Cybersecurity Insights
a NIST blog

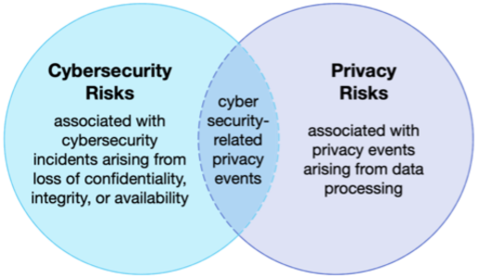
As part of NIST’s 50th anniversary of cybersecurity, this month’s blog post is centered on privacy at NIST. Since many of you have become familiar with the Privacy Engineering Program’s popular Venn diagram showing the relationship between cybersecurity and privacy risks, let’s use it to show how NIST has expanded and matured its understanding of privacy over the last 50 years.
If we go back in time to the 1960s, data privacy really came into focus when the growing use of computers created concerns about secret databases of people’s information. The report, Records, Computers, and the Rights of Citizens, released in July 1973 by the Department of Health, Education, and Welfare, recommended that there be a federal “Code of Fair Information Practice” for all automated personal data systems. This report provided a basis for the Privacy Act of 1974, which established requirements for federal agencies and personally identifiable information (PII). NIST’s foray into privacy began in May 1975 with the Computer Security Guidelines for Implementing the Privacy Act of 1974 (withdrawn).
Following these initial guidelines, NIST began developing standards for cryptography and encryption. Directly addressing the Venn diagram overlap (cybersecurity-related privacy events), cryptography and encryption are fundamental to modern security and privacy because they enable data confidentiality, protection from unauthorized modification, and source authentication. In 2010, NIST released SP 800-122, Guide to Protecting the Confidentiality of Personally Identifiable Information (PII). While essentially still situated in the overlap, the guide did recognize that privacy is broader than just protecting the confidentiality of PII.
The year 2014 marked the first steps towards NIST’s treatment of privacy as an independent, albeit related, discipline to cybersecurity. The NIST Cybersecurity Framework V1.1 was released with a methodology for protecting privacy and civil liberties, recognizing that although cybersecurity can protect privacy, certain methods or measures can also create privacy risks. Volume 2 of NISTIR 7628 Rev. 1, Guidelines for Smart Grid Cybersecurity focused on privacy and the smart grid. It identified privacy risks specific to the Smart Grid and distinct from cybersecurity risks.
NIST’s Privacy Engineering Program (PEP) was established and accelerated the conceptualization of privacy risk management. PEP introduced a generalizable model for identifying privacy risks in systems processing data and a set of privacy engineering objectives with the publication of NISTIR 8062, An Introduction to Privacy Engineering and Risk Management in Federal Systems and the Privacy Risk Assessment Methodology (PRAM). PEP also began integrating privacy guidance with cybersecurity guidance. SP 800-63-3, Digital Identity Guidelines was the first publication to fully integrate privacy, but others quickly followed, including SP 800-37 Rev. 2, Risk Management Framework for Information Systems and Organizations: A System Life Cycle Approach for Security and Privacy, SP 800-53 Rev. 5, Security and Privacy Controls for Information Systems and Organizations, SP 800-53A Rev. 5, Accessing Security and Privacy Controls in Information Systems and Organizations, SP 800-53B, Control Baselines for Information Systems and Organizations, and NISTIR 8228, Considerations for Managing Internet of Things (IoT) Cybersecurity and Privacy Risks.
PEP launched the Privacy Engineering Collaboration Space in 2019 providing an open, virtual platform for practitioners to share, discuss, and improve upon open-source tools, solutions, and processes that support privacy engineering and risk management. The winning algorithms from NIST’s Public Safety Communications Research Division’s differential privacy challenges can be found on the platform among other differential privacy tools.
In 2020, NIST released the NIST Privacy Framework: A Tool for Improving Privacy through Enterprise Risk Management. The Privacy Framework, modeled on NIST’s highly successful Cybersecurity Framework, is a voluntary tool used to help organizations identify and manage their privacy risks. Jeewon Serrato, a partner at BakerHostetler, said that “if you need to establish a privacy program, the NIST Privacy Framework is a perfect place to start.” Others’ experiences with implementing the Privacy Framework can be found on the Privacy Framework Perspectives and Success Stories page.
So, what’s next for privacy at NIST? We heard from stakeholders that the privacy workforce is a priority, which is why PEP launched the Privacy Workforce Public Working Group (PWWG). The PWWG, with more than 600 members from across the globe, is in the process of defining tasks, knowledge, and skills aligned with the NIST Privacy Framework and the Workforce Framework for Cybersecurity (NICE Framework) to support the growth of a workforce capable of managing privacy risks. We’re also working on integrating guidance for privacy awareness and training programs into the upcoming revision of SP 800-50 Rev.1, Building a Cybersecurity and Privacy Awareness and Training Program.
PEP recently wrapped up a blog series focused on differential privacy, which provided basic concepts about differential privacy and applicable use cases to help privacy and IT professionals implement these tools. This blog series is serving as the foundation for more in-depth guidelines, with a draft anticipated to be released for public comment later this year. Meanwhile, NIST’s Privacy-Enhancing Cryptography Project is promoting the use of cryptographic protocols that enable parties to interact meaningfully without revealing private information to one another or to third parties. NIST is also collaborating with the White House Office of Science and Technology Policy and the National Science Foundation to advance privacy-preserving data sharing and analytics through bilateral prize challenges with the United Kingdom this year.
As we reflect on our history at NIST, it is important to recognize the strides we’ve made in protecting privacy. Today NIST is looked to for leadership on privacy, just as it is in many other domains. We’ve come a long way since the 1960s and 70s (and I’m not just talking about disco pants), but we’re not done yet!


