Summary
ITL’s Internet Infrastructure Protection (IIP) program, led by the Advanced Network Technologies Division (ANTD), works with industry to develop the measurement science and new standards necessary to ensure the robustness, scalability, and security of the global Internet. The research focuses on the measurement and modeling techniques necessary to understand, predict, and control the behavior of Internet-scale networked information systems. ITL staff use these insights to guide the design, analysis, and standardization of new technologies aimed at improving the robustness of the Internet’s core infrastructure. Recent efforts have focused on enhancing the security of the Internet’s Domain Name System (DNS), Border Gateway Protocol (BGP), and Electronic mail (Email) and messaging infrastructures. In addition, the IIP program addresses other systemic vulnerabilities in core Internet technologies such as those that enable massive scale Distributed Denial of Service (DDoS) attacks.
Description
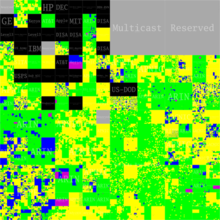
In the FY 2016 ITL staff made significant contributions in the design, standardization, test and measurement of technologies to improve the security and robustness of the Internet’s global routing protocol BGP. NIST staff are key contributors to Internet Engineering Task Force (IETF) standards to add cryptographic validation to BGP (see, https://tools.ietf.org/html/draft-ietf-sidr-bgpsec-protocol/), and to address robustness issues associated with large scale routing policy violations (see, https://www.rfc-editor.org/rfc/rfc7908.txt). In addition, NIST developed and released an open source reference implementations of these emerging IETF specifications, on-line test tools to foster their adoption and measurement systems to track their operational deployment. Below is a visualization generated by once such monitoring tool, of the emerging global structure of the Resource Public Key Infrastructure (RPKI). The RPKI has been designed to provide the trust infrastructure upon which Internet routing security technologies can be based.
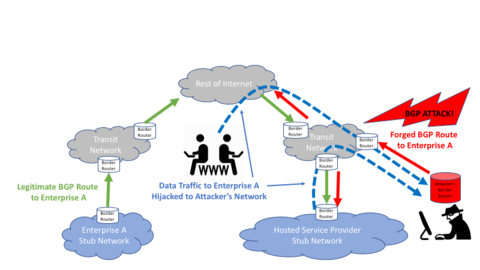
In FY 2016, as technology specifications and implementations matured, ITL staff began a series of outreach efforts with the networking industry to increase the understanding, and foster adoption, of these new BGP security mechanisms. ITL staff organized and led a workshop at the June North American Network Operators Group (NANOG) meeting aimed and addressing the practical issues, state of vendor support and existing operational experience with emerging BGP security technologies (see, https://www.nanog.org/meetings/abstract?id=2846). ITL staff also initiated a nationwide BGP security pilot deployment project with the Internet2 research and education community.
ITL’s High Assurance Domains (HAD) project aims to leverage NIST’s previous successes in the development and deployment of Domain Name System Security (DNSSEC) technologies, to enable scalable solutions other long standing Internet security issues. In FY 2016 the project focused on addressing the issues of Email phishing attacks and developing scalable techniques to enable cryptographic protection of Email message exchanges. NIST published NIST SP 800-177 Trustworthy Email, a comprehensive guidance on the deployment and use of emerging DNS-based authentication mechanisms to combat Email phishing and spam. In addition, ITL developed and deployed on-line test tools to assist network operators in the configuration and verification of their deployment of emerging anti-phishing technologies.
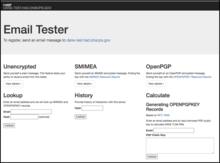
The second area of focus for the HAD project in FY 2016 was the advancement of specifications, implementations and deployment of IETF Domain-based Authentication Named Entities (DANE) technology that leverages a secured DNS as a ubiquitous key discovery and management infrastructure. In FY 2016 ITL staff contributed to the development of IETF DANE specifications and developed distributed test and measurement tools to assist in their adoption and use in the global internet. Figure below shows the user interface to the recently released NIST DANE test system that enables product developers and network operators to test their use of the DANE technologies to store, retrieve and validate various types of cryptographic keying material for end-to-end Email security, and for general transport layer security (TLS) for web and other applications.
HAD project staff also collaborated in the NCCoE DNS-Based Secured Email project (see, https://nccoe.nist.gov/projects/building_blocks/secured_email) which tested and produced detailed deployment guidance for commercial implementations of DANE-based server-to-server security for Email transport.
ITL staff in Advanced Distributed Denial of Service (DDoS) Mitigation Techniques project, are working with the community to document and quantitatively characterize the applicability, effectiveness and impact of various approaches to filtering spoofed Internet Protocol (IP) traffic st
reams and then to develop consensus recommendations and deployment guidance that can drive their adoption in Federal network environments and throughout the Internet industry. In FY 2016 NIST staff developed benchmarking methodologies to characterize the performance implications of various techniques to block spoofed IP packets in commercial routers and developed draft deployment guidance for these mechanisms in a variety of network interconnection scenarios.
In addition to understanding the barriers to deployment and adoption of existing DDoS mitigation techniques, ITL staff began research and evaluation of new, scalable means of DDoS detection and mitigation based upon Software Defined Networking (SDN) technologies. NIST will research and develop the measurement science necessary to meaningfully characterize and test the behavior, performance and robustness of emerging NFV/SDN technologies. Our particular focus will be metrics and techniques to measure the safety and security of NFV/SDN networks at scale and the ability of such networks to meet strict performance requirements Leveraging the capabilities above, NIST will examine the potential for NFV/SDN technologies to contribute significantly to other high priority programs. NIST will explore two such domains in the first two years: software defined Internet of Things (IoT) networking and novel uses of SDN for network security.
In FY 2017 the major milestones for Internet Infrastructure Program will include:
- Completing publication of IETF standards for BGP security and increasing outreach and pilot deployment activities to foster commercial deployment of these technologies.
- Continuing to develop and mature DANE specifications and technologies for scalable key management in the Internet and conducting research in their applicability to emerging problems domains such as authentication in consumer networks.
- Publishing NIST guidance on current DDoS mitigation techniques and continuing to research and develop new approaches based upon emerging SDN technologies.
Major Accomplishments
Robust Inter-Domain Routing Project: https://www.nist.gov/programs-projects/robust-inter-domain-routing
NIST RPKI Deployment Monitor and Test System: https://www.nist.gov/services-resources/software/nist-rpki-deployment-monitor-and-test-system
BGP Secure Routing Extension (BGP‑SRx) Prototype: https://www.nist.gov/services-resources/software/bgp-secure-routing-extension-bgp-srx-prototype
BRITE - BGPSEC / RPKI Interoperability Test & Evaluation System: https://www.nist.gov/services-resources/software/brite-bgpsec-rpki-interoperability-test-evaluation-system
High Assurance Domains Project: https://www.nist.gov/programs-projects/high-assurance-domains
NIST SP 800-177 Trustworthy Email: http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-177.pdf
NIST DANE Test System: https://dane-test.had.dnsops.gov/
Advanced DDoS Mitigation Techniques Project: https://www.nist.gov/programs-projects/advanced-ddos-mitigation-techniques
Software Defined Virtual Networks Project: https://www.nist.gov/programs-projects/software-defined-virtual-networks

