Taking Measure
Just a Standard Blog

Last year I provided a number of simple steps to lower the risk to your online presence without making your life harder. This year, I'm focusing on making logging into your accounts easier.
First, I'm going to share the takeaways from our new password guidance. Simply put: Use passphrases, not passwords.
Then, I'm going to explain the absolute most important thing to know about passwords: Try not to use them at all. And if you do, don't rely on passwords, or even passphrases, alone.
Work smarter, not harder
I've been a runner for a long time. A few years ago, I found myself in a really bad rut. I was under a lot of stress, so I had trouble sleeping. When I woke up, I’d be exhausted, so I'd sleep in a half hour. Because I was starting later in the morning, it would be hotter, so I'd run a little slower. Running slower meant more time would pass, so it would get even hotter, so I'd cut off a mile, but doing that made me disappointed in myself, which added to my stress and ended up making me even more exhausted.
After a while, I finally realized I wasn't helping myself.
Running was supposed to build me up, body and spirit, but I was in a cycle that was tearing both down. I changed the cycle to let my emotional and physical conditions dictate my running, not the other way around. Soon after, I was running longer, faster, more consistently, and with fewer injuries. I broke the cycle by having the way I function drive my training, and the results were unambiguously positive.
This may seem like a forced analogy, but that is the basic approach to change NIST took in rewriting its password guidance.
Over the years, our reliance on passwords, and the ease with which our adversaries can defeat those passwords, resulted in a negative feedback loop where users were subjected to increasingly complex, stressful and exhausting composition rules (upper, lower, and special characters, oh my!), increasing length requirements, password rotation requirements, and on and on.
Like pounding out more and more miles faster and faster, these looked like gains on paper but undermined the outcome we wanted: a safer and more convenient online experience.
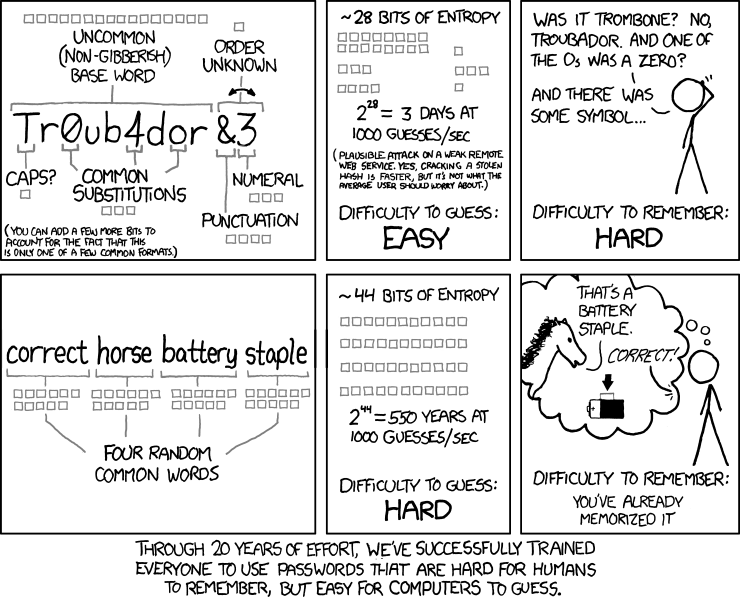
As this XKCD comic points out, complex password rules actually drive us to create predictable, easy-to-guess passwords (“password1!” anybody?) or find other ways to make things easier on ourselves, e.g., reusing passwords across sites or saving them in spreadsheets or sticky notes. In practice, all those rules had made it easier for the bad guy, and harder—and less secure—for the user.
Our task: Find a better way
This summer, after a lengthy process with continual collaboration from government and industry, NIST released an update to Special Publication (SP) 800-63 to address the many changes that digital identity has undergone during that document's decade of existence. You can read more about that groundbreaking process here.
Among the huge number of things we wanted to do with the update was to give people guidance that would help them come up with passwords that were easy for them to remember, but hard for attackers to compromise. While the math of what makes a strong password hasn’t changed in theory, data from the past several years has revealed much about how people think about and cope with computer security. It was these human factors that served as the foundation for our recommendations.
So, without further ado, here are three simple steps to building a better password:
Step 1: Leverage your powers of association
The first lesson is about how humans remember. We're not particularly good at rote memorization. We're much better at remembering by association. Here's a simple example: Is it easier to remember the 20th letter of the alphabet or the letter that comes after “s”? As children, we didn't learn to associate a letter with the number of its corresponding place in the alphabet. What most of us learned was the alphabet song. The song helped us build associations between one letter and the next, with the upshot being that now we couldn’t forget our ABCs if we wanted to. Similarly, most of us rattle off our siblings’ names by their ages, likely oldest to youngest, months from January to December, and the planets from Mercury to Neptune (sorry, Pluto).
With a password composed of a random set of characters, there is, by definition, no association between one character and the next. Since “x” doesn't have a natural association with “&,” it's harder for us to memorize them.
Instead, we should use passphrases. Passphrases leverage things that we know are paired, like the letters in a word. Our brains are so good at recognizing groups of letters that form words that we don't even process the letters individually. If you look at the word “apple,” you don't say to yourself, “A-p-p-l-e, oh that's apple!” Your brain simply recognizes the word as a single image and converts it into a real-life image of the thing it represents—the classic red apple with a single green leaf on its stem, a bushel of granny smiths, or, for me, the perfect vector for peanut butter.
This ability to convert characters to words and words to images gets us to our second and third steps.
Step 2: Make the associations unique to you
So, we've established that, at least for password purposes, memorizing an entire word is no harder than memorizing a single letter. But we don't want to just replace 12-character passwords with 12-word passphrases—that would be a nightmare to type.
Instead, choosing just a handful of normal words or phrases can work, as long as whatever associates those words in your mind are known only to you.
Examples of bad passphrases: The names of your four kids; the colors of the rainbow; the Cavs starting lineup in game seven of the 2016 NBA finals when they came back from a 3-1 deficit and beat the Warriors to win Cleveland's first major sports championship in 52 years and then returned to The Land to be greeted by a giant parade attended by more than a million people … but I digress.
Instead, passphrases should be words that can go together in your head, but no one else would ever suspect. An example from my kitchen: “blender vent sauté pendant red chair.” These words all make sense, and they aren't even all things. Verbs work just as well.
Even if someone knew I picked words based on my kitchen, they would need to see my kitchen and then determine which of the thousands of nouns and verbs I picked. So, from a hacker's perspective, it really is random.
All we have to do now is remember it. This brings us to our last step.

Step 3: Picture this
Here's where we get to use our brain's strengths again. Back to the apple example from step 1, we know our brains like to picture things, and we can use this to advantage.
Those words about my kitchen—blender vent sauté pendant red chair—happen to be visible to me from right to left as I sit at my dining room table. Again, a hacker wouldn't know that, but, no matter where I am, I can always close my eyes and see that image. Even if I rearrange my kitchen or move to a different house, I can easily conjure that image just as it was.
In short, make your passphrase a picture in your head.
Compared to a password like “uE*s3P%8V)”, I think it's pretty clear passphrases can improve usability. But are they really better for security?
The savings add up
I won't get deep into the math here, but suffice it to say that a decent passphrase is decidedly stronger than a 10-character password made of a mess of letters, numbers and symbols.
The basic idea is that, once you've put a hacker in the position of having to guess, you want them to have to make as many guesses as possible. At some point, it's costly enough—in time or computing power—that the hacker will give up, or not even bother in the first place.
Depending on which special characters you allow and a few other factors, the random 10-character password would have something like 65 bits of entropy, a measure of its strength. For the passphrase, even if the hacker knows there are exactly six English words of 5-11 letters each, and given the average American has a vocabulary of about 19,000 such words, the passphrase would have about 85 bits of entropy.
A bit of fancy math on how entropy relates to the required number of guesses shows that it would take about 1,050,000 times more effort to crack the passphrase. Yes, that's over 1 million times stronger—1 million times longer guessing time to crack.
It's not even close.
THE MOST IMPORTANT PART
Here's the thing about passwords and passphrases: They're both pretty bad no matter how you create them. That said, we still live in an online world dominated by passwords. They are static and knowable, meaning they are stored somewhere. If they’re stored somewhere, they can be stolen, and if they're stolen, they can be used by the thief. Passphrases are harder to guess, and we continue to make them harder to steal, but, by their very nature, neither passwords nor passphrases will ever be good enough to protect sensitive accounts on their own.
So, even though our new guidance should yield more usable and more secure passphrases, to safeguard those things that you really care about, you need to rely on something other than passphrases alone. I said it a year ago, and I’ll say it again: Turn on multi-factor authentication to protect your personal information!
The future, which is already here
Increasingly, we're seeing technologies that enable password-less login while appropriately mitigating risk. Some of our largest industry partners are moving in this direction already. We're incredibly optimistic that more forward-looking organizations will continue to adopt and improve these methods and that one day we'll finally move beyond the password. But ramping up takes time, and we can't let the promise of tomorrow keep us from making gains today.
Turn on multi-factor authentication, create passphrases instead of passwords, and see how working smarter, not harder, can make your life easier and more secure.
Read all about the updated NIST SP 800-63, Digital Identity Guidelines, here and here.
*Post edited 21 May 2018 to reflect that Neptune, not Uranus, is the farthest planet from the Sun
About the author
Related Posts
Comments
Thanks for your comment. I agree, too many sites are using the old approach. But many are changing. Our new guidance means more federal agencies should be changing soon. We hope to see private entities doing the same. I encourage you to email, post, tweet, etc., to let service providers that haven't changed know that you're paying attention. Like anything, it takes time to transition--but a nudge never hurts! And, please, turn on MFA whenever you can.
When I'm forced to provide a "minimum of 8 letters + 1 numeral + 1 symbol" password, I munge the lyrics from songs I know and love. For example, a line from Nirvana's Teen Spirit goes;
"Come as you are, as you were / As I want you to be"
Which I turn into; Caur,auw/A1wutbe.
I find that once I start singing (silently!) the song, the letters etc. just pop into my head.
thats nirvanas come as you are, not teen spirit
WHILE I AGREE AND USE PASSPHRASES ON A FEW IMPORTANT SITES AND HAVE HAD THE SAME PROBLEM AS "CHEVYONE" RELATES YOU MENTION USING A PASSWORD MANAGER. IF YOU DO THIS I FIND IT EASIER THEN COMING UP WITH A LOT OF DIFFERENT PASSPHRASES. I USE THE MAXIMUM ALLOWED TO CREATE THE PASSWORD SO I HAVE INCREASED MY PASSWORD STRENGTH AND DON'T HAVE TO REMEMBER MUCH. ADDITIONALLY, I HAVE FOUND THAT MOST SITES THAT USE MFA REQUIRE YOU TO HAVE A SMARTPHONE TO SEND THE CODE TO. I DON'T USE A SMARTPHONE SO I CAN'T GET MFA ON MANY SITES. GRANTED IT WILL TAKE TIME TO GET COMPANIES TO MAKE THEIR SITES BETTER PROTECTED, BUT WITH SO MANY SITES HACKED AND OUR INFO STOLEN FROM THEM, NO MATTER HOW HARD WE WORK TO PROTECT OURSELVES WE GET BLOWN OUT OF THE WATER BY COMPANIES THAT DON'T CARE ABOUT PROVIDING ADEQUATE SECURITY FOR THEIR CUSTOMERS. MAYBE IF THE GOVERNMENT OR WE COULD SUE THEM FOR THEIR LACK OF CARE IT MIGHT MOVE THEM QUICKER TO IMPROVE. THE INTERNET IS ONLY GOING TO GET BIGGER AND MORE COMPLEX AS TIME GOES ON.
I am regular reader of your blog and no doubt it all stuff is awesome. The best thing about your sharing and posting is that you always provide content that is helpful for both the newbie and experts.
there is an amazing reference site on how secure your password is google password haystacks by trusted security expert Steve Gibson
I have 50 sites requiring username/passwords related to work, probably over 100 at home, all with different requirements of length, special characters or not. I don't care how many familiar images I conjure up and use to recall my passwords or pass phrases, there is no way to remember all these and have room for the work at hand. I do scientific research. I want to fill my brain with signaling pathways and discoveries related to ameliorating disease. Passphrase or password, I will need to write them all down somewhere. Now based on NIST guidance our company is instituting a passphrase policy. It will take longer to login, but it is not going to be easier to remember....Please someone develop a cheap iris scanner, to replace the need for passwords!!!
it's called a fingerprint scanner. no need for retinal ID; and unless you've seen too many movies or procedural TV series where the detective or secret agent picks up your fingerprint off a drinking glass, etc -- it's pretty darn secure. which is why most smartphones have them now.
the trick is to have your agency invest in software which will utilize data gathered from fingerprint readers; and of course, all that costs money upfront, so...
I think the retinal scanner is a bit impractical and far-fetched for average-security 2018 work. [of course, retinal scans have been popularized in many movies and fictional scenarios involving "top secret access", but most of those are point-of-presence scanners -- which makes sense in those situations; not logging onto a database or secure website using a retinal scanner to match up data.]
maybe by 2020, I'll be proven wrong.
@Memory Overload
Use a password manager
just a tiny tiny factual correction here Mike Garcia -- Uranus is not the furthest planet out from the Sun. Discounting Pluto of course, it's actually Neptune. You might want to edit your otherwise well-written article to reflect that. Cheers.
Whoops! We appreciate your attention to detail and will make that change right away!
Certainly helpful !
Am I missing something? Isn't this scheme vulnerable to dictionary attacks? You seem to be using random words but real words in the dictionary. Also, your character set is just the alphabet.
I always understood that using English words (or any other language real words) and just alphabetic characters was a poor scheme vulnerable to brute force attacks. This is why site requires upper and lower case and special characters.
The idea is that the character set is the collection of 19,000 words in the given length range that an average person knows, from which only 6 characters are chosen. 6 choices from the 19,000 possibilities is what gives the author's estimate of 85 bytes of entropy. Of course you can also consider an attacker randomly trying combinations of the 55 sub-characters likely to be used (A-Z a-z <comma> <period> and <space>). The long length of individual characters that passphrases give actually makes this more difficult, over 200 bytes, assuming 6 words with 6 characters each on average.
That said, using only one or two words from the dictionary, or any common phrase, would be a bad idea. The words need to be chosen in a way that at least seems random to someone who doesn't know how you chose them (choosing truly randomly (or pseudorandomly) actually also gives much more memorable passphrases than many traditional passwords with symbols, numbers, etc). Good to be skeptical though!
Sorry, bytes > bits.
Not helpful- Sorry
Clicked on this link to find out the rules - i.e. CAPs, Lower case, number, character, etc. and all it gave me was how to create a password.
Could you use a (silly)sentence, or is that too predictable?
I think we need to do away with passwords and start doing finger prints and retina eye scans
I agree with doing away with passwords
I wasn't expecting an article about passwords to be so entertaining! Very informative too
Thank you for your help
Our word recognition is actually quite independent from any visual images they conjur for you.
In fact, your experience isn't as universal as you think: People with aphantasia CANNOT conjure up an actual visual picture in their "mind's eye". Yet word associations or even creating art are far from out of reach for them.
The funniest part is explaining to someone with aphantasia that it wasn't all metaphorical, all their life, when people talked in a way that takes visualization for granted.
Oh and while we're at it: Your "inner voice"? Same concept. Not universal.
good information on pass phrases. using a password manager solves all issues. not sure why someone wouldn't, unless work wont allow or provide one. trying to remember password doesnt make sense.
Thank you
good
This is great.
I’ll try to remember lol
Great information
Very helpful





I love your ideas, however, many sites have asked for 12- 20 characters with X number of caps, small, numbers, punctuation. I have tried to do what you have recommended and all I get is error messages. Maybe someday these organizations will learn.
Perhaps I can forward this article to them. No, that won't work-they would have to change their programming!
Thanks and have a FUN day!