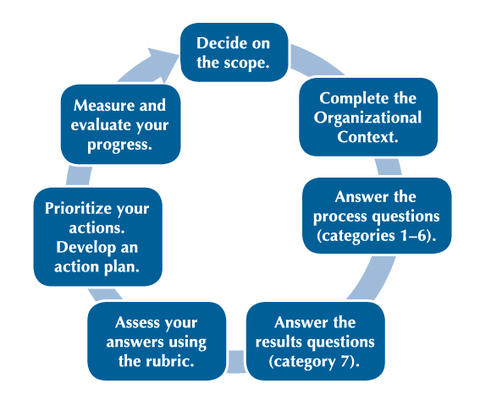
How the Baldrige Cybersecurity Excellence Builder Works
Director Message | About BCEB | Training | Blogs | FAQs | NIST Cybersecurity Framework
The BCEB asks you to describe your Organizational Context, defne your processes, and report your results. As you do so, notice the linkages among these elements (e.g., describing your workforce, detailing your workforce processes, and stating your workforce result). The linkages among these categories help you align your processes and results with your unique organizational characteristics and situation.
Scope
Organizational Context
Process Questions (Categories 1–6)
Results Questions (Category 7)
Assess Your Responses
Prioritize Your Actions; Develop an Action Plan
Measure and Evaluate Your Progress
Decide on the Scope
The Baldrige Cybersecurity Excellence Builder is most valuable as a voluntary assessment of an entire organization’s cybersecurity risk management program, but it is also useful in assessing a subunit, multiple subunits, or parts of an organization.
Complete the Organizational Context
The Organizational Context section is critically important for the following reasons:
- It helps you identify gaps in key information and focus on key cybersecurity performance requirements and results.
- You can use it as an initial self-assessment. If you identify topics for which conflicting, little, or no information is available, you can use these topics for action planning.
- It sets the context for understanding your organization’s cybersecurity-related needs and responding to the questions in the rest of the Baldrige Cybersecurity Excellence Builder.
Answer the Process Questions (Categories 1–6)
Many of the questions in these 12 items begin with “how.” In answering the questions, give information on your organization’s key cybersecurity-related processes:
- Approach: How do you accomplish your organization’s cybersecurity-related work? How systematic are the key processes you use?
- Deployment: How consistently are your key cybersecurity-related processes used in relevant parts of your organization?
- Learning: How well have you evaluated and improved your key cybersecurity-related processes? How well have improvements been shared within your organization?
- Integration: How well do your cybersecurity-related processes address your current and future organizational needs?
Answer the Results Questions (Category 7)
For these five items, give information on the cybersecurity-related results that are the most important to your organization’s success:
- Levels: For your key measures of the effectiveness and efficiency of cybersecurity-related processes, what is your current performance?
- Trends: Are the results improving, staying the same, or getting worse?
- Comparisons: How does your performance compare with that of other organizations and competitors, or with benchmarks?
- Integration: Are you tracking cybersecurity-related results that are important to your organization and consider the expectations and needs of your key stakeholders? Are you using the results in decision making?
Assess Your Answers Using the Rubic
Using the process and results assessment rubrics on pages 26 and 27, assign a descriptor (Reactive, Early, Developing, Mature, Leading, or Exemplary) to your responses to each item.
Prioritize Your Actions; Develop an Action Plan
Then determine the importance of areas of strength and opportunities for improvement. Celebrate the strengths of your cybersecurity risk management program, and build on them to improve what you do well. Sharing what you do well with the rest of your organization can speed improvement. Also, prioritize your opportunities for improving your cybersecurity-related processes and results; you cannot do everything at once. Think about what is most important for your organization as a whole at this time, balancing the differing needs and expectations of your stakeholders and your expected results, and decide what to work on first.
Measure and Evaluate Your Progress
As you respond to the questions and gauge your responses against the rubric, you will begin to identify strengths and gaps—first within the categories and then among them. The coordination of key processes, and linkages between your processes and your results, can lead to cycles of improvement. As you continue, you will begin to define the best ways to build on your strengths, close gaps, and innovate.
You might also consult relevant informative references listed in the Cybersecurity Framework. These specific sections of standards, guidelines, and practices common among critical infrastructure sectors illustrate methods to achieve the outcomes associated with cybersecurity functions.
In addition, completing this voluntary self-assessment might serve as a first step in carrying out these suggestions in the Cybersecurity Framework, section 3.0 (“How to Use the Framework”):
- 3.1 Basic Review of Cybersecurity Practices: Use the information gained from answering the self-assessment questions to compare your current cybersecurity-related activities with those outlined in the Cybersecurity Framework Core.
- 3.2 Establishing or Improving a Cybersecurity Program: Use your answers to the self-assessment questions to inform the seven steps in creating or improving a cybersecurity program.
- 3.3 Communicating Cybersecurity Requirements with Stakeholders: Your answers to the questions might inform the creation of a Target Profile.
Related Links
Baldrige Cybersecurity Excellence Builder
BCEB Process and Results QuestionsExcel
BCEB Self-Analysis Worksheet Excel
NIST Cybersecurity Framework
Resources
Baldrige Cybersecurity Initiative
NIST Cybersecurity Framework Industry Impacts
How Baldrige Works
Baldrige Key Terms
Baldrige Products and Services
Contacts
-
Baldrige Customer Service(301) 975-2036NIST/BPEP
100 Bureau Drive, M/S 1020
Gaithersburg, MD 20899-1020

