Cybersecurity Insights
a NIST blog
As we celebrate Data Privacy Day 2020, let’s take a moment to reflect on the changes to privacy as a discipline — not just here at NIST, but as a community. A decade ago, conversations among privacy professionals seemed stuck in debates about the meaning of privacy, whether the Fair Information Practice Principles (FIPPs) were still viable in a world of Big Data and emerging technologies like Internet of Things and artificial intelligence, and why privacy-enhancing technologies (PETs) were not being widely adopted. The idea of privacy risk management was just a twinkle in our collective eye.
Today we understand much better how important process is to realizing privacy protections in our information technology systems, products, and services. It’s not enough to simply have principles, legal requirements, and PETs; we’ve had to follow the path that security experts set out upon many years before to figure out how to embed security in systems and business development processes. When NIST launched its Privacy Engineering Program six years ago, it was to mixed support among stakeholders. Now, privacy systems management standards have been or are being developed in global consensus-based bodies (for example, ISO/IEC 27701, ISO/PC 317, IEEE P7002), the International Association of Privacy Professionals launched a Privacy Engineering Section, and new conferences are emerging such as Privacy Engineering Practice and Respect demonstrating that the demand is there. The release of Version 1.0 of the NIST Privacy Framework: A Tool for Improving Privacy through Enterprise Risk Management is a milestone in this journey.
It’s About the Journey
And what a journey it’s been! Through roughly a year of open collaboration with stakeholders from across government, academia, and industry, we have worked to craft and hone a tool to help organizations better identify, prioritize, and manage privacy risks to protect individuals’ privacy. To everyone who showed up ready to dig into content at workshops, wrote pages of thoughtful feedback, engaged with us during countless roundtables and briefings, and helped us spread the word about this effort: we thank you. We are incredibly grateful for your contributions.
We knew things were going to be different at the first workshop when we didn’t get bogged down in discussions of definitions of privacy and personal data (or personally identifiable information or personal information). It’s been our goal to make the Privacy Framework agnostic to laws and regulations, which are the source of many of these variant terms and to take a risk-based approach. Using the more generic term of data has allowed us to achieve both these goals. Organizations can still layer on specific legal definitions that may govern the environment they operate in, but taking a general approach allows a much broader range of organizations to use the Privacy Framework to apply a risk-based approach that considers the context within which data is processed and how that context may change over time.
The communication discussion continued in the second workshop where we learned that, notwithstanding our efforts, the discussion draft hadn’t quite hit the mark in terms of bridging the way legal and policy professionals talk about privacy and the language of engineers. In the iterations that followed, we worked to smooth that transition and demonstrate the connection between principles and methods of implementation rather than simply create one more restatement of the FIPPs. As we framed it at our third workshop, we want everybody in an organization to be able to find themselves in the Framework Core.
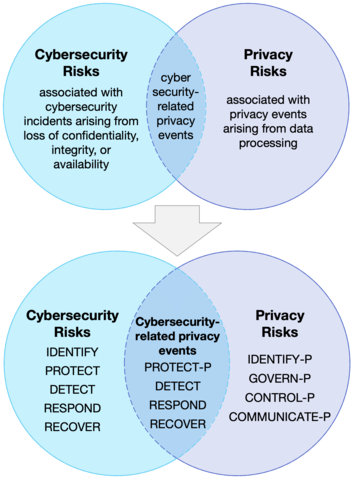
That third and final workshop of the development journey was a fantastic, down-in-the-weeds discussion of how to better align privacy and cybersecurity within organizations, both conceptually and process-wise. This discussion allowed us to continue to improve the foundational Venn diagram that we have been using to express the relationship between privacy and cybersecurity. It culminated in a new Venn diagram to demonstrate different ways that organizations could use the Privacy Framework and the Framework for Improving Critical Infrastructure Cybersecurity (aka, the NIST Cybersecurity Framework) to better manage privacy and cybersecurity risk collectively.
The comments on the preliminary draft confirmed for us that our efforts to respond to the varied stakeholder discussions were on track, and more importantly, that there is a growing appetite for more guidance on privacy risk management. As we begin 2020, our thoughts have shifted to adoption and the resources that will be needed to advance not only the use of the Privacy Framework, but privacy engineering and risk management more broadly.
The Real Fun Begins with Adoption
We appreciate all of the privacy leaders that began using the Preliminary Draft of the Privacy Framework last year. A big thank you also to those who are now sending along questions, feedback, and supportive statements. Please keep it coming!
One of the best ways to help the community is to share what you know in the new Resource Repository we just launched. We’re looking for crosswalks between the Privacy Framework and privacy laws, regulations, standards, and frameworks; common profiles; guidance on best practices; and tools to support implementation. These resources are critical to transforming the Privacy Framework from a simple document to an actual working tool.
As we noted above, the Privacy Framework is just one milestone in a never-ending journey. There are many challenges for organizations in achieving their privacy objectives, some of which we’ve called out in a companion Roadmap. Over the next year, we’ll be out and about at various events and would love to continue the conversation with stakeholders to support adoption and advance priority areas from the Roadmap. Visit our website for more information about where to engage with us or how to provide feedback, and sign up for our mailing list for periodic updates.
If you’d like to learn more, join tomorrow’s NIST Privacy Framework Webinar: Ready, Set, Adopt Version 1.0 at 1 p.m. Eastern time (a recording will be posted afterwards).
It’s been a blast creating this tool with all of you — and we look forward to working together to make sure the Privacy Framework continues to evolve to meet your needs in the coming decade. We can’t wait to recount how we’ve progressed as a community for Data Privacy Day 2030, but until then: Happy Data Privacy Day 2020!
About the author
Related Posts
Comments
Awesome my takeaway "it’s been our goal to make the Privacy Framework agnostic to laws and regulations, which are the source of many of these variant terms and to take a risk-based approach." It's all about risk, and the cost of risk impact, risk optimization, mitigation or acceptance. Looking forward to more...






Very interesting and most importantly relevant topic!
Entirely and fully support !!!