Auditing Use Case
READ-ONLY SITE MATERIALS: Historical voting TWiki site (2015-2020) ARCHIVED from https://collaborate.nist.gov/voting/bin/view/Voting
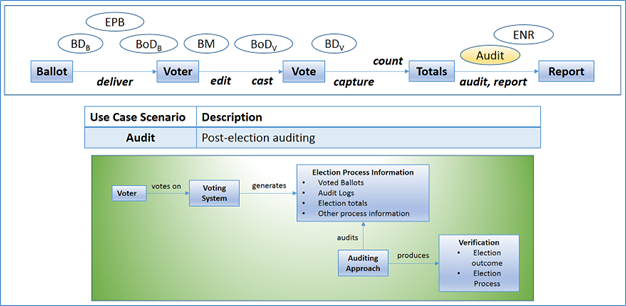
The most essential purpose of post-election auditing technology is to verify election outcomes as well as how those outcomes were produced. Typically, this may be done in a completely offline manner.
A full recount occurs in the case when every voter-verified ballot that was properly cast is recounted for a given election. Such a process may be employed as a means for checking whether or not originally reported outcomes and recounted outcomes are the same. To perform full recounts is a lengthy, manual, and potentially error-prone process.
To provide evidence for the correct outcome more efficiently, one may perform various kinds of audits, such as risk-limiting audits, which do not necessarily require a full recount, but are designed to limit the risk of an incorrect election outcome when given an appropriate (representative, random) sample of an election’s voter-verified/cast paper ballots. The sample size typically depends on the reported margin of victory in the contest. If cast vote records (CVR) that can be efficiently associated with paper ballots are available, a risk-limiting audit may be performed at the ballot level by comparing the CVR to the paper ballot. If batch tallies can be easily linked to the relevant paper ballots, then multiple-ballot (batch) level comparison auditing may also be performed. If tallies can't be easily linked to the ballots they report on (e.g. if only precinct result reports are available, but ballots for a given precinct are scattered across many days of mail-in ballot batches), then a ballot polling audit can be performed.
This use case may also provide the opportunity for discussion of additional auditing types or approaches as well. Different auditing approaches may make use of different kinds of election process information and utilize different strategies in order to establish their conclusions. For example:
- evidence-based elections require good evidence that the chain of custody of the paper ballots has been securely preserved.
- targeted auditing of specific audit units (individual ballots, precincts, batches or other auditable collections of ballots) based on timely reporting of results by audit unit, mark density information in Cast Vote Records, indications of breaches in chain of custody, and other evidence or claims that the audit unit deserves scrutiny
- poll book accounting or ballot reconciliation processes compare evidence of how many voters showed up at the polls or properly returned their ballots and cast votes, with the number of ballots counted. Discrepancies should be investigated, documented and factored into the overall assessment of the evidence. Secure and auditable methods of preserving event logs that document voter authorization, signature verification, ballot casting, ballot counting, etc. can be used to facilitate these forms of accounting.
- security checks can be performed on seals, seal logs and surveillance tapes, and event logs can be checked for anomalies
More information is available at
- Evidence-Based Elections: Stark and Wagner, IEEE Security and Privacy, 2012.
- Principles and Best Practices for Post-Election Audits - 2008
- Risk-Limiting Post-Election Audits: Why and How Risk-Limiting Audits Working Group, October 2012 (version 1.1)
Use Case Scenarios
WHAT | Verify election results
HOW | Scenarios
- Recount - Typical-offline, manual: Fully, manually recount all voter-verified and cast ballots
- Risk-limiting audit
- ballot-level comparison auditing
- Multiple-ballot (batch) comparison auditing
- Ballot polling audit
- Ballot accounting audit
- Chain of custody checks
- Security checks
Request for Feedback
For each use case scenario, please address these questions:
- Is the use case scenario in scope for the Next Generation VVSG for development of requirements that will undergo testing and certification? or
- Is the use case scenario in scope to develop as guidelines for election officials and voting system manufacturers? or
- Is the use case scenario not in scope for this work?
- If different parts of the use case scenario fall in 1., 2., and/or 3. Please identify as such.
- Is anything missing?
Voting TWiki Archive (2015-2020): read-only, archived wiki site, National Institute of Standards and Technology (NIST)
ARCHIVE SITE DESCRIPTION AND DISCLAIMER
This page, and related pages, represent archived materials (pages, documents, links, and content) that were produced and/or provided by members of public working groups engaged in collaborative activities to support the development of the Voluntary Voting System Guidelines (VVSG) 2.0. These TWiki activities began in 2015 and continued until early 2020. During that time period, this content was hosted on a Voting TWiki site. That TWiki site was decommissioned in 2020 due to technology migration needs. The TWiki activities that generated this content ceased to operate actively through the TWiki at the time the draft VVSG 2.0 was released, in February of 2020. The historical pages and documents produced there have been archived now in read-only, static form.
- The archived materials of this TWiki (including pages, documents, links, content) are provided for historical purposes only.
- They are not actively maintained.
- They are provided "as is" as a public service.
- They represent the "work in progress" efforts of a community of volunteer members of public working groups collaborating from late 2015 to February of 2020.
- These archived materials do not necessarily represent official or peer-reviewed NIST documents nor do they necessarily represent official views or statements of NIST.
- Unless otherwise stated these materials should be treated as historical, pre-decisional, artifacts of public working group activities only.
- NIST MAKES NO WARRANTY OF ANY KIND, EXPRESS, IMPLIED OR STATUTORY, INCLUDING, WITHOUT LIMITATION, THE IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, NON-INFRINGEMENT AND DATA ACCURACY.
- NIST does not warrant or make any representations regarding the correctness, accuracy, reliability or usefulness of the archived materials.
ARCHIVED VOTING TWIKI SITE MATERIALS
This wiki was a collaborative website. NIST does not necessarily endorse the views expressed, or concur with the facts presented on these archived TWiki materials. Further, NIST does not endorse any commercial products that may be mentioned in these materials. Archived material on this TWiki site is made available to interested parties for informational and research purposes. Materials were contributed by Participants with the understanding that all contributed material would be publicly available. Contributions were made by Participants with the understanding that that no copyright or patent right shall be deemed to have been waived by such contribution or disclosure. Any data or information provided is for illustrative purposes only, and does not imply a validation of results by NIST. By selecting external links, users of these materials will be leaving NIST webspace. Links to other websites were provided because they may have information that would be of interest to readers of this TWiki. No inferences should be drawn on account of other sites being referenced, or not referenced, from this page or these materials. There may be other websites or references that are more appropriate for a particular reader's purpose.

