NICE Framework in Focus: Leeza Garber, Esq.
This Framework in Focus interview was featured in the Winter 2020-21 NICE eNewsletter.
Leeza Garber, Esq.
Title/Organization: Privacy & Cybersecurity Attorney; Co-Founder of Can. Trust. Will., LLC; Adjunct Professor at Drexel University's Thomas R. Kline School of Law (Information Privacy Law) and Guest Lecturer at The University of Pennsylvania's The Wharton School (Internet Law)
NICE Framework Category: Oversee and Govern
NICE Framework Work Roles: Cyber Legal Advisor, Executive Cyber Leadership, Privacy Compliance
Academic Degrees: Bryn Mawr College, cum laude, B.A. 2008, University of Pennsylvania Law School, J.D., 2011, The Wharton School, Certificate in Business and Public Policy, 2011
Certifications: None
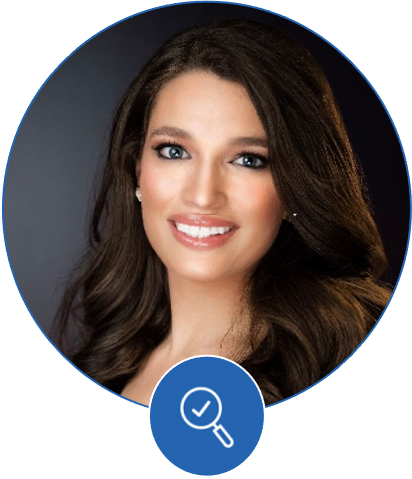
Leeza Garber is an attorney who specializes in privacy and cybersecurity law, a corporate keynote speaker and consultant offering problem-solving sessions related to cybersecurity, and a co-founder of Can. Trust. Will., a best hiring practices LLC focused on cybersecurity hiring. In addition, Ms. Garber teaches Internet Law at The Wharton School at the University of Pennsylvania and is an adjunct professor at Drexel University's Thomas R. Kline School of Law, Drexel Law School where she teaches Information Privacy Law. Below is a summary of her conversation with Karen A. Wetzel, Manager of the NICE Framework:
Karen: Welcome, Leeza, and thank you for joining us here today. Can you explain a little bit more about your roles and responsibilities as an attorney specializing in cybersecurity and privacy law?
Leeza: In general, attorneys are trusted advisors, whether they are litigators or performing contract work. In cybersecurity and privacy, litigators deal with active cases on data breaches or standards in cybersecurity and then the flip side is the contract work that might be dealing with insurance, cybersecurity insurance, different policies, best practices and procedures, legal standards, or privacy policies.
For me, I was passionate about tech, cybersecurity, and privacy, and that led me to consulting in these areas. It’s also a way to pursue my academic interests in teaching law students and undergraduates the importance of information privacy and internet law.
Karen: We just finished up our NICE Conference for this year and you presented on “Putting the NICE Framework to Work: Hiring Cybersecurity Talent that is Highly Able and Not Just Highly Skilled.” Could you share about that distinction and how the NICE Framework can be used as a guide in one’s career?
Leeza: The point of this presentation was to share that the key to a hiring process for cybersecurity isn’t just to look for people who have all of the bells and whistles in terms of cyber education, but to really understand what you need. That is something that the NICE Framework details thoroughly in terms of what kind of work roles exist, and it provides that fundamental groundwork for understanding what your company needs. There may be someone who is very highly skilled but not able; the fundamental difference is what the person can do and what they actually will do, particularly when under stress. But how do you filter for that in a hiring process? We argue that you first filter for can, the capabilities, and then you filter for will, what a person actually will do in a certain situation. It comes down to a behavioral interview.
Karen: Following on that, what kinds of cybersecurity jobs do you think are the most difficult to fill?
Leeza: There are so many unfilled positions related to cybersecurity—it’s not just one specific job or role that’s tough to fill, it’s all of them. I think it’s because we’re approaching cybersecurity job applicant pools in the wrong way. It requires not just an audit of what your organization currently has or is missing; it’s also a question of finding, hiring, and keeping the right employees. For cybersecurity it’s always going to be difficult because they’re in-demand—it doesn’t matter if you have a really incredible paycheck offering, or benefits package, or a pool table in the office. It’s about the culture of your company and finding the person who can will get the job done.
There number of open positions is only going to grow, too, as more as organizations realize they need people in cybersecurity and as new roles emerge. Being able to come back to a great resource like the NICE Framework helps to make people feel less overwhelmed.
Karen: How important is it to have a cybersecurity related academic degree or certification in this field and how does that relate to Competencies?
Leeza: My business partner and I have a manuscript for a book coming out next year on cybersecurity hiring. As part of that work, we got to interview quite a few folks, including Rodney Petersen, the Director of NICE, who said, “Position descriptions are over-spec’d and the number of open jobs and certification requirements often exceed the number of people available who even hold them in the universe.” I thought that was illustrative of some of the problems; yes, there are not enough people, but we may not be looking in the right places, either.
I’m an educator in cybersecurity and I fully believe in many of the academic programs that are offered in the field if you learn that way. Certifications are also a fantastic opportunity as long as you choose the right ones. But, in essence, competencies come from experience—and that can be work or personal experience. If you know someone is right for you because they have the abilities—the “will” to get things done in your office on your cybersecurity team—then give them the opportunity to gain the experience on the job and earn the certs after. In essence, it depends on what correlates to success for a specific role for your specific organization. That comes back to understanding what you need and that comes back to the NICE Framework.
It may seem more labor intensive, more of an obligation, and more responsibility to be intentional about job descriptions—updating them and making sure your team continues to get the right training. In the end it’s just like data breaches: if you put in that effort up front and be proactive, you’re going to be better off down the line. Saying, “We can’t stay ahead of the curve, but we can try to stay on top of it”—that’s the way to go.
Karen: My next question is about diversity and how it plays into your work. What advice do you have for organizations looking to broaden their workforce diversity?
Leeza: When we talk about diversity and inclusion its really diversity versus uniformity. The analogy my writing partner for the book loves to use is a soccer field: if you don’t have diversity on your team, it’s the same as putting eleven goalies on a soccer field. Cybersecurity is driven by creativity: it’s problem solving and being able to work quickly under pressure—we need diverse talent to attack a problem from multiple perspectives. We have to do it because it will lead to our success, plain and simple.
One of the things I love about the NICE Framework is that it’s coming at it from all angles. Yes, we need the techies who will handle incident response and the digital investigations and building firewalls, but we also need the person who’s going to come in from a legal perspective or from a risk management perspective. There are so many ways into this field.
Karen: What do you enjoy most about the work you do?
Leeza: One of the most fulfilling pieces of my work is getting to talk to students who are intrigued by entering into a career in cybersecurity. Last semester I taught a class of sixty undergraduates from different backgrounds and majors interested in learning about internet law; a great bulk of the course was spent on cybersecurity. It is wonderful for these students to understand that they have something extremely valuable and significant to add to the discussion on policy, procedure, and the law. Being able to guide them and let them know about all the opportunities available in this field is something I absolutely adore and wouldn’t trade for anything.
Karen: Is there advice you typically give to new students as they are entering in this field?
Leeza: My main advice is to find the thing you’re most excited about within the field and to push forward in it, because you have something valuable to say about that should be heard. You have to be passionate about what you’re doing in order to want to stay up to date, stay educated and trained on it, to accept the intertwining nature between cybersecurity and the actual business of your company.
Karen: That’s great advice for not only new people in the field but all of us. Thank you so much for your time today. I’m sure our listeners are going to be thrilled to hear your perspectives and we’ll look forward to your book next year!
To listen to the full audio interview with Leeza Garber, click on the audio below:
Download a full transcript of the interview.

