Cybersecurity Insights
a NIST blog
Privacy and NIST are in the headlines today and in good way! We are delighted to announce the release of the Preliminary Draft of the NIST Privacy Framework: A Tool for Improving Privacy through Enterprise Risk Management for public comment.
Since our kickoff workshop in October 2018, in Austin, Texas, we put out a Request for Information and we’ve been traveling around the country conducting a series of workshops and roundtables to listen to stakeholders about their challenges with protecting privacy and how we can develop the Privacy Framework into a tool that will help. This Preliminary Draft is the result of these conversations. Our goal was to deliver a tool that could help organizations communicate better about privacy risks when designing and deploying products and services, provide more effective solutions that can lead to better privacy outcomes, and facilitate compliance with their legal obligations. Now it’s your turn to let us know if we met that goal.
Of course, it wouldn’t be as much fun if there wasn’t a little excitement during the development process. Robust discussions about how to describe the relationship between privacy and cybersecurity took center stage. How do we bring privacy risk management into parity with cybersecurity risk management, as well as with organizations’ broader enterprise risk portfolios? How do we address the overlap between data security and privacy breaches in cost-effective and practical ways? Where does the Cybersecurity Framework play a role?
OK, it’s not exactly cage match material, but if we want to make meaningful progress on optimizing beneficial uses of data while minimizing adverse consequences for individuals (or society as a whole) we need to grapple with these issues. From the get-go, we heard from stakeholders a desire to model the Privacy Framework structure after the Cybersecurity Framework such as using the construct of the Core with its high-level Functions, and increasingly granular set of protection activities and outcomes. But there were mixed responses on whether the Privacy Framework and the Cybersecurity Framework should have overlapping Functions with respect to data security, so we decided to workshop it. We proposed two options for the Privacy Framework Core to discuss at our third workshop in Boise, Idaho: one option included Functions from the Cybersecurity Framework to address data security, while the other did not.
Spoiler alert: If you’re looking for the big reveal on which Core we selected, we’re sorry to disappoint you, but this is a drama free zone! Although the views were pretty evenly split on the Core options, stakeholders felt strongly about their preferences because they reflected how closely their organizations collaborated on privacy and cybersecurity, and the maturity of their privacy programs. These reasons told us that we should design the Core to meet organizations where they are today and provide the flexibility to allow them to “choose their own adventure” when it comes to using both frameworks. To demonstrate this flexibility, we’ve created the following Venn diagram, mirroring the one we’ve been using to describe the relationship between privacy and cybersecurity (see section 1.2.1 of the Preliminary Draft).
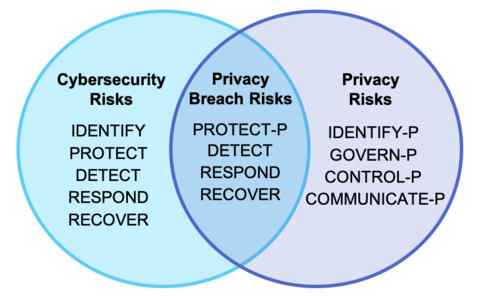
As presented in the Preliminary Draft, there are five Functions in the Privacy Framework: Identify-P, Govern-P, Control-P, Communicate-P, and Protect-P, where the -P distinguishes privacy focused activities versus cybersecurity ones. The first four can be used to manage privacy risks arising from data processing, while Protect-P can help organizations manage privacy risks associated with privacy breaches along with Detect, Respond, and Recover from the Cybersecurity Framework. Protect-P is not the only way to manage privacy risks associated with privacy breaches. Alternatively, organizations could use all of the Cybersecurity Framework Functions in conjunction with Identify-P, Govern-P, Control-P, and Communicate-P to collectively address privacy and cybersecurity risks.
At NIST, we believe in the importance of collaboration between privacy and cybersecurity teams. That’s why we’ve been working to integrate privacy into our cybersecurity guidance. Special Publications 800-37 Rev. 2, Risk Management Framework for Information Systems and Organizations: A System Life Cycle Approach for Security and Privacy, 800-53 Rev. 5 (draft), Security and Privacy Controls for Federal Information Systems, and 800-63 Rev. 3, Digital Identity Guidelines are all good examples of our efforts to date. But as noted above, we also recognize that it’s important to build a tool that is usable regardless of an organization’s structure. We realize that this flexibility comes at a cost of some complexity. Therefore, we plan to continue to discuss the best way to encourage more collaboration while simplifying our approach to our various frameworks.
So far, developing the Privacy Framework has been a true pleasure because of the fantastic engagement of our stakeholders. Although reaching version 1.0 will really just be the first of many milestones, if you’ve joined in the journey already, thank you! If you haven’t yet, don’t miss this opportunity to share your feedback with us.
We will be accepting public comments on the Preliminary Draft through October 24, 2019. Submission instructions can be found here. If you would like to learn more about the Preliminary Draft, please join our NIST Privacy Framework Webinar: Ready, Set, Comment on the Preliminary Draft on September 17, 2019 (a recording will be posted afterwards). We’ll also be out and about at various events over the next few months – visit our website for more information about where to engage with us or privacyframework [at] nist.gov (reach out) to learn more about becoming an early adopter of the Privacy Framework. Happy reviewing!


