CSF 1.1 Uses and Benefits of the Framework
This online learning page explores the uses and benefits of the Framework for Improving Critical Infrastructure Cybersecurity("The Framework") and builds upon the knowledge in the Components of the Framework page. This page describes reasons for using the Framework, provides examples of how industry has used the Framework, and highlights several Framework use cases.
Why Use the Cybersecurity Framework?
The Framework provides a common language and systematic methodology for managing cybersecurity risk. The Core includes activities to be incorporated in a cybersecurity program that can be tailored to meet any organization’s needs. The Framework is designed to complement, not replace, an organization's cybersecurity program and risk management processes.
The process of creating Framework Profiles provides organizations with an opportunity to identify areas where existing processes may be strengthened, or where new processes can be implemented. These Profiles, when paired with the Framework's easy-to-understand language, allows for stronger communication throughout the organization. The pairing of Framework Profiles with an implementation plan allows an organization to take full advantage of the Framework by enabling cost-effective prioritization and communication of improvement activities among organizational stakeholders, or for setting expectations with suppliers and partners. Additionally, Profiles and associated implementation plans can be leveraged as strong artifacts for demonstrating due care.
The Implementation Tiers component of the Framework can assist organizations by providing context on how an organization views cybersecurity risk management. The Tiers guide organizations to consider the appropriate level of rigor for their cybersecurity program. The Tiers may be leveraged as a communication tool to discuss mission priority, risk appetite, and budget.
Supporting Risk Management with the Framework
The Framework helps guide key decision points about risk management activities through the various levels of an organization from senior executives, to business and process level, and implementation and operations as well.
As pictured in the Figure 2 of the Framework, the diagram and explanation demonstrates how the Framework enables end-to-end risk management communications across an organization.
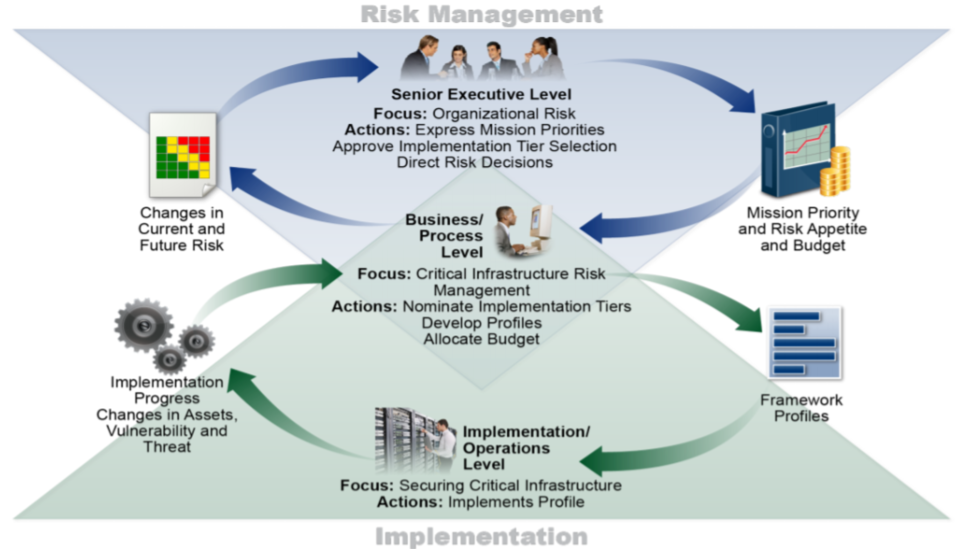
The executive level communicates the mission priorities, available resources, and overall risk tolerance to the business/process level. The business/process level uses the information as inputs into the risk management process, and then formulates a profile to coordinate implementation/operation activities. The implementation/operations level communicates the Profile implementation progress to the business/process level. The business/process level uses this information to perform an impact assessment. Business/process level management reports the outcomes of that impact assessment to the executive level to inform the organization’s overall risk management process and to the implementation/operations level for awareness of business impact.
Who should use the Framework?
The Cybersecurity Framework is for organizations of all sizes, sectors, and maturities.
While the Framework was designed with Critical Infrastructure (CI) in mind, it is extremely versatile.
With built-in customization mechanisms (i.e., Tiers, Profiles, and Core all can be modified), the Framework can be customized for use by any type of organization.
Because the Framework is outcome driven and does not mandate how an organization must achieve those outcomes, it enables scalability. A small organization with a low cybersecurity budget, or a large corporation with a big budget, are each able to approach the outcome in a way that is feasible for them. It is this flexibility that allows the Framework to be used by organizations which are just getting started in establishing a cybersecurity program, while also providing value to organizations with mature programs.
How are other organizations using the Framework?
Over the past few years NIST has been observing how the community has been using the Framework. These are some common patterns that we have seen emerge:
- Leadership has picked up the vocabulary of the Framework and is able to have informed conversations about cybersecurity risk.
- Organizations have used the tiers to determine optimal levels of risk management.
- Organizations are finding the process of creating profiles extremely effective in understanding the current cybersecurity practices in their business environment.
- Profiles and implementation plans are being leveraged in prioritizing and budgeting for cybersecurity improvement activities.
Examples from organization's using the Framework
Many organizations are using the Framework in a number of diverse ways, taking advantage of its voluntary and flexible nature. The section below provides a high-level overview of how two organizations have chosen to use the Framework, and offers insight into their perceived benefits.
To see more about how organizations have used the Framework, see Framework Success Stories and Resources.
NIST is always interested in hearing how other organizations are using the Cybersecurity Framework. Organizations are encouraged to share their experiences with the Cybersecurity Framework using the Success Stories page.
University of Chicago
The University of Chicago's Biological Sciences Division (BSD) Success Story is one example of how industry has used the Framework. BSD selected the Cybersecurity Framework to assist in organizing and aligning their information security program across many BSD departments.
BSD began with assessing their current state of cybersecurity operations across their departments. This consisted of identifying business priorities and compliance requirements, and reviewing existing policies and practices. This information was documented in a Current State Profile. BSD then conducted a risk assessment which was used as an input to create a Target State Profile. This Profile defined goals for the BSD cybersecurity program and was aligned to the Framework Subcategories. Finally, BSD determined the gaps between the Current State and Target State Profiles to inform the creation of a roadmap. The roadmap consisted of prioritized action plans to close gaps and improve their cybersecurity risk posture. The roadmap was then able to be used to establish budgets and align activities across BSD's many departments. The image below represents BSD's approach for using the Framework.
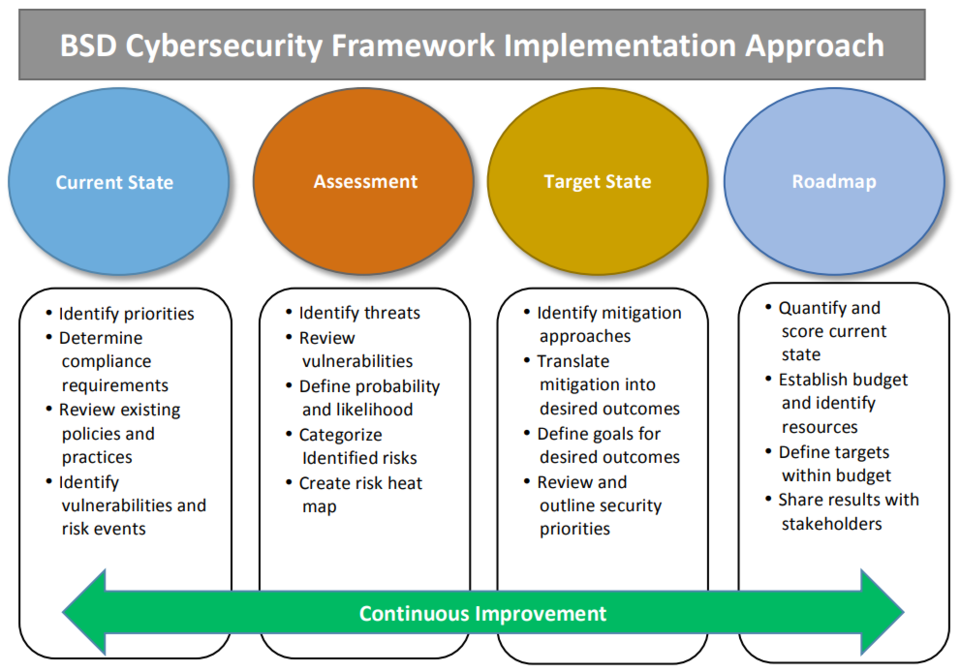
After implementing the Framework, BSD claimed that "each department has gained an understanding of BSD’s cybersecurity goals and how these may be attained in a cost-effective manner over the span of the next few years." BSD also noted that the Framework helped foster information sharing across their organization.
BSD recognized that another important benefit of the Cybersecurity Framework, is the ease in which it can support many individual departments with differing cybersecurity requirements. BSD said that "since the framework outcomes can be achieved through individual department activities, rather than through prescriptive and rigid steps, each department is able to tailor their approach based on their specific departmental needs."
To learn more about the University of Chicago's Framework implementation, see Applying the Cybersecurity Framework at the University of Chicago: An Education Case Study.
Intel
Intel used the Cybersecurity Framework in a pilot project to communicate cybersecurity risk with senior leadership, to improve risk management processes, and to enhance their processes for setting security priorities and the budgets associated with those improvement activities.
Because the Framework is voluntary and flexible, Intel chose to tailor the Framework slightly to better align with their business needs. Intel modified the Framework tiers to set more specific criteria for measurement of their pilot security program by adding People, Processes, Technology, and Environment to the Tier structure.
The graphic below represents the People Focus Area of Intel's updated Tiers. There are 3 additional focus areas included in the full case study.
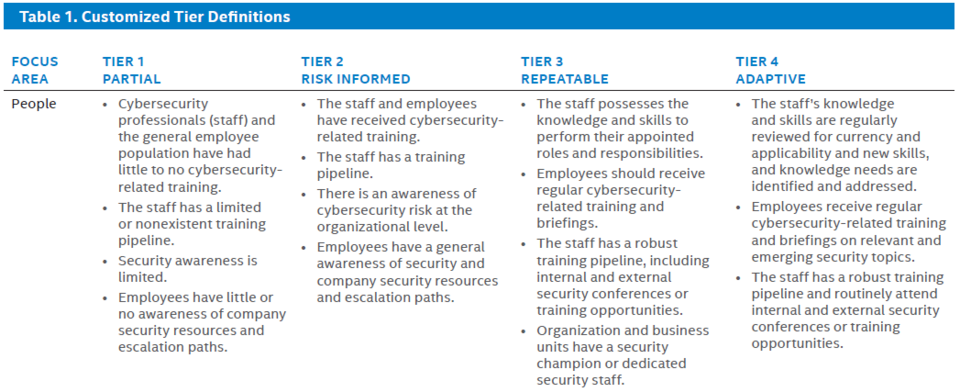
In addition to modifying the Tiers, Intel chose to alter the Core to better match their business environment and needs. For example, they modified to the Categories and Subcategories by adding a Threat Intelligence Category.
After the slight alterations to better fit Intel's business environment, they initiated a four-phase process for their Framework use.
Intel began by establishing target scores at a category level, then assessed their pilot department in key functional areas for each category such as Policy, Network, and Data Protection. These scores were used to create a heatmap. An illustrative heatmap is pictured below.
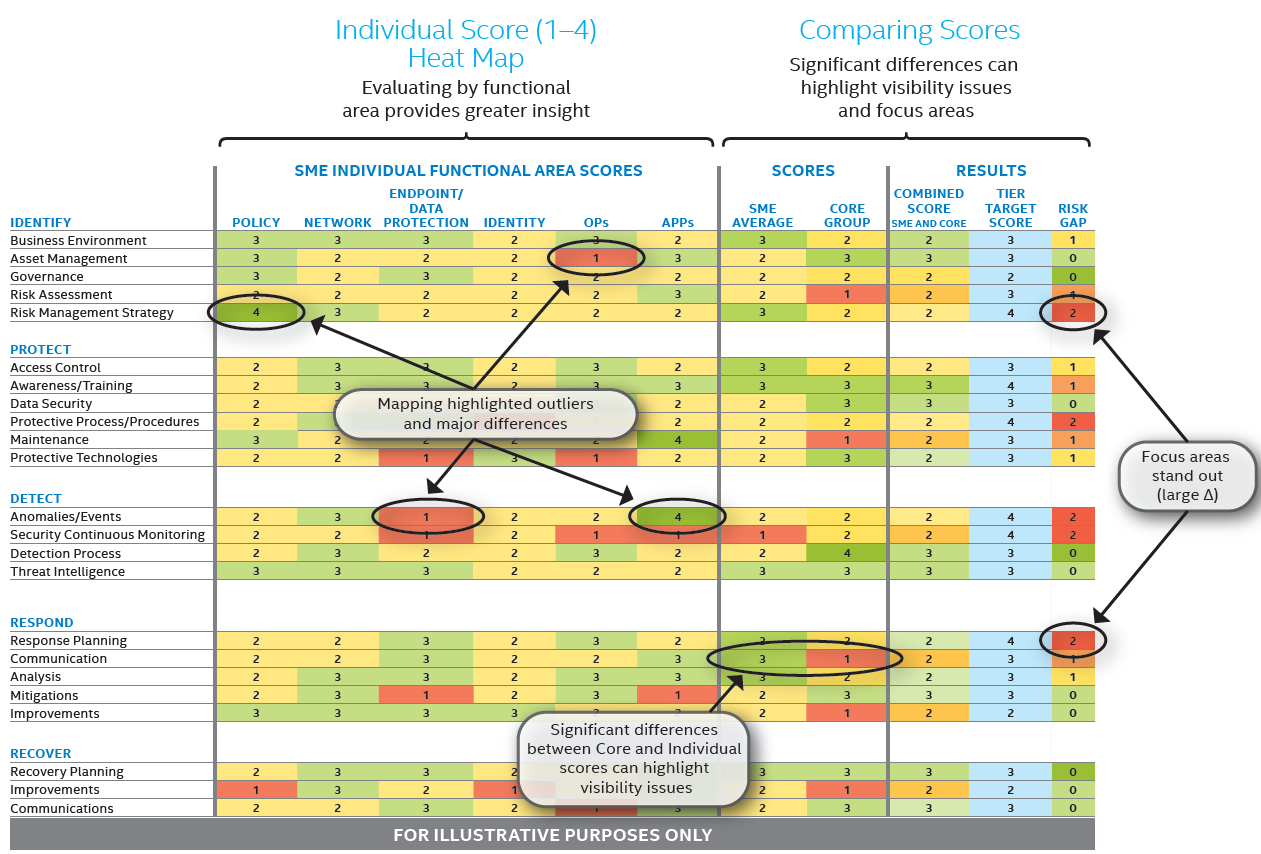
The resulting heatmap was used to prioritize the resolution of key issues and to inform budgeting for improvement activities.
After using the Framework, Intel stated that "the Framework can provide value to even the largest organizations and has the potential to transform cybersecurity on a global scale by accelerating cybersecurity best practices". They found the internal discussions that occurred during Profile creation to be one of the most impactful parts about the implementation. These conversations "helped facilitate agreement between stakeholders and leadership on risk tolerance and other strategic risk management issues".
Additional Resources
Uses_and_Benefits_of_Framework.pptx (PPTX | 1.6 MB)

