Principles
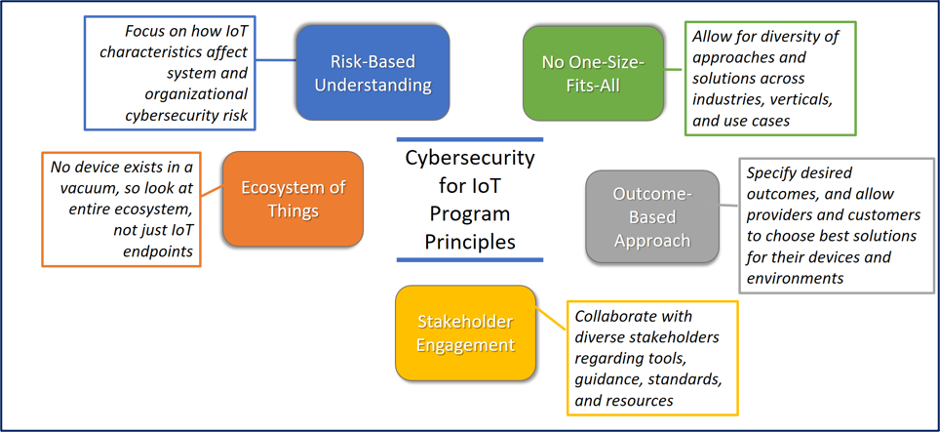
The Cybersecurity for IoT Program applies five principles to our efforts.
Some examples of our principles in practice:
- No One-Size-Fits-All
- NISTIR 8259 Series recommends 6 activities for manufacturers across IoT product life cycle
- Profiles of baseline recommendations created for different verticals/use case/types of devices
- Consumer IoT white paper identifies a candidate adaptation of NISTIR 8259A/B for Consumer Products in EO Response
- Ecosystem of Things
- Applying IoT Program Technical & Non-Technical Capabilities to NCCoE Projects
- Securing Telehealth Remote Patient Monitoring Ecosystem
- Protecting Information and System Integrity in Industrial Control System Environments
- Securing the Industrial IoT
- Mitigating Cybersecurity Risk in Telehealth Smart Home Integration
- Consumer Home IoT Product Security
- Outcome-Based Approach
- NISTIRs 8259 A and B provide outcome-focused recommendations for suppliers/ manufacturers of IoT products, support use case flexibility
- National On-Line Informative References (OLIR) program mappings demonstrate the outcome-focused approach, allowing for diversity of IoT cybersecurity solutions
- Risk-Based Understanding
- NISTIR 8228 helps organizations apply the Risk Management Framework and Cybersecurity Framework
- SP 800-213 Guides Organizations in Managing IoT Risk
- Stakeholder Engagement
- Over 150K Downloads of our 19 documents in 3 languages
- Over 1,700 Comments received
- Hosted 15+ Events with 3,000+ participants
Created November 9, 2021, Updated November 16, 2021

