NICE 2018 Winter eNewsletter
| Featured Article | NICE Framework in Focus | Academic Spotlight | Industry Spotlight | Government Spotlight | Affiliated Programs Updates | Funded Projects Updates | NICE Working Group Updates | Key Dates |
Subscribe to the NICE eNewsletter

Welcome! The beginning of a new year is a good time to reflect on the accomplishments of the past year and plan for the year ahead. The NICE Program Office spent some time in December celebrating all that we have achieved together as a community, ranging from the release of NIST Special Publication 800-181 NICE Cybersecurity Workforce Framework to the delivery of two, major national conferences – Annual NICE Conference & Expo and NICE K12 Cybersecurity Education Conference. There were many more significant milestones throughout the year. For a complete list visit the NICE Program Office 2017 Accomplishments. 2018 is certain to be an even more important year as NICE works together with community partners to keep advancing cybersecurity education and workforce both which are critical to our national security and economic prosperity. We need to more actively engage cybersecurity employers, from both the public and private sectors, with the collective work that is being done by the NICE community, emphasize the importance of the NICE Framework category of Securely Provision to reduce the need for more cybersecurity workers in other categories such as Protect and Defend or Investigate, describe outputs and measure impact of our various programs and initiatives, and learn from and collaborate with our international peers and partners from government, academia, and industry. This newsletter features several articles that help point to the present and future of how we can continue to work together as a community, bringing together our diverse talents and contributions, towards the common good of supporting a digital economy enabled by a knowledgeable and skilled cybersecurity workforce.
Rodney Petersen
Director of NICE
Featured Article:
COOPERATIVE EDUCATION MODEL: ACCELERATE THE CYBERSECURITY LEARNING PROCESS
By Barbara Endicott-Popovsky, Executive Director, UW Center for Information Assurance Cybersecurity; Morgan Zantua, Director Workforce Development, UW Center for Information Assurance Cybersecurity
Introduction
Cooperative education (co-op) has a track record of integrating academia to corporate settings going back to the early 1900’s in American universities. Today the cooperative education model redesign is seen as one answer to close the gap between the classroom and workplace, to providing hands-on experience, and to bridging classroom lessons and theory into rapidly changing cybersecurity corporate environments. Many two and four-year institutions of higher education offer internships for a quarter or a semester. The cybersecurity field, based upon feedback from corporate and government employers, would benefit from entry-level workers with education and experience. Apprenticeship is another approach identified as a solution available using related supplemental instruction. Two and four-year colleges and universities may view cooperative education as a delivery model for experiential education bridging the gap from the classroom to productive corporate employment.
University of Washington (UW), a Center of Academic Excellence (CAE) in-Research and Education, is tasked with developing a cooperative education model that can be adapted and implemented by two and four-year educational organizations. To accelerate research, in addition to field testing the model with corporate partners, UW assembled a panel of experts.
Panel of Experts
In early 2017 University of Washington’s Center for Information Assurance Cybersecurity (CIAC) identified three distinguishing features separating internships from cooperative education.
- Length of commitment. A co-op is more likely to span several terms or semesters and may lengthen time to degree. An internship is often a one-term assignment.
- Pay for work. A co-op is based on the assumption of paid work. While internships are commonly for pay, the fact that phrasing such as "paid internship" exists means that the unpaid sort also exist.
- Multiple exposures to a company. A co-op is more likely to involve several "tours" or "rounds" whereby students can sample different workplaces or advance from introductory experiences to more advanced assignments.
Cooperative Education Emerging Themes
The development of students into cybersecurity professionals based upon research conducted at UW CIAC integrate four success factors: Talent Search Process, Intense Personal Interest, Individualized Approach to Coaching and Mentoring, and a Well-Structured Nurturing Pedagogical Process. For the purpose of the Cooperative Education Model Factors 1 and 2, Talent Search and Intense Personal Interest, were addressed through a rigorous application and selection process of students seeking a cooperative education industry experience. Students benefited from the combined exposure of employer mentors, teachers in the professional certificate and seminar, and mentors encountered during their cooperative learning experience. Opportunities to join in professional development alongside cybersecurity professionals through seminars or mentorships accelerated their career progress.
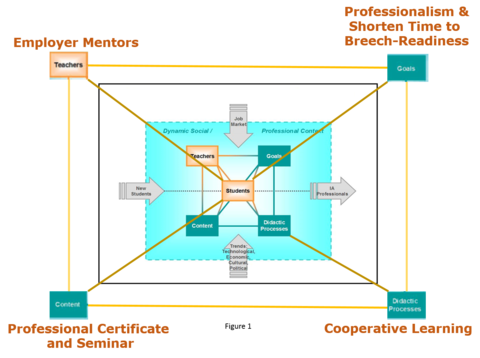
The Pedagogical Model for IA Curriculum Development (see figure 1) lays out a visual representation of the Cooperative Education Model overlaid on the knowledge based pedagogical (KBP) Model for Information Assurance Curriculum Development. The student-centric KBP Pedagogical Model compresses the learning time and deepens the development of cybersecurity professionals’ lifelong learning capacity.
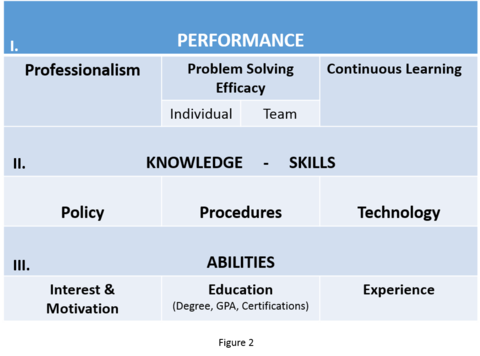
The model’s goals achieve three dimensions of professionalism in shortened period (see figure 2).
- Performance is defined as exhibiting professionalism and problem-solving efficacy on the job and indulging in a program of continuous learning.
- Knowledge - Skills acquisition is defined as understanding policy development and implementation and effective application of procedural and technological controls - the ’rules and tools’ of cybersecurity.
- Abilities is evidenced by following a student’s interest and motivation, their educational accomplishments, and their experience - especially experience relevant to cybersecurity and the level of responsibility they have attained.
Combining the models in the figures shown above, the UW CIAC devised a cybersecurity cooperative learning pilot with timeline (see figure 3)
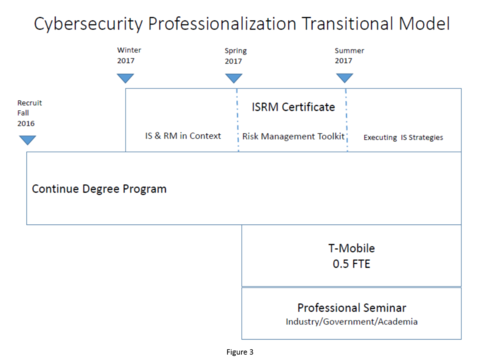
where students maintain their current academic load in the last year of their degree programs and, in addition, opt into an integrated program of professional instruction and half-time industry employment. The additional professional education includes: 1) an information security and risk management (ISRM) certificate that covers all the necessary Knowledge Units required of a CAE -Cyber Defense Education and 2) a professional seminar conducted by the university in partnership with industry to help students triage their work experience with what they’ve learned formally in the classroom. The addition of the professional seminar and certificate elements in the pilot are expected to accelerate student work readiness when they formally graduate. This model provides a setting for students to reflect and integrate on what they are learning in the classroom and learning on the job, including teamwork and the experience of adjusting to the workplace.
Corporate Partner + UW CAE = Agile Research
Academic institutions normally require a minimum of twelve to twenty-four months to design and implement new courses and programs. The UW CIAC corporate partner compressed the implementation of the co-op model. Trusted relationships and innovative cultures from all partners supported an aggressive twelve-week recruitment to co-op selection and part-time employment cycle. In the first iteration of this partnership, 9 out of 10 students received full-time offers of employment. The tenth student added the co-op experience on their resume and was hired within one month after graduation by a major Pacific Northwest software development corporation. An accelerated recruitment effort in the summer of 2017 generated a second cohort of 12 co-op students. Updates on advancements on adaptable cooperative education models are available at https://www.uwb.edu/stem/research/national-center-of-academic-excellence-in-cybersecurity-research-education.
NICE Framework in Focus
Introducing a recurring column for each issue that will profile a cybersecurity practitioner to illustrate application of the NICE Cybersecurity Workforce Framework categories, specialty areas, and work roles.
NICE Framework Category: Oversee and Govern
Description: Provides leadership, management, direction, or development and advocacy so the organization may effectively conduct cybersecurity work.
NICE Framework Specialty Area: Training, Education, and Awareness
Description: Conducts training of personnel within pertinent subject domain. Develops, plans, coordinates, delivers and/or evaluates training courses, methods, and techniques as appropriate.
Name: Carolyn Schmidt

Title: Program Manager, Security Engagement and Awareness Team, Office of Information Systems Management
Organization: National Institute of Standards and Technology, Gaithersburg Maryland
Academic Degree(s): B.S., Computer Management and Information Science, University of Maryland University College (UMUC); M.S., Cybersecurity, UMUC; M.B.A., Business Administration, UMUC
Certification: None
Q: Explain your role and responsibilities as Program Manager in the Office of Information Systems Management?
A: My role as a program manager encompasses a lot of different areas. I previously had individual responsibility for IT security and privacy awareness training and education for NIST staff operationally and they expanded that to include a supervisory skill-set.
Q: What is the size of your team and what types of roles do they fill?
A: My team is comprised of five individuals, and their responsibilities that I oversee encompass: IT security and privacy directives management supporting the NIST Chief Privacy Officer, representing NIST with our headquarters department, conducting privacy assessments, and continuing to oversee and manage IT security and privacy awareness training and education. I have some team members that are IT security officers for organizations internally that support such functions as human resources, finance, acquisitions, facilities, etc.
Q: Describe your career path to becoming a Program Manager?
A: I have been within the government, specifically with NIST, for close to thirty-three years. I actually started my career on a high school co-op program thirty-three years ago and I came on-board as a clerk typist. That was when the clerk typists were first introduced within the government. Through the years my career evolved from clerk typist to computer specialist to IT specialist, managing a BAA program on PKI technology. Then, I become a computer scientist supporting activities for the information infrastructure Task Force. Thereafter, I worked on the research side of our NIST organization where I was a system administrator and I conducted research on digital libraries. From the research organization I transitioned over to what is now our Chief Information Officer Organization supporting security and privacy internal to NIST. I do report to our Chief Information Security Officer, and I also, in a matrix fashion, report to our Chief Privacy Officer and now have the managerial responsibilities for the team.
To listen to the full audio interview with Carolyn Schmidt, Program Manager in the Office of Information Systems Management at NIST, click on the audio below.
Download a transcript of the interview
Academic Spotlight:
NEW REGIONAL RESOURCE CENTERS AND NATIONAL RESOURCE CENTERS SUPPORT CENTERS OF ACADEMIC EXCELLENCE
By Lynne Clark, National Security Agency/Department of Homeland Security Centers of Academic Excellence in Cyber Defense Program Office
The National Security Agency (NSA) and Department of Homeland Security (DHS) National Centers of Academic Excellence in Cyber Defense Program (CAE-CD) was established to promote higher education and research in cyber defense and ensure a growing number of professionals with cyber defense expertise in various disciplines. These programs set the national standards and guidelines for excellence in cybersecurity education, training, and workforce development. Students attending designated institutions are eligible to apply for scholarships and grants through the Department of Defense Information Assurance Scholarship Program and the Federal CyberCorps: Scholarship for Service Program.
Academic and institutional program requirements are stringent, and can require extensive faculty time to gather the necessary information and documentation to apply. Colleges and universities in this program are leaders in the national cybersecurity education community, both teaching and practicing cybersecurity at their institutions. Faculty in these programs work to advance cybersecurity as a profession, and continue definition of the field. The CAE-CD program is approaching 20 years, and has (as of October 2017) 232 designated institutions with the objective of growing the cybersecurity workforce necessary to meet the needs of the nation, government, industry, and academia.
With the growing number of designated programs, CAE Regional Resource Centers (CRRCs) and CAE National Resource Centers (CNRCs) were established in 2017 to provide an infrastructure among CAE-designated institutions in different geographic regions. As of October 2017, there are nine geographic regions in the CAE-CD program, each supported by a CRRC.
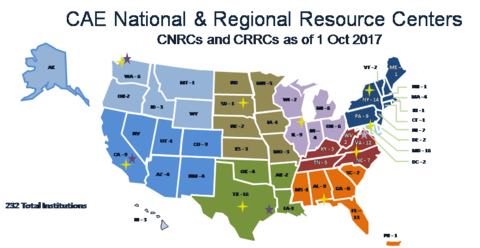
The nine geographic regions are:
North Western Region
South Western Region
South Central Region
North Central Region
Mid-Western Region
North Eastern Region
National Capital Region
East Central Region
South Eastern Region
The resource centers are exemplary volunteer CAE-CD designated institutions established to assist new institutions of higher education joining the CAE-CD program, to provide faculty professional development opportunities, and to build a cohesive community among designated colleges and universities in their region. Three categories of resource centers are positioned to assist at a regional and national level; Hub, Consultation, and National.
The Hub CAE Regional Resource Centers (CRRCs) act as a hub for institutions within the CAE-CD Candidates Program in one of the nine geographic regions. Hub CRRCs include:
- East Central Region – Forsyth Technical Community College
- New England/North Eastern Region – Mohawk Valley Community College
- North Central/Mid-Western Region – Moraine Valley Community College
- South Central Region – San Antonio College
- South Eastern Region – University of West Florida
- Western (North and South) Region– Coastline Community College
Institutions interested in becoming a CAE-CD receive support from their CRRC to assess the status of their program, have an advisor from a similar college or university assigned to assist with program development, and participate in workshops to help them meet requirements. Hub CRRCs host a variety of program and faculty development workshops, seminars, and courses for designated and candidate institutions. Hub CRRCs also collaborate with Consultation CRRCs to ensure unique higher education requirements for college and university degree programs and applications are addressed. Consultation CRRCs include:
- Dakota State University
- Northeastern University
- University of Houston
- University of Washington
Once a candidate institution has a viable program and is within one year of graduating their first cohort of students, they are eligible for a mentor. The mentor is an individual from a designated institution who has been trained by the program office and who will help the candidate prepare the application.
Four CAE National Resource Centers (CNRCs) work with the CAE Program Management Office at NSA to train mentors and peer reviewers, coordinate the work on designation requirements, and provide infrastructure support such as web pages, marketing and communications, community building events, program advocacy, and collaboration with the CRRCs. CRNCs include:
- California State University – CAE Community
- Northern Virginia Community College – Peer Review
- Prince George’s Community College – Program Development
- Whatcom Community College - Mentoring
The 2017 introduction of the six Hub CRRCs, four Consultation CRRCs, and four CNRCs, was the latest iteration of the NSA/DHS CAE-CD program. The quality and size of the national cybersecurity workforce is moving in the right direction, in part by the CAE-CD, which has helped raise the bar in postsecondary cybersecurity education. The influence of the CAE program on cybersecurity education continues to grow and the U.S. cybersecurity education is guided by the principles circumstancing CAE designation.
For more information, go to www.caecommunity.org, or email askcaeiae [at] nsa.gov (askcaeiae[at]nsa[dot]gov).
Industry Spotlight:
IMPACTING DIVERSITY – ONE PERSON AT A TIME
By Gina Mahin, Lynx CEO; Doug Yarabinetz, Lynx Chief Marketing Officer
Lynx Technology Partners (a Service Disabled Veteran Owned Small Business (SDVOSB) and a Minority Business Enterprise (MBE)) has always been about more than just delivering cybersecurity, risk, and compliance solutions. Woven into the fabric of the company is a shared mission to have an impact that goes beyond business. Lynx’s commitment to social responsibility is matched in the long-term partnership with an organization that seeks to make a meaningful difference in the lives of others while addressing a key area of concern for the industry at large.
The International Consortium of Minority Cybersecurity Professionals (ICMCP) has partnered with Lynx since its inception in 2014. Both organizations share similar goals to change the diversity landscape within the cybersecurity field. The ICMCP was launched to help bridge the ‘great cyber divide’ that results from the ongoing underrepresentation of minorities and women in the fast-growing field of cybersecurity. The ICMCP tackles this ‘divide’ with scholarship opportunities, technical training programs, innovative outreach, mentoring, and networking programs. The ICMCP targets minority and women cybersecurity professionals worldwide and promotes academic and technical excellence.
Aric Perminter is the Founder and Chairman of Lynx Technology Partners and serves as President of the ICMCP. “As the U.S. population becomes more diversified, we see an increasing need to encourage and empower the participation of women and minorities in the workforce,” says Perminter. “Cybersecurity is one of the biggest challenges to our Nation’s national and economic security and we’re facing a major talent shortfall in the industry. Under-participation by large segments of our society represents a loss of opportunity for individuals, a loss of talent in the workforce, and a loss of creativity in shaping the future of cybersecurity.”
Vanessa Joseph is currently studying criminal justice in college and through the ICMCP was matched with Aric K. Perminter as her mentor for information security. Monthly, they meet by phone to review her college and cybersecurity courses. Aric helped her select the Cyber Crime Analyst / Investigator career path, gain access to Security+ Training, and explore summer internships. "Vanessa demonstrates an unwavering commitment to her future career in cybersecurity. Upon graduating in 2018 with a BA in Administration of Justice, she will contribute to the success of any company," reports Perminter.
“We are a cybersecurity and risk management solutions provider, and we support organizations in all aspects of managing solid and secure systems and programs,” states Gina Mahin, CEO at Lynx. “What that means is, we help our clients and partners in developing policies and procedures, understanding the execution of compliance programs, and enabling them to facilitate a strong security posture through people, processes, and technology.” It’s the strength of their entire team that differentiates Lynx and which aligns so well with the goals of the ICMCP. “When we take on a customer’s mission, it becomes our own, and every individual in our company is invested in the success,” Mahin stresses. “We have an atmosphere of comradery that fosters a team-building work-ethic that promotes an on-time effective delivery method. We are transparent and face obstacles together to defeat all challenges in providing customer satisfaction.”
This requires strategies to ensure all talent, regardless of race, ethnicity or sexual orientation, feel welcome and included. This is part of the ICMCP mission. Lynx supports this mission with a formal Social Responsibility Team and donates a portion of its revenue to the cause. But the partnership goes much deeper and much higher in the Lynx organization.
From its founder, who has been involved since day one and became president of the ICMCP in early 2017, to all Lynx employees who are encouraged to participate in roles that support the ICMCP, including:
- Marketing
- eSOC Leadership and Development
- Intern Programs
- Event Planning
- Financial Investment
The relationship is mutually beneficial. “Lynx benefits greatly from our partnership with the ICMCP,” says Mahin. “We are able to collaborate with other supportive organizations and have access to amazing talent to support our company objectives. In addition, we participate because we know that our efforts will make a direct impact on diversity.” It all starts with the people and Lynx and the ICMCP are devoted to ensuring the consistent representation of women and minorities in the cybersecurity industry through programs designed to foster recruitment, inclusion, and retention – one person at a time.
Government Spotlight:
A STATE’S PERSPECTIVE TO BUILDING THE WORKFORCE
By Aaron Verdell Call, Director, Information Security , ISRM Division, Minnesota IT Services , Partners in Performance
Few information security programs have the funding or resources they need. This is especially true when the organization provides public services. In state government, every dollar spent on IT or backoffice overhead is a dollar that doesn’t directly contribute to school lunches or police training or bridge maintenance - the tangible and easily understood kinds of things that get and keep government officials in office. IT spending must be as efficient as possible to withstand the scrutiny of officials and citizens. The State of Minnesota is making progress toward consolidation of IT service delivery by breaking down agency-specific IT silos so all agencies benefit by the economies that come with larger scale. Among the benefits of bringing together larger IT teams is the ability of those team members to become more specialized as opposed to generalists. Specialization in positions, coupled with more maturity in processes and consistency in IT implementation, creates a fertile landscape for documentation and focused training. Professional judgement can be removed from certain routine tasks, avoiding some opportunities to make mistakes. Those tasks that still need creative thinking have fewer complexities to know or consider, minimizing organizational risk. These are especially good things for an organization that supports life safety systems or manages sensitive information about millions of people. Decreasing the number of positions that require volumes of historical or institutional knowledge means more positions can be filled by less experienced personnel. That is, staff have lower salary requirements making offers from the government more competitive.
People, including those looking to maximize their salary, are looking at careers in cybersecurity. State government has an appealing position in being big enough to have access to large-scale enterprise technology, but still small enough for individuals to make meaningful impact. State government also benefits from the Federal Government’s CyberCorps: Scholarship for Service program. Through this program, qualifying students receive tuition and stipends in exchange for working in civil service. This candidate pool super-charges security programs designed to embrace people new to the workforce that has a slightly higher-degree of turnover.
Part of this model requires organizations to accept being a training ground for other better funded organizations. Fortunately, supporting citizens and local businesses is part of what state government does so the pill can be less bitter. In any case, bringing fresh talent into an empowering environment benefits the employee and employer. It also gives employers time to spend with current or future star performers and convince them of the long-term benefit and value of government service. Workers with a few years of experience leaving for higher pay or other reasons create opportunities to promote stand-out internal personnel, or at least give them a chance to try a new role. A little churn means those that stick around get to keep expanding their skillsets. Those that value learning and appreciate this aspect of an organization are often the most valuable to a cybersecurity program.
Designed correctly, this staffing model becomes a machine that continuously flows fresh ideas, facilitates learning, and promotes from within, providing desirable traits regardless of a program’s budget.
Affiliated Programs Updates:
Various organizations within the U.S. government own and operate programs designed to enhance the cybersecurity education, training, and workforce development needs of the nation. The following are a few of those programs.
National Initiative for Cybersecurity Careers and Studies (NICCS)
On December 12, 2017, the NICCS website updated and enhanced the content for the National Initiative for Cybersecurity Education (NICE) Cybersecurity Workforce Framework functionality. The increased functionality enables users to navigate the framework in a seamless and easy to use fashion, while clearly defining and disseminating the knowledge, skills, abilities, and tasks associated with each category of the framework. In addition, the NICCS website will be releasing the Cybersecurity workforce framework mapping tool in the spring that will enable users the ability to map cybersecurity positions to the framework as a mechanism for assessment. For more information, please visit: https://niccs.us-cert.gov/workforce-development/cyber-security-workforce-framework
Learn more at www.niccs.us-cert.gov
Advanced Technological Education
The Advanced Technological Education (ATE) program provides grants that support the development of innovative approaches for educating highly skilled technicians for the industries that drive the nation’s economy. In tandem with creating products to improve students’ learning, many ATE grantees offer professional development for faculty. The ATE program funds large, comprehensive Centers of Excellence, as well as smaller-scale, more focused projects. Each ATE Center generally involves a collaboration among several educational institutions, along with partners from business, industry, and government, all of which work together to improve education and build the workforce in a particular area of technology. View a one pager on the ATE program here.
Learn more at www.atecenters.org/st and www.nsf.gov/ate
GenCyber
GenCyber’s mission is to grow the cybersecurity workforce for the United States. The program is funded by the National Security Agency and the National Science Foundation and sponsors summer camps across the Nation for elementary, middle, and high school students and teachers. The camps focus on engaging learners with sound cybersecurity principles and teaching techniques.
The GenCyber program continues to grow and generate a broader awareness of, and interest in, cybersecurity. In the future, GenCyber will have a positive impact on the number of qualified cybersecurity professionals entering the Nation’s workforce. Learn more by watching the GenCyber video here: https://www.youtube.com/watch?time_continue=56&v=oSCR5FTAJhU.
Learn more about the camps at www.gen-cyber.com
NICE Cybersecurity Workforce Framework
The NICE Framework serves as a fundamental reference to support a workforce capable of meeting an organization’s cybersecurity needs. It provides organizations with a common, consistent lexicon that categorizes and describes cybersecurity work by Category, Specialty Area, and Work Role. It is a resource from which organizations or sectors can develop additional publications or tools that meet their needs to define or provide guidance on different aspects of workforce development, planning, training, and education.
Check out the publication at http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-181.pdf
During the NICE Conference, held in November 2017, the new NICE Framework Work Role Capability Indicators: Indicators for Performing Work Roles Report was announced. While the Work Roles have made the NICE Framework easier to associate to specific positions, they do not provide organizations with guidance on how to determine if a cybersecurity worker can perform a Work Role. This report provides capability indicators which are intended to help organizations address this challenge.
View the draft Capability Indicators Report at https://csrc.nist.gov/publications/detail/nistir/8193/draft
Learn more here.
Funded Projects Updates:
The U.S. government provides funding to third parties to develop products that will help advance cybersecurity education, training, and workforce development needs. The following are a few of those projects.
NICE Challenge Project
With the new year upon us, the NICE Challenge Project is ready to start off the year with a bang!
During the last quarter of 2017, the project has been overhauling the player (student) section of its web platform. This new overhaul is not only a fresh coat of paint for the user interface (UI) that breaths new realism into challenges, but also a redesign of the deployment process making it simpler.
While players will see a big UI change, curators (professor/staff) will see a huge increase in the availability of workspaces (previously called pods). The number of future reservations curators can make will increase from two to four. Also, our virtual infrastructure’s capacity for workspaces will increase roughly fourfold. This will result in the availability of approximately four hundred concurrent workspaces per day for players and curators.
However, curators have more to look forward to then workspace capacity. We are introducing a new feature on the web platform related to challenge submission reports. This feature, "Check Types", will add a new layer of depth to challenge checks. Check Types will label all of our checks with a type. This type has a defined behavior and purpose, which will allow for curators to more easily understand the output of a check in our submission reports.
New and current curators now have two more things, aside from new features and capacity, available to them which are monthly webinars. The "Curator Crash Course" webinar occurs on the first Friday of every month and covers everything a new curator would need to know to get started using the NICE Challenges. This includes running through a challenge, using the NICE Challenge Webportal, and discussion on integration of challenges into classes. The "Meet the NICE Challenges" Webinar occurs on the third Friday of every month and covers two challenges in depth. This includes possible challenge solutions and context development methodology. Each of these webinars are about one hour in length and require the curator to register ahead of time. More information on the webinars along with signup forms can be found at www.nice-challenge.com.
In terms of content, the NICE Challenge Project now has 70+ unique challenges available. Over the course of the upcoming year, we will be focusing on expanding deeper into the Protect & Defend category of the NICE Framework.
The project's development and content decisions are driven not only by our strategic vision, but by the extremely valuable feedback we receive from our growing user base, whom we feel privileged to work with on this journey forward in creating the next generation in hands-on cybersecurity content.
If you are a professor/staff member at an educational institution within the United States looking to sign up, or would just like to learn more, head over to www.nice-challenge.com.
CyberSeek
Several new features have been added to CyberSeek to provide greater visibility into the supply and demand of cybersecurity workers at the national, state, and metropolitan levels. One key new feature of the CyberSeek heat map is the ability to track data on cybersecurity job demand overall and within the public and private sectors. The CyberSeek career pathway, which maps to the NICE Cybersecurity Workforce Framework, has also been enhanced to help both individuals interested in cybersecurity careers and employers looking to fill job openings. The expanded, interactive career pathway includes information on 10 core cybersecurity roles and 5 tech jobs that often serve as “feeder roles” to cybersecurity positions.
The updated site also includes an embeddable heat map and career pathway widgets. Anyone interested in the cybersecurity workforce can embed versions of the heat map and career pathway on their websites with links back to CyberSeek.org.
Learn more at www.cyberseek.org
National Integrated Cyber Education Research Center
A foundation for growing a cyber-literate workforce begins in K-12 education. Educators across the country are not only shaping our future workforce with the knowledge, skills and abilities needed for opportunities of today and tomorrow, they are fulfilling a gap that will protect the security of our country. The Department of Homeland Security Cybersecurity Education Training and Assistance Program (CETAP), in partnership with the Cyber Innovation Center and its National Integrated Cyber Education Research Center (NICERC) continue to positively influence the K-12 classroom through project driven, cyber-based curricula and professional development programs for teachers in order to begin systematically empowering educators with the resources needed to prepare our students and our future workforce. These resources, available to every K-12 educator at no cost, span across the country with teachers from all 50 states accessing and integrating the curricula into their classrooms. In addition, partnerships with state departments of education are being solidified to seamlessly integrate concepts of cybersecurity into existing math, science and liberal arts state-level standards.
Learn more at www.NICERC.org
Regional Alliances and Multi-Stakeholder Partnerships to Stimulate (RAMPS) Cybersecurity Education and Workforce Development
Regional Alliances and Multi-Stakeholder Partnerships to Stimulate (RAMPS) Cybersecurity Education and Workforce Development
The RAMPS programs continue to reach major milestones and accomplishments. Here’s a recap of a few major highlights from 2017:
Collectively, the five RAMPS projects have partnered with over 170 organizations, leading to the execution of multiple summer camps, curriculum development and course development, articulation agreements, and the establishment of local internships and apprenticeships.
For example, the Arizona Statewide Cyber Workforce Consortium in the greater Phoenix area has hosted summer boot camps and cybersecurity awareness activities for students in primary and secondary education. The University of Albany has streamlined its cybersecurity programs into an integrated set of courses aligned to the NICE Framework. Old Dominion University has signed articulation agreements with two local community colleges, allowing the transfer of Associate degree work toward Bachelor degrees, thereby saving a student approximately 50 credit hours or 1.5 years of schooling. Securing internships and apprenticeships for students has also been a major accomplishment of the RAMPS program. The Cyber Prep Program in Colorado Springs, Colorado worked with seven local employers to organize a six-week paid internship for high school students, many of whom have been invited to stay on-board or return after graduation.
Learn more about each of the RAMPS programs by visiting their websites listed below:
The Partnership to Advance Cybersecurity Education and Training (PACET)
Learn more at www.albany.edu/facets
The Hampton Roads Cybersecurity Education, Workforce and Economic Development Alliance (HRCyber)
Learn more at www.securitybehavior.com/hrcyber
Cincinnati-Dayton Cyber Corridor (Cin-Day Cyber)
Learn more at www.soche.org
Cyber Prep Program
[link no longer active]
The Arizona Statewide Cyber Workforce Consortium
Learn more at www.ArizonaCyber.org
NICE Working Group Updates:
The NICE Working Group (NICEWG) continues to work toward identifying and producing deliverables that energize and promote cybersecurity education, training, and workforce development. For example, the Training and Certifications subgroup is working on a mapping of industry certifications to the NICE Framework. The project will aim to establish criteria and standards of measurements for effective mapping of certifications and improve utilization of performance-based assessments which integrates cognitive/skill acquisition models beneficial to build cyber resiliency for the nation.
Learn more at https://www.nist.gov/itl/applied-cybersecurity/nice/about/working-group/training-and-certifications-sub-working-group.
Discussions on projects like these and more take place monthly in each of the following five subgroup areas: K-12, Collegiate, Competitions, Training and Certifications, and Workforce Management.
Learn more about the NICE Working Group and sign up to participate in the NICE Working Group at the Working Group’s website.
Key Dates:
Federal Information Systems Security Educators’ Association (FISSEA), March 14-15, 2018
The Annual FISSEA Conference will be held on March 14-15, 2018 at the NIST Campus in Gaithersburg, MD. The conference is organized for information system security professionals to assist federal agencies in meeting their information system’s security awareness, training, and education responsibilities. Attendees will gain new techniques for developing and conducting training, cost effective practices, workforce development, and free resources and contacts.
Learn more at FISSEA | NIST.
Women in CyberSecurity (WiCyS) Conference, March 23-24, 2018
The WiCyS Conference will be held March 23-24, 2018 in Chicago, Illinois. WiCyS is a continuing effort to recruit, retain and advance women in cybersecurity. It brings together women (students/faculty/researchers/professionals) in cybersecurity from academia, research and industry for sharing of knowledge/experience, networking and mentoring.
Registration for WiCYs is OPEN NOW!
Student registration is only available via scholarship or sponsorship. Although student scholarship applications have ended, applications to attend can be submitted here.
All other registrations (faculty, professionals) close February15, 2018 or at capacity (whichever comes first).
Learn more and register at https://www.wicys.org/
NICE K-12 Cybersecurity Education Conference, December 3-4, 2018
Save the date for the NICE K-12 Cybersecurity Education Conference! In 2018, the NICE K-12 Conference will take place in San Antonio, Texas on December 3-4.
Learn more at https://www.nist,gov/nice/k-12conference
NICE Webinars
On February 21, 2018 NICE will host a webinar on “Development of Soft Skills That Are in Demand by Cybersecurity Employers.” This webinar will explore frameworks, resources, and effective approaches for developing soft skills to complement NICE Framework KSA’s to develop a well-rounded cybersecurity workforce. Learn more and register for the webinar here.
On January 17, 2018 NICE hosted a webinar on “Writing Cybersecurity Position Descriptions for the Greatest Impact.” This webinar described how human resources professionals and hiring managers can leverage the NICE Framework to develop more effective position descriptions and job announcements and in the process recruit and attract a more diverse workforce. View a recording and more here.
On November 15, 2017 NICE hosted a webinar on “A Path to Obtaining Cybersecurity Work Experience: Internships, Cooperative Education, and Apprenticeships.” This webinar focused on a variety of underutilized and emerging work-based learning and experiential learning methods such as internships, cooperative education, and apprenticeships. View a recording and more here.
On October 18, 2017 NICE hosted a webinar on “Cybersecurity Careers for Autistic People.” This webinar informed the participants of research efforts and corporate initiatives to increase the participation of autistic adults in the workforce. Specific attention was paid to jobs and skills appropriate to the cybersecurity workforce. View a recording and more here.
NICE webinars are free to attend, but registration is required.
Learn more, view webinar recordings, and more here.

