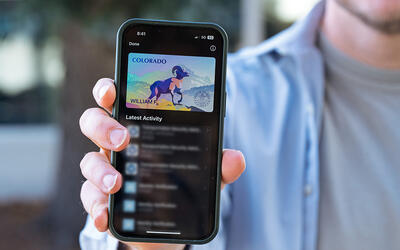
On August 1, 2025, NIST released Digital Identity Guidelines, (Special Publication 800-63, Revision 4), which intends to respond to the changing digital landscape that has emerged since the last major revision of this suite was published by NIST in 2017.
Identity and Access Management is a fundamental and critical cybersecurity capability. Simply put, with its focus on foundational and applied research and standards, NIST seeks to ensure the right people and things have the right access to the right resources at the right time.
To advance the state of identity and access management, NIST
- Conducts focused research to better understand new and emerging technologies, their impact on existing standards, and the implementation of identity and access management solutions;
- Leads in the development of national and international identity and access management standards, guidance, best practices, profiles, and frameworks to create an enhanced, interoperable suite of secure, privacy-enhancing solutions, including authentication and authorization within the Internet of Things (IoT);
- Evolves its identity and access management standards, guidelines and resources; and
- Produces example solutions that bring together the identity management and cybersecurity requirements needed to address specific business cybersecurity challenges.
Through this Identity and Access Management Resource Center, we seek to share our efforts that strengthen the security, privacy, usability and interoperability of solutions that meet an organization’s identity and access management needs throughout the system lifecycle.
Other Recent Updates:
- New Supplement - Incorporating Syncable Authenticators Into NIST SP 800-63B, Digital Identity Guidelines — Authentication and Lifecycle Management
- Blog | Giving NIST Digital Identity Guidelines a Boost: Supplement for Incorporating Syncable Authenticators
- Draft Identity and Access Management Roadmap
- View recordings from NIST's three-part Digital Identity Guidelines Webinar Series