Cybersecurity Insights
a NIST blog
All aboard: the NIST Cybersecurity for IoT Program is headed to our next stop! Share your input on where we’re headed during our Future Directions Two-Day Workshop on March 31st.

Workshop Details…
We’re looking forward to hearing from the community during our “Future Directions” Workshop!
Date: March 31 - April 1, 2026
Where: NIST’s Gaithersburg campus!
Registration and Details: HERE
Can’t make it? We still want to hear from you – email us at IoTSecurity [at] nist.gov (IoTSecurity[at]nist[dot]gov).
All Aboard for Product Cybersecurity
The NIST Cybersecurity for Internet of Things (IoT) Program was established to help real-world practitioners navigate the gray areas between IT and connected products. This provides clarity when it comes to challenges, available existing resources, and understanding where we can provide further guidelines (to help fill in the gaps). Our IoT Program Principles are founded in the understanding that: no product operates in a vacuum, desired outcomes and usability have to drive approaches, and there’s no one-size-fits-all approach.
Underlying all this is the understanding that connected products differ from traditional IT. This has implications for their use, as well as how they must be secured. We’re seeking to better understand which IoT needs and considerations are most relevant to which specific stakeholders — and provide practical guidelines with a common language to manage connected products. To understand where to go next, it’s important we understand where we are, and how we got here…
Our Path Here
Since our start in 2017, the NIST IoT Program's mission has been to cultivate trust in IoT and foster an environment that enables innovation on a global scale through standards, guidelines, and related tools. We've created this “metro map” (see image below) to help illustrate how our publications fit together.
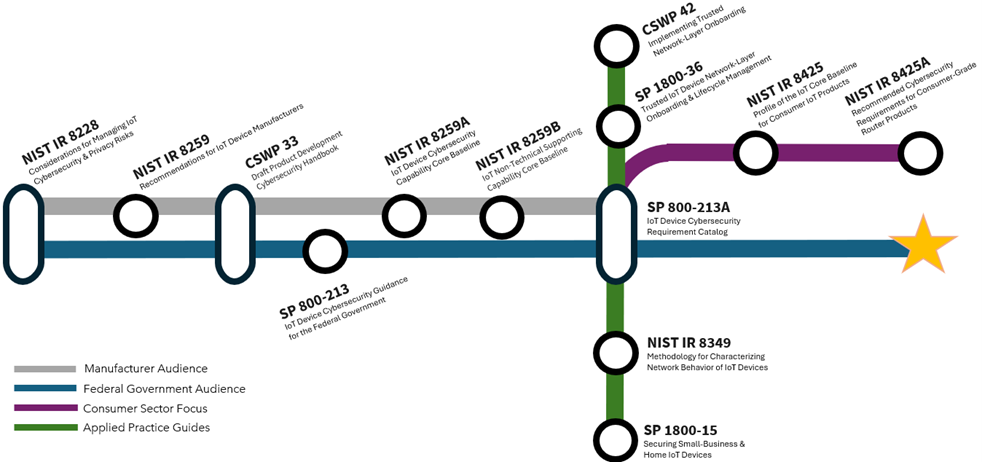
While this may not be the precise 1:1 model you’d expect from NIST, we think it works to directionally show how our publications connect and have built upon one another; this is not strictly chronological. The “transfer points” show where there is an overlap of audiences.
One of our earliest publications was NISTIR 8228, Considerations for Managing IoT Cybersecurity and Privacy Risks, illuminating for federal agencies (and other organizations) how IoT products differ from traditional IT, common themes seen across organizations, and the need to protect product security, data security, and individual privacy. From there, we continued along our "Blue Line" and "Silver Line" to focus on enabling innovation through: (1) working with IoT product manufacturers on securing products, and (2) working with federal practitioners to understand their needs, both for mission support and service delivery, as well as technical and regulatory needs.
Over time, these have moved towards more applied practice guides, running along our "Green Line," and consumer-focused resources on our "Purple Line." Of course, federal audiences, and a wide range of associated stakeholders (e.g., owners and operators of critical infrastructure with IoT products in the ecosystem and manufacturers selling to federal agencies) have always remained a priority.
We Are Here: Today & Future Directions
As for the yellow star? We are here! But where is here, exactly?
We have been hearing that stakeholders would like help understanding how to approach securing their IoT products and systems, given the large range of documentation available. This often becomes an academic exercise, like “homework” on top of their already busy job of managing technology to support mission needs and efficient use of cybersecurity resources.
We’re working to identify broadly applicable considerations for developing and securely deploying IoT products across sectors and use cases – and to extend NIST’s work to consider the cybersecurity of IoT product components beyond the IoT products. We understand the need to be agile and consider the needs of the product, the environment it’s deployed in, and how the two interact. Ultimately, the goal is to provide useable, common language approaches to manage IoT products based on the context of their use.
We are currently completing updates to NISTIR 8259, Foundational Cybersecurity Activities for IoT Device Manufacturers and NIST SP 800-213, IoT Device Cybersecurity Guidance for the Federal Government: Establishing IoT Device Cybersecurity Requirements. We encourage you to weigh in on these documents on day one.
And of course – we want to hear from you on workshop day two, where we’ll specifically ponder these questions:
- What would be most usable for cyber practitioners and policymakers? What formats or resources would help alleviate the “homework” challenge?
- How do emerging technologies impact these considerations, as these connected products must be operated (and secured) within the enterprise? How does the rate of change impact your approach?
- How do you see network connectivity facilitating next-level behaviors and risks?
- How do we approach real world use cases, including the ongoing need for a human-in-the-loop?
- How does context impact the use – and security implications – for products within your ecosystem? What about for different stakeholders in your organization/ecosystem?
- Is there value in approaching product security from the angle of decision-making and physical impact (beyond immediate systems and the digital space)?
See you at the Station: Workshop Details
We’re looking forward to hearing from the community during our Workshop in Gaithersburg, MD on March 31 - April 1, 2026!
Note: Day one is mainly focused on NIST SP 800-213 updates. Day two explores our next steps. If you can't make it, we still want to hear from you; please email us at IoTSecurity [at] nist.gov (IoTSecurity[at]nist[dot]gov).


