| Team CNA Corporation / RIIS LLC | $30,000 |
| Team ManTech / Flyt Aerospace | $30,000 |
Stage 2: video test and safety evaluation and walk-on evaluation
The following winners each received an invitation to participate in Stage 3: Live Test and Evaluation:
- Team ARCC from Penn State University
- Team CNA Corporation / RIIS LLC
- Team ManTech / Flyt Aerospace
Stage 2: check-in review
The following winners each received $2,000 in prize awards and an invitation to participate in Stage 2: Video Test and Safety Evaluation:
- Team ARCC from Penn State University
- Team CNA Corporation / RIIS LLC
- Team Cyber Resilience League
- Team ManTech / Flyt Aerospace
Stage 1: solution description
The following winners each received $3,000 in prize awards and an invitation to participate in Stage 2: Check-in Review:
- Team ARCC from Penn State University
- Team CNA Corporation / RIIS LLC
- Team Cyber Resilience League
- Team ManTech / Flyt Aerospace
UAS 3.3 was hosted by NIST’s PSCR Division and managed by Kansas State University, in partnership with Mississippi State University.

