NICE 2016 Winter eNewsletter
| Featured Article | Academic Spotlight | Industry Spotlight | Government Spotlight | Affiliated Programs Updates | Funded Projects Updates | NICE Working Group Updates | Key Dates |
Subscribe to the NICE eNewsletter

NICE Lead for Industry Engagement
Featured Article:
CYBERSEEK TAKES MAPPING THE CYBERSECURITY WORKFORCE TO THE NEXT LEVEL
by Tim Herbert, Vice President of Research, CompTIA
How many cybersecurity wake-up calls does it take to spur action? Is this a rhetorical question or a bad joke? Sadly, the reality is often some of both. Despite the frequency and intensity of headline-making incidents, many businesses and public sector institutions continue to lag in their efforts to embrace cybersecurity best practices.
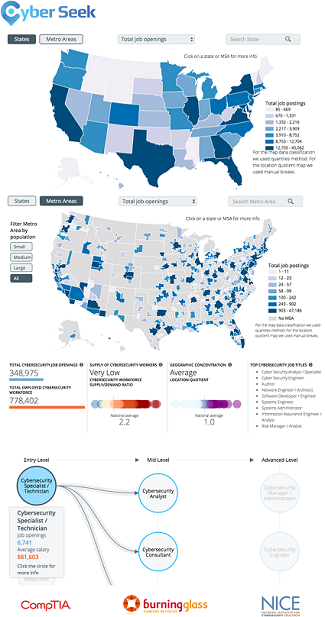
Nationally, there were nearly 350,000 job postings for cybersecurity occupations during the past year, according to CyberSeek. Relative to the base of employment, the supply-demand ratio for cybersecurity occupations is one of the tightest across the labor force. This came as no surprise to attendees of the NICE 2016 Conference in Kansas City who come face to face with the consequences of worker shortages and skills gaps on a daily basis.
The use of technology is so pervasive, security risk now extends to just about every business activity across every industry. As a result, the demand for cybersecurity talent is much deeper and broader. Relatedly, the speed of change routinely outpaces established approaches to training new workers. For example, the rate with which the Internet of Things products have hit the market have many employers scrambling to find workers with the appropriate skill sets to safeguard these new categories of connected devices and services.
While there is no silver bullet to address the multi-faceted nature of most cybersecurity issues, having a common reference point for framing the discussion is a valuable first step. A key component of CyberSeek is its alignment with the NICE Cybersecurity Workforce Framework. This alignment to the NICE Framework provides needed structure in helping employers and job seekers get on the same page in how they view the cybersecurity jobs market.
To illustrate, a job seeker in Chicago could use CyberSeek to see employers in the region who place the greatest emphasis on skills related to the Operate & Maintain category of the NICE Framework, followed by Securely Provision, and Analyze. This job seeker may realize further training in one or more of these areas could boost their job prospects. Using CyberSeek’s interactive career pathways tool, this job seeker may set an end goal of reaching the level of cybersecurity engineer, along with the average salary for this position of nearly $110,000.
CyberSeek is free to use at www.cyberseek.org. Take a look and let us know what you think or how we can make it more useful to you.
Academic Spotlight:
INTEGRATING CYBERSECURITY INTO COMPUTER SCIENCE CURRICULA
by Justin M. Serota, Teacher, Anne Arundel County Public Schools; Lisa Wenzel, Teacher, Howard County Public School System
Computer Science Education Week (CSEdWeek) is an annual program dedicated to inspiring K-12 students to take an interest in computer science. CSEdWeek is also a great time to consider folding cybersecurity topics into the computer science curriculum. While there are numerous events planned throughout the week, the most common activity includes participating in an “Hour of Code” through a number of tools. While many of these resources make programming fun through building interactive games and animations, and many highlight concepts such as functions, loops, and lists, few emphasize the importance of secure programming. Computer programming has gone through a renaissance from its early days. Today’s coding techniques include testing techniques and configuration management from the very start, but secure programming is not yet included as a central tenet of computer science. There has been a growing discussion in the education community around the how and when to teach secure programming.
Just as testing and version control are now “baked-in” to computer science courses, curricula needs to include the building blocks that form the programmer’s complete tool kit. Secure programming needs to be taught not as a stand-alone course or as a specific skill, but instead as a central concept within programming. Only an understanding of both concepts and skills allows one to be successful. Knowledge allows the programmer to think conceptually about what makes code secure. Skills enable the programmer to implement these concepts in the finished product. It is important that the education community teaches the concepts that form the fundamental basis of secure programming, but it is equally important that the workforce can apply this knowledge to their current task. Task descriptions in the NICE Cybersecurity Workforce Framework map to the job category of Securely Provision and the specialty area of Software Development which includes work roles such as Software Developer and Secure Software Assessor.
As we learn about the rising number of security incidents resulting from vulnerabilities in software, the need for secure programming is becoming more urgent. Computer users, business managers, software developers, and executives would benefit from more secure products and services. However, more support is needed to have these skills taught in today’s computer science programs. There is a growing base of resources that are being used to help explore these topics. Below are a few that we have found helpful to supplement our computer science courses. Additionally, they are useful to students preparing for cyber defense competitions.
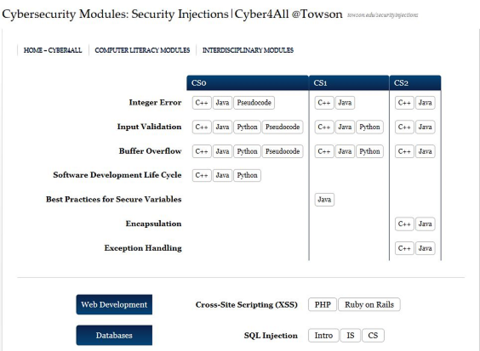
Security Injections are modules built by an interdisciplinary team at Towson University funded by the National Science Foundation (NSF). Integer Error, Input Validation, Buffer Overflow, and Software Development Life Cycle are four of the modules we have used in our computer science high school courses and CYBERSTEM summer camps. Modules include short summaries of the topic, many of which include cartoons highlighting the theme and examples of authentic occurrences, followed by interactive lab exercises, quizzes, and discussion questions for consideration.
The SEED LABS project, also funded by NSF, was developed by Syracuse University and provides hands-on laboratory exercises (called SEED labs) for computer and information security education. Our Cyber Defense team students have downloaded the pre-built virtual machine images to practice a variety of exercises. The organized diagrams and videos explaining programming vulnerabilities are helpful for computer science instruction.
One final resource that is being piloted are the cybersecurity-infused Computer Science Modules. These modules, developed through the Catalyzing Computing and Cybersecurity in Community Colleges (C5 Project), which brings together computer science faculty and cybersecurity educators from community colleges, are designed to be seamlessly incorporated into existing computing courses or bundled together to create an introductory cybersecurity-infused computer science course. Modules have been designed to align with the Advanced Placement Computer Science Principles (CSP) course, the Knowledge Units required of DHS/NSA Centers of Academic Excellence – 2 Year Colleges, and the Association for Computing Machinery Computer Science Guidelines. Modules include applied cryptography, secure scripting, responsible software development, and processing and protecting digital information.
The resources presented here are directed at a more experienced audience. There is still a gap in resources on this topic for a younger, K-8 audience. Just as cyber awareness training has been pushed to younger age groups, with the rise of technology use by children, resources exploring software security issues for this younger age group are still needed.
As we look for new ways to integrate cybersecurity in computer science, we must stay cognizant of the entire suite of NICE goals and realize that there are a variety of ways to meet these challenges. The NICE Strategic Plan wishes to accelerate learning and skills development for the cybersecurity workforce, of which computer scientists are just one aspect. We must also remember that NICE seeks to nurture a diverse learning community and facilitate the development and dissemination of a variety of academic pathways. Many of the resources above can be used outside of the classroom, for personal career growth, or as part of an employer directed program. The NICE Strategic Plan encourages the stimulation of innovative educational approaches.
If you have a favorite site you would like to share, or for more information about NICE Academic engagement activities, please contact nist.nice [at] nist.gov (nist[dot]nice[at]nist[dot]gov)..
Industry Spotlight:
HOW TO GROW A WORKFORCE IN A TIGHT LABOR MARKET: LEVERAGE THE MAJOR LEAGUE BASEBALL METHOD
by Jeremy Willingham, Services Enablement Architect, Optiv
What does Major League Baseball (MLB) have to do with developing a cybersecurity workforce? Think about a Major League roster. There are basically two categories of players. The first are the stars whose names everyone knows and who frequently appear on Sports Center. The second are the everyday players who have the skills to play in the majors without as much fanfare.
A corporate staff can be similarly categorized. There are employees who are the “stars”; those counted on to complete their tasks, handle problems that arise, and regularly go beyond expectations, such as senior consultants. Then there are the employees who have solid skills and perform their required tasks, such as consultants.
This concept takes shape in the acquisition of new talent. In MLB, when players have to be replaced (whether they left or were released) there are two methods for finding a replacement: free agency and promoting a minor leaguer. Both methods are valid. Signing a player in free agency means you already know how the player will perform, because they’ve done it. However, they cost more because they’re an established player. On the other hand, promoting a minor leaguer is cheaper but you don’t know how that player will perform in the majors. Or even if they’ll perform.
So, which method should be pursued? Both, of course. No team would be able to compete without signing players in free agency to fill holes on the roster. It’s necessary to attract talent. But the really good organizations also have a stash of blossoming players in the minor leagues. Players that have been developed over the years, whose skills have been honed to perform for the big league.
Building and maintaining a successful team requires planning; you don’t draft the hot shot high school shortstop this year to play in the majors next year. He just won’t be ready for that level of competition. You draft him to play down the line and develop him in low-pressure settings with that goal in mind. After all, minor league games aren’t front page news.
Successful teams can point to a core of “home-grown” players who have prepared to perform for the big club; players that cost less because they’re still young and proving their worth. This core of players can be supplemented by free agents to fill specific holes. It’s possible to focus solely on free agency to acquire talent, but the annual payroll ends up being incredibly high and demands an incredible success to justify. If you sign Alex Rodriguez (A-Rod), you’ve got to pay Alex Rodriguez. If you only sign players like Alex Rodriguez, you need to play in the World Series almost every year.
You might be asking yourself what all this has to do with developing a cyber workforce. It was stated earlier that employees could be categorized similar to MLB players: Senior consultants are compared to MLB Stars and consultants with the solid MLB players.
But what about the minor leaguers who may be the stars of tomorrow? That’s where entry-level employees come in. No individuals are hired today and expected to perform right away. However, they are hired today, trained for a few weeks/months and developed over time to be solid employees who may eventually become stars.
One place where this analogy fails is the corresponding labor markets. There is a surplus of MLB talent compared to roster spots available. The cybersecurity workforce is different. There are more positions available than people who are qualified to fill them. Don’t believe me? Check out cybersecurity job postings and look at the requirements for those job roles. This makes the “free agent” option more difficult. There are not enough people out there, and everybody wants to hire them. This does not apply to only security companies; many industries are creating their own security functions.
Organizations that want to grow will need a method to develop and mentor entry-level talent to create employees who can supplement the current workforce, fill holes created by attrition and eventually become the stars of the organization. Early focus should be on core skills and knowledge that apply to most/all job roles. Just as the minor league pitcher needs to perfect a fastball (because all big league pitchers need a competent fastball), they also need to develop alternate pitches to supplement it.
MLB teams use long-term planning when building out their rosters, scouting potential draft picks and mapping scenarios for their own roster (free agent defections, development of players, etc.). That same long-term planning should be applied to an organization’s workforce. Start by asking yourself:
- Who are my stars today?
- Will they still be here next year?
- What about three years from now?
- Do I have someone who can grow in to that role?
- What is the likelihood I can hire a replacement?
Every organization in the industry is dealing with this problem. The organizations that can find a way to train entry-level personnel will be better prepared to handle turnover.
So, start building your minor league!
Government Spotlight:
STATE STRATEGIES FOR STRENGTHENING CYBERSECURITY PRACTICES
by Timothy Blute, Program Director, Homeland Security and Public Safety Division, National Governor's Association
The National Governors Association (NGA) works closely with states and federal partners to tackle the policy priorities of the nation’s governors. All states aim to grow their individual economies through innovative practices in workforce development, and cybersecurity has emerged as a key dimension of such initiatives.
NGA’s Homeland Security and Public Safety (HSPS) Division is currently in the middle of two year-long projects on state cybersecurity. This past summer, NGA Chair Virginia Governor Terry McAuliffe launched Meet the Threat: States Confront the Cyber Challenge. This initiative convened state officials, federal experts and the private sector to share best practices across five core areas of state cybersecurity: critical infrastructure, public safety, health care, education, and workforce development.
The initiative recently concluded during a major summit in Boston, Massachusetts. The Summit was attended by representatives from 26 states and included multiple panels and breakout sessions on workforce development. Rodney Petersen, Director of NICE, and Lynne Clark from the NSA, gave a one-hour presentation to state officials on the opportunities and pitfalls of developing a cybersecurity workforce.
Discussions during the breakout sessions and other panels underscored a number of lessons for governors, including the importance of: recognizing a state’s unique needs and articulating realistic workforce goals; recognizing a governor’s ability to convene educators and private industry; addressing cybersecurity as a broader technology issue that demands more than additional computer science courses; promoting mid-career training for non-experts and experts; highlighting the need for flexibility within our education systems to create programs that meet the needs of the workforce; and expanding the available pool of instructors by drawing on adjunct talent and training current teachers.
In addition to workforce issues, attendees discussed the challenge of securing computer-based election systems, incentivizing critical infrastructure operators to strengthen protections for the nation’s electric grid and protecting student data and intellectual property at institutions of higher education. In addition to the Chair’s Initiative, NGA is working closely with five states: Connecticut, Illinois, Louisiana, Nevada, and Oregon to establish their own pipelines for attracting cybersecurity specialists.
For resources and more information, please visit www.nga.org/meetthethreat.
State Chief Information Officers Prioritize Cybersecurity as Top Issue in 2017
The National Association of State Chief Information Officers (NASCIO) has recently published a list of the top 10 policy and technology issues for federal chief information officers across all 50 states. This list will help drive the CIO’s agenda heading into 2017.
At the top of the list is Security and Risk Management focusing on governance, budget and resource requirements, security frameworks, data protection, training and awareness, insider threat, third party security practices as outsourcing increase, and determining what constitutes “due care” or “reasonable”. The state CIO’s plan to examine new technologies during 2017 to help achieve these policy goals.
View the full list and learn more at http://www.nascio.org/topten.
Affiliated Programs Updates:
Various organizations within the U.S. government own and operate programs designed to enhance the cybersecurity education, training, and workforce development needs of the nation. The following are a few of those programs.
Cybersecurity Education and Awareness Portal
The Cybersecurity Education and Awareness Portal (NICCS) has a new look! You will immediately see a brand new homepage with a new design and functionality. NICCS is now responsive in its design, adjusting the site presentation for optimal viewing on desktops, tablets, and mobile devices. Content is streamlined and easier to find within our three main tabs: Training, Formal Education, and Workforce Development. These three sections have always been, and remain, the focus of the NICCS mission. The Education and Training Catalog is the heart of our Training section. The robust search capabilities allow visitors to search courses by keyword, delivery method, specialty area, or proficiency level. Through geospatial mapping, users can easily search for courses based on geolocation, zip code or a specific distance. All courses remain aligned to the Cybersecurity Workforce Framework, which is presented in a more organized and informative way. Related courses from the Training Catalog into each Specialty Area’s detailed presentation are also incorporated.
Learn more at www.niccs.us-cert.gov
Federal Cybersecurity Workforce Strategy
The Office of Management and Budget and The Office of Personnel Management will be hosting the first ever cybersecurity orientation for new hires on December 14, 2016. The orientation will include presentations from Government leaders and participants will obtain an understanding of their role in supporting the Federal Government’s cybersecurity mission. The Agencies will also soon be launching an online one-stop-shop for federal cybersecurity careers.
Advanced Technological Education
The 23rd National Advanced Technological Education (ATE) Principal Investigators Conference, cosponsored by the American Association of Community Colleges (AACC) and the National Science Foundation (NSF), was held at the Omni Shoreham Hotel in Washington, DC, on October 26-28. The conference attracted over 800 participants representing community colleges, secondary school systems, four-year colleges, business and industry, federal and state government, and R&D organizations. Sessions covered many issues relevant to preparing students for technician-level jobs in a range of high-tech fields. NSF's five ATE centers for cybersecurity education, as well as other ATE grantees in cybersecurity, hosted exhibits and gave presentations.
Learn more at www.atecenters.org/st/ and www.nsf.gov/ate
National Centers of Academic Excellence in Cybersecurity
The National Security Agency (NSA), in conjunction with the Department of Homeland Security (DHS), jointly announced the designations of the following eight new institutions as NSA/DHS National Centers of Academic Excellence in Cyber Defense:
- Augusta University - CAE-CDE (GA)
- Clark State Community College - CAE-2Y (OH)
- Embry-Riddle Aeronautical University - CAE-CDE (FL)
- Florida International University - CAE-R (FL)
- Lake Superior College - CAE-2Y (MN)
- Middle Georgia State University - CAE-CDE (GA)
- Red Rocks Community College - CAE-2Y (CO)
- University of Delaware - CAE-CDE (DE)
The CAE Application Website is open for submissions for the 2017 cycle. Program requirements and other resources can be found here. The application tool will be closed June 1, 2017.
- Applications will be reviewed in the order in which they are received. Applicants are encouraged to apply early in the cycle; notification and possible feedback will be received within 10 to 12 weeks.
- Applications submitted by January 15, 2017 will be reconciled NLT May 1, 2017, and successful applicants may elect to receive their certificates in an award ceremony at the National Cyber Summit in Huntsville, AL in early June, or at the NICE Annual Conference in November
Learn more at www.caecommunity.org
CyberCorps®: Scholarship for Service
The National Science Foundation, Department of Homeland Security, and Office of Personnel Management will host an in-person career fair for CyberCorps: Scholarship for Service (SFS) students on January 4-6, 2017 in Arlington. VA. The career fair will be restricted to SFS students, Principal Investigators, Faculty, and government hiring organizations. The deadline for government organizations to register is December 9, 2016.
Learn more at www.sfs.opm.gov
GenCyber
The National Security Agency's GenCyber program, co-sponsored by the National Science Foundation, sponsors cybersecurity summer camps for students and teachers at the K-12 level. The goals of the GenCyber program are to help increase in cybersecurity and diversity in the cybersecurity career field; help students understand correct and safe on-line behavior and to improve the teaching methods for delivering cybersecurity content in the K-12 curricula. This year the program sponsored 130 GenCyber camps and reached nearly 5,000 students and 1,000 teachers across the nation.
Learn more at www.gen-cyber.com
NICE Cybersecurity Workforce Framework
The Draft NIST Special Publication 800-181, the NICE Cybersecurity Workforce Framework (NCWF) is now available for public comment. The NCWF is a national resource that categorizes and describes cybersecurity work. It provides employers, employees, educators, students, and training providers with a common language to define cybersecurity work as well as a common set of tasks and skills required to perform cybersecurity work. Read the draft and provide your comments here.
Learn more here.
Funded Projects Updates:
The U.S. government provides funding to third parties to develop products that will help advance cybersecurity education, training, and workforce development needs. The following are a few of those projects.
Cybersecurity Curriculum Development
The fiscal year 2017 Call for Cyber Security Curriculum Development Grant Proposal (supporting the Cybersecurity National Action Plan) (RFI-2017-00022) has been posted at https://www.nsa.gov/business/acquisition-resource-center/. The National Security Agency is soliciting proposals for grants in the area of cybersecurity curriculum development to meet the future workforce demands of the U.S. Federal Government. This call includes development of all documentation/materials/labs/etc. to conduct a course in a cybersecurity topic area for public use that links to the NICE Cybersecurity Workforce Framework. Proposals using innovative approaches, employing input from a diverse set of cyber training professionals, are sought. Diversity is a catalyst for insight, the flow of ideas, and innovation. Proposals are due by December 23, 2016.
NICE Challenge Project
The NICE Challenge Project has continued to enjoy a steady growth in its user base. Currently there are 75+ registered institutions from around the United States in the form of mostly two and four year universities. Some of this growth can be attributed to our continued marketing efforts in the cybersecurity education conference circuit. Recently the project was present at the following conferences: NICE Conference, NICE K12 Conference, and the CAE Community Meeting. Due to our commitment to fast and effective support as well as a steady stream of new releases in the form of features and challenge content, we have continued to receive a warm reception. In terms of ease of use, two major features were recently released to our WebPortal which allows for simplified access to virtual machines and a one stop shop for previewing challenge content for professors so they can easily plan how to use challenges in their upcoming courses. Developments are driven not only by our strategic vision but by the extremely valuable feedback we receive from our growing user base whom we are privileged to work with on this journey forward in creating the next generation in hands on cyber security content.
Learn more at www.nice-challenge.com
CyberSeek
The cybersecurity jobs heat map: CyberSeek, has recently launched its new website, cyberseek.org. CyberSeek provides an interactive online tool designed to make it easier for cybersecurity job seekers to find openings and for employers to identify the skilled workers they need. The tool features an Interactive Map and Career Pathway.
Read the full press release on CyberSeek here
Learn more here.
National Integrated Cyber Education Research Center
The Cyber Innovation Center (CIC), through its National Integrated Cyber Education Research Center, continues to empower K-12 educators across the country through the Cyber Interstate™, a robust library of STEM, cyber and computer science curricula and classroom resources, as well as dynamic professional development. Teachers from all 50 states and 2 U.S. territories are accessing the curricula. The CIC has expanded to working with state departments of education and has solidified relationships with many states around the country, including: Louisiana, Arkansas, South Carolina, California, and Virginia. Teachers are the key to a systemic and sustainable change; by empowering K-12 educators to transform their classrooms into a 21st century learning environment, we are preparing students for the 21st century jobs of today.
Learn more at www.NICERC.org
Consortium for Enabling Cybersecurity Opportunities and Research (CECOR)
CECOR continues the momentum to produce well-qualified cybersecurity professionals. At the end of year 2, CECOR partners have established 10 new cybersecurity labs in addition to the development of 8 new programs in Computer Science and Cybersecurity at partner schools that include 47 new and improved courses that focus on cybersecurity topics. Through its signature program, the CECOR Scholar, partners are leveraging the expertise across the consortium to implement and replicate evaluated activities that have emerged as best practices. The CECOR scholar represents students who have participated in standardized activities across the consortium and have displayed cybersecurity competencies. CECOR will use this signature program to affect under-represented groups and influence their decision to continue into STEM disciplines.
Learn more at http://cecork20.org/
Regional Alliances and Multistakeholder Partnerships to Stimulate (RAMPS) Cybersecurity Education and Workforce Development
The RAMPS Awardees and partners convened for a half-day pre-conference seminar at the 2016 NICE Conference and Expo. The awardees shared information about the projects they will be pursuing in the coming year and received informational briefings on the cybersecurity jobs heat map, CyberSeek, and the Draft NIST Special Publication 800-181, the NICE Cybersecurity Workforce Framework.
Learn more here.
NICE Working Group Updates:
The NICE Working Group (NICEWG) leadership team and members presented at the 2016 NICE annual Conference and Expo. Conference attendees learned about the operation of the group including information on the strategic plan, vision, and current projects of each subgroup.
The Competitions subgroup also announced the competitions white paper while at the NICE Conference on November 1, 2016. The paper, titled “Cybersecurity Games: Building Tomorrow’s Workforce” features key topics such as technical vs. soft skills, teachers vs. students, recommendations, and more. You can view a copy of the paper at http://lp.katzcy.com/cybersecuritygames.
Learn more about the NICE Working Group or sign up to participate in the NICE Working Group at the Working Group’s website.
Key Dates:
National K-12 Cybersecurity Education Conference October 6-7, 2016
The National K-12 Cybersecurity Education Conference was held October 6-7, 2017 in Arlington, VA. Check out #cyberseck12 on Twitter for a recap of the action, and the conference website for photos. Attendees can access uploaded presentations and handouts on the post-event website www.web.duuzra.com.
NICE Annual Conference & Expo 2016 November 1-2, 2016
The NICE Conference took place on November 1-2, 2016 in Kansas City, MO, with pre-conference seminars held on October 31, 2016. In alignment with the conference theme “Innovations to Shape the Future Cybersecurity Workforce”, keynotes and speakers showcased effective collaborations, bold experiments and innovations, and other game changing methods that support the NICE Strategic plan. Presentations from the conference can be viewed at www.fbcinc.com/e/nice/ncec/presentations.aspx. Also, check out #2016NICEconference on social media to see what attendees said about the conference!
Learn more at www.fbcinc.com/nice/
NICE Webinars
In celebration of National Apprenticeship week, NICE held a webinar on November 16, 2016 on “Building Your Cybersecurity Team with Apprenticeships”. Additionally, in celebration of Computer Science Education week, NICE held a webinar on “Cybersecurity for Computer Science” on December 7, 2016.
On January 18, 2017 NICE will hold a webinar on “Cybersecurity Games: Building Tomorrow’s Workforce”. Click here to register for this webinar.
NICE webinars are free to attend, but registration is required.
Learn more, view webinar recordings, and subscribe to NICE Webinar announcements at www.nist.gov/nice/webinars
Community College Innovation Challenge
The National Science Foundation and the American Association of Community Colleges has issued a challenge to teams of 3-5 community college students, faculty members, and community or industry partners to propose innovative, STEM-based solutions for real-world problems that identify one of three themes: Maker to Manufacturer, Energy & Environment, and Security Technologies.
The submission window for proposals is open until February 15, 2017. Finalists will receive an expense-paid trip to attend the innovation boot camp in Arlington, VA.
Learn more at www.nsf.gov/CCchallenge
Federal Information Systems Security Educators’ Association (FISSEA) March 14-15, 2017
The 30th Annual FISSEA Conference will be held on March 14-15, 2017 at the NIST Campus in Gaithersburg, MD. The conference is organized for information system security professionals to assist federal agencies in meeting their information system’s security awareness, training, and education responsibilities. Attendees will gain new techniques for developing and conducting training, cost effective practices, workforce development, and free resources and contacts.
Learn more at www.csrc.nist.gov/fissea
NICE Annual Conference & Expo 2017 November 7-8, 2017
Save the date for NICE 2017 in Dayton, Ohio!
It was announced at the 2016 NICE Conference held on November 1-2 in Kansas City, MO, that next year’s conference will take place in Dayton, OH on November 7-8.
Learn more at www.fbcinc.com/nice/
Contacts
FOR GENERALN INFORMATION
-
NICE Program Office(301) 975-4470100 Bureau Dr.
Gaithersburg, MD 20899

