SoloSIM
Expanding the SIM Card Use for Public Safety Challenge
1st Place - $30,000 Prize
Most Commercially Promising Award - $3,500
Creativity in Public Safety Award - $4,000

About the Team
Team Members: Conor Patrick, project lead & development; Haden Patrick, business development; Emanuele Cesena, business development; Nicolas Staldner, advisor
Conor Patrick leads the design and implementation of SoloSIM. He is a cybercorps SFS recipient from Virginia Tech, and has been working in security related applications since 2015. He started with making small U2F keys on his own, and later created this team to co-found SoloKeys. SoloKeys bootstrapped with a successful crowdfunding campaign to kickstart the first generation of SoloKeys products. Now SoloKeys continues to work on products that make authentication more secure and easy.
Haden Patrick is focused on maintaining relationships with contacts in industry and potential users of an improvement authentication solution. Haden has extensive leadership experience, stemming from his 20+ year career as a Naval officer. Haden has led high performing teams at all levels in the Navy, to include leading a crew of 200+ through all operations of a war ship and leading a department of 400+ in operation of naval nuclear propulsion plants. He has also taught college level courses on leadership and Naval history.
Emanuele Cesena is a Security Engineer at Pinterest focused on product security. Previously, he was co-founder and CTO at Theneeds (acquired by Shopkick), and a researcher in the security group at the Politecnico di Torino, Italy. Emanuele holds a PhD in Mathematics with a thesis in elliptic curve cryptography. His specialties are secure cloud computing and privacy, and he's passionate about making security easy and accessible to everyone around the globe.
Nicolas Stalder is a Data Scientist at Admetrics, focused on innovation. In a previous life, he was a high-frequency trader, and before that, an arithmetic geometer, the topic in which he holds a PhD in Mathematics from ETH Zurich, Switzerland.
The Solution
Any mention of commercial products in this video is for information only; it does not imply recommendations or endorsement by NIST.
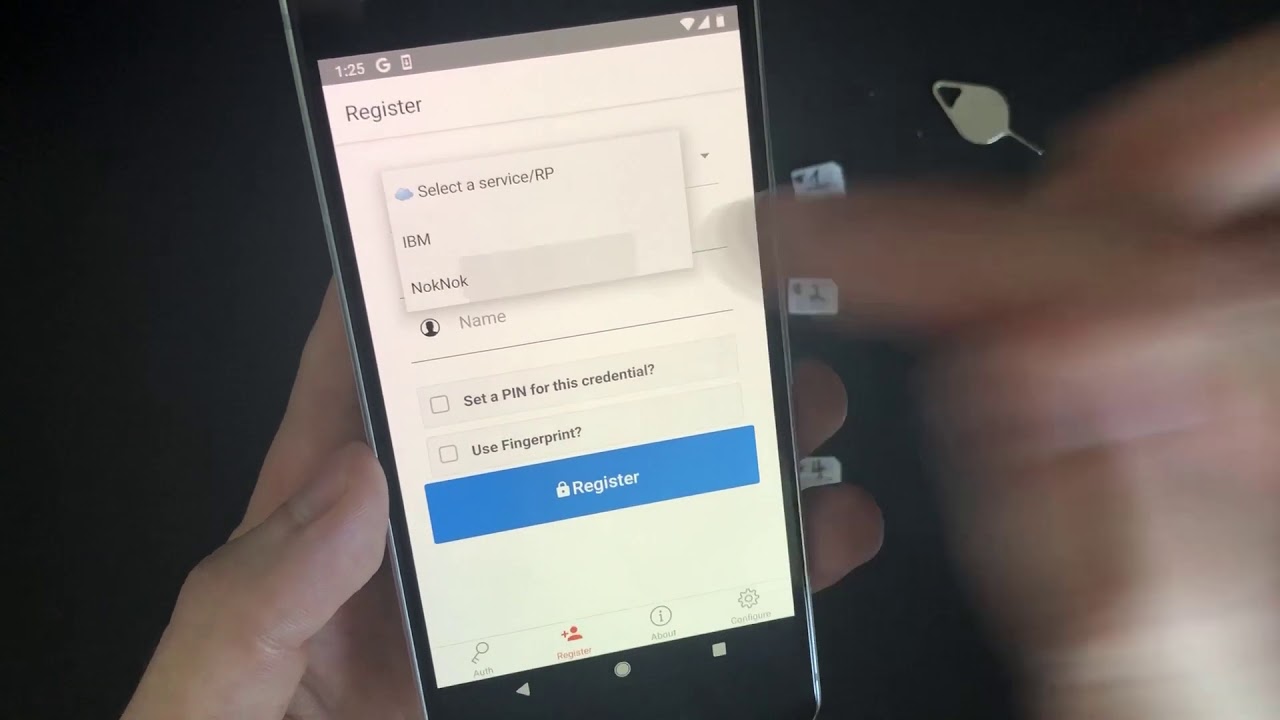
SoloSIM offered an authentication solution based on the SIM card. Their SIM card was programmed with the SoloSIM JavaCard applet, or provisioned with a SIM overlay, and then a smartphone can use it as a FIDO2 authenticator in addition to gaining mobile network access. FIDO2 authentication can be used in place of passwords to log in online.
They demonstrated the SIM Card can hold many FIDO2 credentials at a time, and each one can have a separate PIN, which could allow the SIM card to be shared amongst users. Their required PIN can be stored in the smartphone keychain, which allows authentication to proceed using a biometric (fingerprint). Provisioning of new credentials can also be done with the mobile app.
Key Features
- Authentication using SIM card instead of password
- Does not interfere with mobile network functions
- Can be administered
- SIM can hold multiple credentials and be shared securely
- Based on FIPS 140-2 hardware
- Works with many types of phones