Getting Started with CSF 1.1
Quick Start Guide
The quick start guide intends to provide direction and guidance to those organizations – in any sector or community – seeking to improve cybersecurity risk management via utilization of the NIST Cybersecurity Framework. Though the Cybersecurity Framework is not a one-size-fits-all approach to managing cybersecurity risk for organizations, it is ultimately aimed at reducing and better managing these risks. As such, this guide is intended for any and all organizations regardless of sector or size. Organizations will vary in how they customize practices described in this document. Organizations can determine activities that are important to critical service delivery and can prioritize investments to maximize impact.
The Quick Start Guide has been translated into Portuguese and Spanish.
Background
Recognizing the national and economic security of the United States depends on the reliable function of critical infrastructure, the President issued Executive Order (EO) 13636, Improving Critical Infrastructure Cybersecurity, in February 2013. The Order directed NIST to work with stakeholders to develop a voluntary framework – based on existing standards, guidelines, and practices - for reducing cyber risks to critical infrastructure. The Cybersecurity Enhancement Act of 2014 reinforced NIST’s EO 13636 role.
Created through collaboration between industry and government, the voluntary Framework consists of standards, guidelines, and practices to promote the protection of critical infrastructure. The prioritized, flexible, repeatable, and cost-effective approach of the Framework helps owners and operators of critical infrastructure to manage cybersecurity-related risk.
The Framework Core and Informative References are available as separate downloads in two formats: spreadsheet (Excel) , and alternate view (PDF). A companion Roadmap discusses future steps and identifies key areas of cybersecurity development, alignment, and collaboration.
The National Online Informative References (OLIR) Program is a NIST effort to facilitate subject matter experts (SMEs) in defining standardized online informative references (OLIRs) between elements of their documents, products, and services and elements of NIST documents like the Cybersecurity Framework Version 1.1, Privacy Framework Version 1.0, NISTIR 8259A, or NIST SP 800-53 Revision 5. The NIST Interagency or Internal Report (IR) 8278 - National Online Informative References (OLIR) Program: Program Overview and OLIR Uses focuses on explaining what OLIRs are, what benefits they provide, how anyone can search and access OLIRs, and how subject matter experts can contribute OLIRs.
To increase awareness, understanding, and use of the Cybersecurity Framework, NIST is highlighting brief "Success Stories" explaining how diverse organizations use the Framework to improve their cybersecurity risk management.
A listing of publicly available Framework resources can be found here. Resources include, but are not limited to: approaches, methodologies, implementation guides, mappings to the Framework, case studies, educational materials, internet resource centers (e.g., blogs, document stores), example profiles, and other Framework document templates.
NIST continues to welcome informal feedback about the Framework and Roadmap. Organizations and individuals may contribute observations, suggestions, examples of use, and lessons learned to cyberframework [at] nist.gov (cyberframework[at]nist[dot]gov).
What is the Framework?
The Framework is voluntary guidance, based on existing standards, guidelines, and practices for organizations to better manage and reduce cybersecurity risk. In addition to helping organizations manage and reduce risks, it was designed to foster risk and cybersecurity management communications amongst both internal and external organizational stakeholders.
Check out our Frameworks Basics FAQs section for further information.
An Introduction to the Components of the Framework
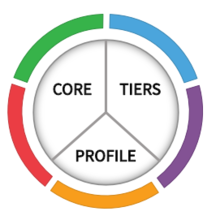
The Cybersecurity Framework consists of three main components: the Core, Implementation Tiers, and Profiles.
The Framework Core provides a set of desired cybersecurity activities and outcomes using common language that is easy to understand. The Core guides organizations in managing and reducing their cybersecurity risks in a way that complements an organization’s existing cybersecurity and risk management processes.
The Framework Implementation Tiers assist organizations by providing context on how an organization views cybersecurity risk management. The Tiers guide organizations to consider the appropriate level of rigor for their cybersecurity program and are often used as a communication tool to discuss risk appetite, mission priority, and budget.
Framework Profiles are an organization’s unique alignment of their organizational requirements and objectives, risk appetite, and resources against the desired outcomes of the Framework Core. Profiles are primarily used to identify and prioritize opportunities for improving cybersecurity at an organization.
To learn more about the Framework’s three main components, see the Components of Framework online learning module, or to learn more about the how organizations are using the Framework and its potential benefits, see the Uses and Benefits of Framework module.