NICE Summer 2018 eNewsletter
| Featured Article | NICE Framework in Focus | Academic Spotlight | Industry Spotlight | Government Spotlight | Affiliated Programs Updates | Funded Projects Updates | NICE Working Group Updates | Key Dates |
Subscribe to the NICE eNewsletter

Welcome! My name is Christine Hysell, and I am a Summer Undergraduate Intern with the NICE program office. During the school year, I work in the Cyber Security Center at California State University, San Bernardino. I am a double major in public policy and theatre arts at the University of Redlands and have a non-technical background. At first, I wasn’t sure how much help I could provide on any cybersecurity-related issues. However, policy and cybersecurity are tightly interwoven, as shown in several of the articles featured in this publication. Growing the workforce and strengthening cybersecurity education are vital issues that have raced to the forefront. NICE supports these efforts through collaboration with academia, industry, and government and through newsletters, webinars, the NICE Framework, and many other methods. I hope to aid in this endeavor, both now and in the future, in whatever way I can. Enjoy the information provided in this eNewsletter and have a wonderful summer!
Featured Article:
PLAYING TO WIN: GAMIFICATION, CODE CHALLENGES AND HACKATHONS IN THE EMPLOYMENT MARKETPLACE
By Bradley Wolfenden, Director, Cyber Academic Partnerships, Circadence Corporation; John Bersentes, Vice President, Client Strategy, MarCom Group, Inc.
We learn about the world through play. We learn to create, to share, to challenge ourselves and others. Through playing, we keep learning.
Gamification, as a way to bring "learning through play" into the employment marketplace, is growing in importance as a tool used by organizations to improve performance of cybersecurity work. New learning methods are now more important than ever. The 21st Century has introduced five generations (i.e., Gen Z, Millennials, Gen X, Baby Boomers, the Greatest Generation) into the workforce with shifts being experienced in the employer-employee dynamics.
The use of game-based learning, code challenges, and other cyber competitions to accelerate the learning and skills development for the cybersecurity workforce has become more widespread.
These activities allow employers to create ways to make learning, team building, and skill-proving cybersecurity fun. Cyber challenges, code sprints, and other gamified activities and competitions, hold enormous promise in both the public and private sectors, and can be used in all phases of the employment lifecycle process. This includes supporting organizational needs for candidate supply, assessing skills with a more engaging candidate experience, as well as from a career development strategy to upskill existing talent.
The use of code challenges and experiential learning is growing across the talent marketplace. Competitive coding, internal challenges and assessments, and many other emerging technologies are increasingly finding their way into the commercial workplace. Much of this change reflects demands from employees. In a recent survey, 79% of respondents said they would be more productive if their work was more "game-like."[1] Workers said they would like point systems, progress bars, real-time feedback, and the ability to progress to different levels.
Companies like Amazon, Facebook, Google, AT&T, Randstad, IBM, Symantec, Home Depot, and many others have explored or used code challenges, game-based skill competitions, and hackathons as tools to engage, educate, and assess employees and candidates alike. Furthermore, Slack, a software firm that produces a communication and collaboration tool, has found success in using code challenges as part of a multi-pronged approach to diversify their workforce with programs that focus on training programmers from underrepresented populations.
Advancements in technology have led to more gamified activities in the workplace, engaging employees and students with hands-on, "technical" learning environments. Surgeons and pilots aren’t the only people who should have access to realistic, "gamified" simulation environments in which to practice.
Coding camps, competitions, and hackathons encourage and engage promising students, as well as high-potential new entrants, to become a member of the cybersecurity workforce. Students, employees, and candidates get the chance to be recognized for demonstrating cybersecurity aptitude and skills among their peers and potential supervisors in a scenario that can create and foster a sense of inclusion. Participants walk away from these events with tangible experience and resume-building content.
By following this model, one can see how the workforce development community and public policy leaders benefit from continued investment and sponsorship of these type of experiential learning endeavors for team building, diversity, and employer brand awareness.
Reskill and upskill your workforce using code challenges, code sprints, and hackathons.
The 21st century workforce needs to develop new skill-sets to keep up with the security needs created by the adoption of new applications and technologies. Activities such as code challenges, cyber competitions, and hackathons can play a dynamic role in creating opportunities for upskilling and reskilling existing employees. These learning tools promote productivity, innovation, diversity of thought, and equal opportunities for advancement. Participants benefit from developing awareness and honing their skills, and teams can identify advancement opportunities, encourage a culture of continuous learning, and provide an active, engaging work environment.
A workforce that is dedicated to continuous learning demonstrates a spirit of problem solving, exploration, and discovery vital to cybersecurity work. According to McAfee’s Winning the Game Report (April 2018), four in ten organizations say they already organize some kind of gamification exercise at least once per year. Almost all (96%) of those using gamification say they have seen benefits. The top benefits of gamification are raised awareness and knowledge among IT staff of how breaches can occur (57%), how to avoid becoming a victim of a breach (49%), and how to best react to a breach (46%); it also enforced a team work culture necessary for quick and effective cybersecurity (43%).
[1] Gamification in learning: A boon for engagement and team building, HRDIVE
NICE Framework in Focus
A profile of a cybersecurity practitioner to illustrate application of the NICE Cybersecurity Workforce Framework categories, specialty areas, and work roles.
NICE Framework Category: Securely Provision
Description: Conceptualizes, designs, procures, and/or builds secure information technology (IT) systems, with responsibility for aspects of system and/or network development.
NICE Framework Specialty Area: Risk Management
Description: Oversees, evaluates, and supports the documentation, validation, assessment, and authorization processes necessary to assure that existing and new information technology (IT) systems meet the organization's cybersecurity and risk requirements. Ensures appropriate treatment of risk, compliance, and assurance from internal and external perspectives.
Name: Julie Chua

Title: Manager, Risk Management Program, Office of Information Security
Organization: U.S. Department of Health and Human Services
Academic Degree: Bachelor of Science in Finance, University of Maryland, College Park
Certifications: Project Management Professional (PMP), Certified Information Systems Security Professional (CISSP), Certified Authorization Professional (CAP)
Q: Explain your role and responsibilities as a manager of the Risk Management Program in your organization.
A: As a manager for the Enterprise Risk Management Program, I am directly underneath the Deputy CISO and the CISO, the Chief Information Security Officer. I am responsible for the overall strategic mission and the vision of a department-wide security risk management program. I make sure that information security and privacy, as well as our healthcare industry cybersecurity, are integrated within a successive enterprise risk management program. I make sure that it is aligned with all strategic plans as well as our mission, of course, within HHS. There’s two things that I’d like to highlight in terms of the vastness of my role at HHS. There are the sector engagement and critical infrastructure risk management efforts as well as HHS federal systems and environment efforts that speaks to more of our HHS systems, protecting them and making sure they are resilient.
Q: How could you envision using the NICE Cybersecurity Workforce Framework to guide your own career as well as your role as a hiring manager for your risk management team?
A: In terms of my team’s involvement with the NICE Framework we were lucky to have been invited to do some updates to the risk management professional category itself to ensure we had a way to guide the career path towards a risk management professional. Right now it’s non-existent where you have a cybersecurity person who is interested in risk management, but would just like to be policy focused, or a risk management professional who would like to be technically focused. One of the things that I think we have tried to carve out is a path for someone who wants to do both, like myself. Or someone who is really just wanting to do a technical focus, or a strategic focus, and giving a person like myself, who are willing and able to cross that line, a path towards a career choice as well.
To listen to the full audio interview with Julie Chua, Manager, Risk Management Program, Office of Information Security, U.S. Department of Health and Human Services, click on the audio below.
Download a transcript of the interview
Academic Spotlight:
USING THE NICE CYBERSECURITY WORKFORCE FRAMEWORK TO DEVELOP A CYBERSECURITY LEGAL AWARENESS COURSE
By Dr. Jim Chen, Professor of Cybersecurity, DoD National Defense University; Mary Lin, National Defense University
Curiosity sometimes leads people to try risky things in online environments. However, experimental inquisitiveness online can have real world consequences. If unaware of these secondary effects, some may unintentionally violate laws by clicking on the wrong usa-buttons, ads, or attachments, thereby executing malicious functions of an application. The consequences can be serious as both legal and professional penalties can be very high. To address this issue, legal awareness training should be provided for students, parents, educators, and the general public. A rigorous curriculum should not only address the social and technical aspects of cyberspace, but the legal and ethical aspects as well. Ultimately, awareness training should help students differentiate what is legal from what is illegal, and distinguish what is ethical from what is not. Increasing awareness may prevent some unintentional and unnecessary cyber activities.
We envisioned a cyber legal awareness program that could address this important area of need. To begin the design process, we needed to answer two important questions: (1) what should be taught, and (2) how should it be taught? These questions can be tied to one objective of the NICE Strategic Plan: Explore methods to identify gaps in cybersecurity skills and raise awareness of training that addresses identified workforce needs (Objective 1.5). This article shares how the NICE Cybersecurity Workforce Framework (NICE Framework) served as a critical aid in the design of a cyber legal awareness course.
The NICE Framework, National Institute of Standards and Technology (NIST) Special Publication 800-181, is a nationally-focused resource that categorizes and describes cybersecurity work. The NICE Framework establishes a taxonomy and common lexicon that describes cybersecurity work and workers irrespective of where or for whom the work is performed. It is comprised of seven Categories and 33 Specialty Areas, as well as Work Roles, Tasks, and Knowledge, Skills, and Abilities (KSAs).
The NICE Framework provides employers, employees, educators, students, and training providers with a common language to define cybersecurity work. By defining the cybersecurity workforce and using standard terminology, academia and employers can synchronize education, recruitment, and development to establish a robust talent pipeline and sustain a highly qualified workforce. More importantly, it allows educators like ourselves to develop a rigorous course that connects with industry needs. The current version of the NICE Framework includes cyber legal advisor and cyber instructor work roles which can be dedicated to developing and delivering a cybersecurity legal awareness program within the specialty area of training, education, and awareness. The NICE Framework provides guidance in the development of a cyber legal awareness program.
Our design process included identifying the relevant KSAs in a relevant work role and assigning the KSAs into focus areas that are used as guidance in creating a curriculum for the program. There are at least three benefits in using this methodology. First, the common language already developed in the NICE Framework is utilized. Second, the key areas in the curriculum are determined with the help of the focus areas already identified within a relevant work role. Third, thorough coverage of focus area in a curriculum is guaranteed by including the relevant framework KSAs.
Examining the guidance of the work roles of the cyber legal advisor and the cyber instructor, the following five competencies were determined for the cyber legal awareness course:
- knowledge of leadership;
- knowledge of cyberspace fundamentals;
- knowledge of cyber law;
- analytical thinking skills; and,
- communications skills.
Each competency is fully supported by specific KSAs, as shown here:
A0118, an ability prescribed for the work role of cyber instructor, requires an understanding of technology, management, and leadership issues. Maps to Competency (1)
K0001, a piece of knowledge needed for both the work role of cyber legal advisor and the work role of cyber instructor, requires knowledge of computer networking concepts and protocols as well as network security methodologies. Maps to Competency (2)
K0003, indicates the work role of cyber legal advisor, requires knowledge of laws, regulations, policies, and ethics as they relate to cybersecurity and privacy. Maps to Competency (3)
A0070, an ability wanted for the work role of cyber instructor, requires applying critical reading or thinking skills. Maps to Competency (4)
S0356, a skill desired for the work role of cyber instructor, requires communicating with all levels of management including board members. Maps to Competency (5)
Students are put into different teams to integrate these five areas of study in the learning process. Each team is assigned a specific scenario (for example a phishing attack), then provides potential solutions based on their individual perspective as viewed through the lens of technology, legality, leadership, and communications. The differences among varied perspectives are then analyzed during a class discussion. The legal aspect is specifically emphasized and examined. This process helps students understand what is legal and what is ethical as well as the consequences of violating the law.
The images below highlight the process used to determine the five areas of study to include:
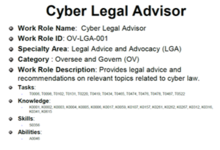
Image 1: Cyber Legal Advisor
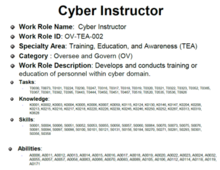
Image 2: Cyber Instructor
In this case, the NICE Framework was used to create cyber legal awareness courses as part of an overall cybersecurity curriculum. This course not only addresses the legal concepts relating to cyberspace, but it also teaches the basics of leadership, cyberspace, critical thinking skills, and communications skills. The course can easily be adopted, revised, and updated for various awareness training and education needs.
Industry Spotlight:
AS CYBERATTACKS DIVERSIFY, THOSE LEADING THE DEFENSE MUST AS WELL
By Debra McLaughlin, Sr. Manager, Corporate Responsibility, Symantec

The cybersecurity landscape is constantly changing. Businesses and individuals alike must be able to outmaneuver and defend themselves from ever-evolving threats. Both the people and the technology we rely upon need to mount a defense that maintains that pace and doesn’t become complacent.
For example, Symantec’s annual Internet Security Threat Report (ISTR) reports a 600 percent increase in “Internet of Things” (IoT)-related attacks, while “the threat landscape has become more diverse, with attackers working harder to discover new avenues of attack and cover their tracks while doing so.” New mobile malware variants increased by 54 percent, and, as the crypto currency market took off, attackers recognized a new opportunity, resulting in an 8,500 percent increase in detections of “coin miners” on endpoint computers.
Adding the dramatic growth in threat types to the well-known shortage of cybersecurity talent and lack of diversity, means the cybersecurity workforce is at a crucial juncture. We don’t have enough people, we need to be increasingly vigilant about new and different vectors of threats, and we’ve got to get serious about bringing new talent into the pipeline and helping them get skilled as quickly as possible. To illustrate our diversity issue, women make up only 11 percent of the cybersecurity workforce[1], and 9 percent are African American[2]. The U.S. Research also shows that a percentage of cybersecurity positions could be filled by individuals without a college degree[3].
How do we fill our talent pipeline with the diversity the industry requires while helping people enter the field more rapidly? Enter the Symantec Cyber Career Connection (Symantec C3) program. Founded by Symantec in June 2014, the intensive program addresses both the critical shortage of qualified cybersecurity professionals in the industry as well as the under-employment of young adults (ages 18 to 29), specifically women, people of color, and veterans. The program is intended to fill the industry’s entry-level cybersecurity employment gap with diverse candidates who are well-trained through an alternative pathway.
Symantec C3 is purposefully designed, applying classroom-based training that prepares students for key certifications, followed by meaningful hands-on internship experience, and support for job placement. Working with leading educational development nonprofits Year Up, NPower, and The Stride Center, this unique program addresses four steps of the cybersecurity workforce pipeline:
- Excite — Symantec C3 supports nonprofits and educators in raising awareness of the long-term career opportunities of cybersecurity.
- Recruit, Train and Certify — Symantec C3 recruits underserved populations into the field of cybersecurity, and offers industry-recognized training programs implemented through a network of partners.
- Prepare for Jobs — Symantec C3 places students in cybersecurity internships for on-the-job preparation and skill development.
- Launch Careers — Symantec C3 connects program graduates to cybersecurity positions through Symantec’s network of customers and partners.

To date, Symantec C3 has achieved a 79 percent graduation rate, with 65 percent of graduates hired in cybersecurity positions within six months of graduation. 60 percent of graduates are underrepresented minorities (African American and Hispanic) and 25 percent of graduates are female.
Symantec C3 alumnus Christopher Reynolds began developing expertise in cybersecurity during his military career. However, while pursuing a post-military shift to the corporate world, he quickly learned his skills were not as transferable as he thought. Christopher turned to Symantec C3 at The Stride Center to build out the skill set and experience he needed. In a recent article, he shared how the program opened his eyes to a new career path and helped him land a job with managed service provider Endsight’s helpdesk team:
“IT is a foreign language and a lot of people are afraid to jump in. The face of IT is changing. It is no longer just for white males who wear pocket protectors; it’s for all of us. African Americans who are interested in technology need to be a part of this community. Get the right education and resources to support you, and knock on the door until it opens. I’m already inside and I’ll be waiting to hold that door open for you.”
Alumna Layla Gardner underestimated her natural technical talents until she discovered the Symantec C3 program:
“I never really envisioned myself as that person who would be a technology professional. My school had honors physics, science, English classes, but no computer science. And my mother wasn’t particularly tech savvy; however, she was very supportive of my interests. I really feel that if you start with something you are interested in and dive in, you can do anything. I never thought I would have ended up where I am, but somehow I grabbed ahold of my passion and it took me somewhere I enjoy.”
Today Layla has a full-time position with a leading financial services company’s software security group, on the team that develops and reviews security code for external and internal company applications.
Symantec continues to evaluate ways to scale the program to reach more students and better prepare them through multi-stakeholder interviews, tracking progress, and establishing additional partnerships to expand the reach of this impactful program.
Additionally, the support of Symantec leadership has been key to continuing the momentum of Symantec C3. Symantec President and COO Mike Fey is an active board member for training partner NPower. Symantec employees also serve as advocates and mentors for the Symantec C3 program.
Most importantly, the students themselves are ambassadors for others from diverse backgrounds. Christopher Reynolds, who serves on The Stride Center Alumni Council, continually reports on how Alumni of the Symantec C3 program have been role models for friends and peers.
Programs like Symantec C3 show that industry can help bridge the critical gap in cybersecurity roles today and in the future. If you are interested in supporting the mission of Symantec C3 by hosting interns, hiring graduates, or donating time or resources, email SymantecC3 [at] symantec.com (SymantecC3[at]symantec[dot]com) for more information.

[1] Global Information Security Workforce Study: Women in Cybersecurity
[3] Burning Glass: Job Market Intelligence: Cybersecurity Jobs, 2015
Government Spotlight
STATE CIOs AND CISOs HIGHLIGHT UNIQUE-TO-GOVERNMENT BENEFITS TO RECRUIT AND RETAIN IT AND CYBERSECURITY PROFESSIONALS
By Yejin Jang, Director of Government Affairs, NASCIO
The National Association of State Chief Information Officers (NASCIO) is a non-profit association with a membership that includes the nation’s chief information officers (CIO). State CIOs serve as IT executives within state government and provide IT services to state executive branch agencies. Naturally, cybersecurity is a top priority for CIOs. In fact, in NASCIO’s annual survey of state CIO top ten priorities, cybersecurity has held the number one position for the past five years (See, NASCIO Top Ten).
In April, NASCIO held its 2018 Midyear Conference where state CIOs and state technology officials gathered for several days for peer exchange and to learn from each other about the priories they listed in the NASCIO Top Ten. Conference sessions focused on a variety of topics, but it was clear that the challenge of recruiting and retaining cybersecurity professionals in state government influenced much of the work and IT priorities state CIOs are charged with implementing. In fact, the state of Michigan led a conference session on their program “CISO-as-a-Service” which offers cities and counties cybersecurity assistance, effectively offering its services as a CISO for hire.
When it comes to the larger IT workforce picture, we know from the 2017 NASCIO State CIO Survey that state CIOs face incredible challenges when attempting to hire. State governments must compete with technology companies who can offer higher salaries that government can’t match. Despite the challenges, state CIOs are rising to the challenge. State CIOs are using innovative strategies like promoting non-salary benefits (71 percent), promoting the call to public service (62 percent), utilizing public-private partnerships (43 percent), sponsoring community awareness events (38 percent), among others.
Workforce issues are even more pronounced in the cybersecurity field as evinced in the 2016 Deloitte-NASCIO Cybersecurity Study. In 2016, with 49 state responses, NASCIO asked about the top five barriers to addressing cybersecurity challenges. Second behind lack of sufficient funding (81 percent), was the inadequate availability of cybersecurity professionals (51 percent). But like state CIOs, state CISOs are using innovative techniques to bring talent to state government. State CISOs are promoting job stability (53 percent), the opportunity to serve and contribute to your state (49 percent), and the challenging work environment (41 percent) to attract cybersecurity professionals.
Workforce challenges are undeniably a challenge for state CIOs and CISOs. By employing the benefits unique to government service, state CIOs and CISOs are confronting the challenge with solutions that work. NASCIO looks forward to the work of NICE and sharing best practices that can aid state CIOs and CISOs as they work to continue to recruit and retain qualified IT and cybersecurity professionals to serve state citizens.
For more information, please contact Yejin Jang at yjang [at] nascio.org (yjang[at]NASCIO[dot]org) or 202.624.8477.
Affiliated Program Updates
Various organizations within the U.S. government own and operate programs designed to enhance the cybersecurity education, training, and workforce development needs of the nation. The following are a few of those programs.
National Initiative for Cybersecurity Careers and Studies (NICCS)
The National Initiative for Cybersecurity Careers & Studies (NICCS) is the nation’s one-stop shop for cybersecurity careers and studies. It connects the public with information on cybersecurity awareness, degree programs, training, careers, and talent management. The Training Catalog connects the public to over 3,000 courses every day.
NICCS is proud to announce a new initiative highlighting National Centers of Academic Excellence (CAE) in Cyber Defense on the NICCS website.
The National Security Agency (NSA) and the Department of Homeland Security (DHS) created the National Centers of Academic Excellence program as a way to recognize and grant designations to schools that offer robust degree programs and close alignment to specific cybersecurity-related knowledge units validated by top subject matter experts in the field.
To show appreciation to the CAEs who contribute to the NICCS Training Catalog, each quarter NICCS will highlight two to four CAEs, and the courses that they provide, on the new CAE Highlights page. The New NICCS CAE Highlight page is due to be released on July 3rd, 2018.
Learn more about NICCS and the CAE program at: niccs.us-cert.gov or email us at niccs [at] hq.dhs.gov (NICCS[at]hq[dot]dhs[dot]gov) for more information.
Advanced Technological Education
The Security Technologies Advanced Technological Education (ATE) Centers are:
- The National CyberWatch Center;
- National Resource Center for Systems Security and Information Assurance (CSSIA);
- CyberWatch West (CWW); and
- Broadening Advanced Technological Education Connections (BATEC).
These Centers are producing the fifth annual Community College Cyber Summit (3CS).
3CS will take place August 2-4, 2018, at Mt. Hood Community College in Gresham, OR, and the Marriott Downtown Waterfront Hotel in Portland, OR. This is the only national academic conference focused on cybersecurity education at community colleges. The overarching theme this year is "Expanding Expertise -- Transforming Cybersecurity Programs." There will also be a pre-summit job fair on August 2nd. Participants can attend sessions organized into four tracks:
- "New to Cybersecurity";
- "Experienced in Cybersecurity, and CAE Aspirants";
- "Expanding Expertise in Curriculum"; and
- "Students."
Visit https://caecommunity.org/events/community-college-cyber-summit-3cs for more information on the agenda and links to register as an attendee and/or sign up as an employer at the pre-summit job fair. Register today at https://caecommunity.org/events/community-college-cyber-summit-3cs.
Learn more at www.atecenters.org/st and www.nsf.gov/ate.
NICE Cybersecurity Workforce Framework
The NICE Framework is a reference resource describing cybersecurity work. NIST has created a draft document, mapping competencies to the NICE Framework’s knowledge, skill, and ability statements. The draft document can be located on the NICE Framework webpage under the section for Supporting Materials. Later this year, the mapping itself will become part of an updated draft of NIST SP 800-16, a “Role-Based Model for Federal Information Technology/Cybersecurity Training.”
Many organizations begin their focus on cybersecurity by using a different framework known as the Cybersecurity Framework Core, which provides a set of desired cybersecurity activities and outcomes using common language that is easy to understand. The Core guides organizations in managing and reducing their cybersecurity risks in a way that complements an organization’s existing cybersecurity and risk management processes. NICE recognizes that many people focused on workforce would like to see a mapping that ties the Cybersecurity Framework to the NICE Framework.
Efforts are underway to develop a draft mapping between the Cybersecurity Framework’s 108 subcategories and the NICE Workforce Framework work roles that will assist organizations in making progress towards achieving improved cybersecurity. The Cybersecurity Framework subcategories are outcome-driven statements that describe various attributes of a secure network. These attributes involve activities performed by specific cybersecurity work roles to be identified by the draft mapping.
Learn more about the NICE Framework at nist.gov/nice/framework.
Funded Project Updates:
NICE Challenge Project
During the spring, the NICE Challenge Project reached a new major content milestone: the release of the Protect & Defend environment. This new environment paves the way for tons of new NICE Framework tasks, KSA, and work roles to be covered by NICE Challenges. The new environment’s network, staff, and business context is designed around a small scale big box electronics retailer. The Protect & Defend environment released 10 new challenges including: “Malware Aftermath Cleanup,” “Attack Incoming, Analysis on the Wire,” and “Incoming Zero Day! Prepare the IDS/IPS!” to name a few.
Looking forward to the next quarter we are focusing on creating and releasing new challenges in the Protect & Defend environment.
The NICE Challenge Project has two monthly webinars for curators. The "Curator Crash Course" webinar occurs on the first Friday of every month and covers everything a new curator would need to know to get started using the NICE Challenges. This includes running through a challenge, using the NICE Challenge Webportal, and discussion on integration of challenges into classes. The "Meet the NICE Challenges" webinar occurs on the third Friday of every month and covers two challenges in depth. This includes possible challenge solutions and context development methodology. Each of these webinars is about one hour in length and requires the curator to register ahead of time. More information on these webinars, and signup forms can be found at www.nice-challenge.com.
The project's development and content decisions are driven not only by our strategic vision, but by the extremely valuable feedback we receive from our growing user base, whom we feel privileged to work with on this journey forward in creating the next generation in hands-on cybersecurity content.
If you are a professor/staff member at an educational institution within the United States looking to sign up, or would just like to learn more, head over to www.nice-challenge.com.
CyberSeek
CyberSeek has been updated to include new data collected from April 2017 to March 2018. This new data indicates there are over 301,000 open jobs in cybersecurity across the nation, including over 13,000 openings in the public sector. The tool is aligned with the NICE Cybersecurity Workforce Framework and the latest data shows that the largest number of job openings, 194,224, are in the category of Operate and Maintain. This category includes work roles related to the support, administration and maintenance of IT systems, though not many pure cybersecurity roles. This demonstrates the ubiquity of cybersecurity skills across the technology spectrum.
Click here to read the full press release.
Learn more at www.cyberseek.org.
NICE Working Group Updates:
The NICE Working Group (NICEWG) continues to work toward identifying and producing deliverables that energize and promote cybersecurity education, training, and workforce development. Recently, the Cyber Range project team, under the Training and Certifications subgroup, began to meet again under the leadership of Joe Adams, Vice President of Research and Cybersecurity at Merit Network. The project team’s goals consist of developing a guidance document that describes the “who” and “what” of cyber ranges as well as a taxonomy of cyber range functions and capabilities.
Learn more about the NICE Working Group and sign up to participate at nist.gov/nice/nicewg.
Key Dates:
Community College Cyber Summit (3CS), August 2-4, 2018
Register today! 3CS will take place on August 2-4, 2018, at Mt. Hood Community College in Gresham, OR, and the Marriott Downtown Waterfront Hotel in Portland, OR. The overarching theme this year is "Expanding Expertise -- Transforming Cybersecurity Programs." Participants can attend sessions organized into four tracks: "New to Cybersecurity"; "Experienced in Cybersecurity, and CAE Aspirants"; "Expanding Expertise in Curriculum"; and "Students." There will also be a pre-summit job fair on August 2. Registration for attendees and job fair employers/recruiters is open now. Register before July 29 to avoid late registration fees.
Register today at https://caecommunity.org/events/community-college-cyber-summit-3cs.
NICE Conference and Expo, November 6-7, 2018
Submit your proposal to speak at NICE 2018! The submission period closes July 1, 2018.
The 2018 NICE Conference will take place November 6-7, 2018 in Miami, Florida. This year’s theme, “Innovations in Cybersecurity Education, Training, and Workforce Development”, inspires presentations that demonstrate new, creative, innovative, and effective approaches that will prepare, grow, and sustain a national cybersecurity workforce to safeguard and promote America’s national security and economic prosperity.
The conference will feature four tracks:
- Growing the Cybersecurity Workforce
- Expanding the Workforce Through Diversity and Inclusion
- Interdisciplinary and Cross-Domain Education and Training
- Talent Management and Workforce Development
Learn more at www.niceconference.org.
NICE K12 Cybersecurity Education Conference, December 3-4, 2018
The NICE K12 Conference will take place at the Grand Hyatt in San Antonio, Texas on December 3-4, 2018. The conference will feature five tracks:
- Increasing Cybersecurity Career Awareness
- Infusing Cybersecurity Across the Education Portfolio
- Integrating Innovative Cybersecurity Educational Approaches
- Designing Cybersecurity Academic and Career Pathways
- Promoting Cyber Awareness
Register today at www.k12cybersecurityconference.org/registration/
Learn more at www.k12cybersecurityconference.org.
NICE Webinars
On July 18, 2018 NICE will hold a webinar on “State Governments Pursuing New Tactics in the War for a Skilled Cybersecurity Workforce.” This webinar will describe how state governments are creatively looking to address both state government and industry cybersecurity workforce challenges through investments that foster innovation, entrepreneurship, and collaboration. Learn more and register today for free here.
On June 27, 2018 NICE will hold a webinar on, “Cybersecurity Education and Training for the Operational Technology Workforce.” This webinar described the differing approaches to cybersecurity in OT versus IT environments, and how education and training providers can help students and employees through specialized curriculum and lab environments, better secure ICS and SCADA systems. Learn more and register today for free here.
On May 16, 2018, NICE held a webinar on “Preparing Students through Career and Technical Education and Cybersecurity Programs of Study.” The webinar explored the differences between Career Technical Education (CTE) programs and Programs of Study, highlighting the statutory framework and federal funding that enables formal CTE Programs of Study. It also provided examples of CTE program options and Programs of Study that have been designed to position students to have successful cybersecurity career. View a recording and more here.
NICE webinars are free to attend, but registration is required.
Learn more, view webinar recordings, and more here.

