Taking Measure
Just a Standard Blog

Huh? What? At least that was my response the first time I heard the words “zero trust” when I started working at the National Institute of Standards and Technology (NIST) National Cybersecurity Center of Excellence (NCCoE) in the fall of 2018. Mind you, I was also making a fresh start with an enormous jump to cybersecurity from a career track that had generally been in software engineering. Sure, I did design and develop secure software solutions and even put together secure systems and platforms at times throughout my career, but zero trust seemed like a different ballgame to me. For one thing, it didn’t have a fence.
What do I mean by that? Well, the traditional approach to cybersecurity relies upon barriers — firewalls — that control traffic coming in and out of a network. Zero trust, on the other hand, is about assuming no barriers. It is usually mentioned in the same breath as “removing perimeters,” “shrinking perimeters,” “reducing perimeters” or “going perimeter-less.” These are common references to the idea of “de-perimeterization,” which was originally introduced by a group called the Jericho Forum back in 2005. Then in 2010, cybersecurity expert John Kindervag coined the phrase “zero trust” while he was with Forrester Research. In a nutshell, zero trust assumes that the system will be breached and designs security as if there is no perimeter. Hence, don’t trust anything by default, starting with the network.
We’ll get into what zero trust means for cybersecurity in a minute. But first, how did NCCoE — and I — get wrapped up in zero trust? Well, it’s kind of a long story.
A Big Breach Starts the Ball Rolling
I will dare to argue that the coup de grâce was the Office of Personnel Management (OPM) data breach of 2015. An estimated 22.1 million records were exposed! And if you aren’t shaking your head right about now, you should be, as it has been described as one of the largest breaches of U.S. government data in history. It exposed records of people who had undergone background checks, as well as information about their family, friends and acquaintances, many of whom weren’t even government employees. Social Security numbers, names, dates and places of birth, and addresses were among the types of personally identifiable information that were revealed.
The OPM data breach was a big wake-up call for the U.S. government to secure its information systems and infrastructures. In its aftermath, several initiatives were launched to improve and modernize the U.S. government’s security posture. The American Technology Council, formed in May 2017 under the direction of the president, promptly coordinated and produced a report for federal IT modernization later that year.
Then, a year later in February 2018, the CIO Council Services, Strategy, and Infrastructure Committee, made up of federal IT officers, chartered the Zero Trust and Software-Defined Networking Steering Group. That group’s job was to support the adoption of more effective methods and technologies for verifying, securing, enforcing and continuously monitoring access to the federal government’s assets and data by applying zero trust principles. The group convened a workshop on October 25, 2018, at the NCCoE. The workshop included 21 representatives and subject matter experts from federal civilian and defense agencies alike to discuss and come to consensus on definitions of zero trust networking and software-defined networking, including components, functional capabilities and security characteristics of each model. Shortly after the workshop, I came to work at NIST/NCCoE and was asked to participate in the steering group meetings as the new technical lead. This interaction finally led to the February 2019 launching of a NIST NCCoE project in partnership with the CIO Council to research zero trust and zero trust architectures (ZTA) with the goal to produce a general guidance document for adoption of ZTAs for securing U.S. government information systems and infrastructures.
In August 2020, NIST NCCoE released the general guidance document NIST SP 800-207, Zero Trust Architecture, for adoption of ZTAs in the federal government. This is a document that provides conceptual-level insight for zero trust and zero trust architectures, including deployment models, use case scenarios and discovered gaps in technologies.
Now, with the historical backdrop out of the way, let’s refocus our attention on our main topic: zero trust and what it means for cybersecurity.
Keeping Networks Safe, Then and Now
The best way to quickly get your mind wrapped around zero trust is to consider traditional and present network environments. People who have been in the IT field since the earliest days will surely remember the more innocent times in which we put together network environments. They were immensely different to say the least, as we didn’t have remotely accessible resources or applications and services in the cloud like we do today. Sure, we used digital resources and applications to do our work; however, they were exclusive to internal networks and accessible to staff who were on PCs and laptops within those network environments. How did we protect them from internet threats? We threw a digital fence — a perimeter — around them, which funneled external accesses through a single point of entry in a verified and authorized manner. This would allow the internal users access to the pool of resources and applications protected inside the perimeter. And this was a sound strategy for a long time.
Today, with the explosion of cloud computing, we are more globally connected than ever before. Most of us conduct business remotely using mobile devices. We consume, exchange and store digital information in private clouds, public clouds, hybrid clouds and many other variations in between. Needless to say, the conventional boundaries have expanded and become more obscured to allow for a much larger footprint of applications and services to be located and accessed from anywhere. Of course, with that expansion, the cybersecurity vulnerabilities have also grown. We now have more areas and points of attack. And we are especially vulnerable to the types of cybersecurity breaches that originate from inside the networks — inside the perimeter.
In fact, in the case of infamous OPM data breach I mentioned above, hackers first gained access to OPM’s internal network using stolen credentials and then planted a malware package that installed itself within OPM’s network as a back door for data exfiltration. From there, attackers escalated their privileges to gain access to various OPM information systems, a typical escalation scenario that is often referred to as the “lateral movement” or “East-West traffic” of a security breach inside the perimeter. The shortcoming with the conventional perimeter defense is that it provides no security control mechanism to prevent lateral movements once the security threat is inside the perimeter, as inside is always considered to be the safe or trusted zone in this strategy.
This is where zero trust comes in to save the day. You could be working from an enterprise-owned network, a coffee shop, home or anywhere in the world, accessing resources spread across many boundaries, from on-premises to multiple cloud environments. Regardless of your network location, a zero trust approach to cybersecurity will always respond with, “I have zero trust in you! I need to verify you first before I can trust you and grant access to the resource you want.” Hence, “never trust, always verify” — for every access request!
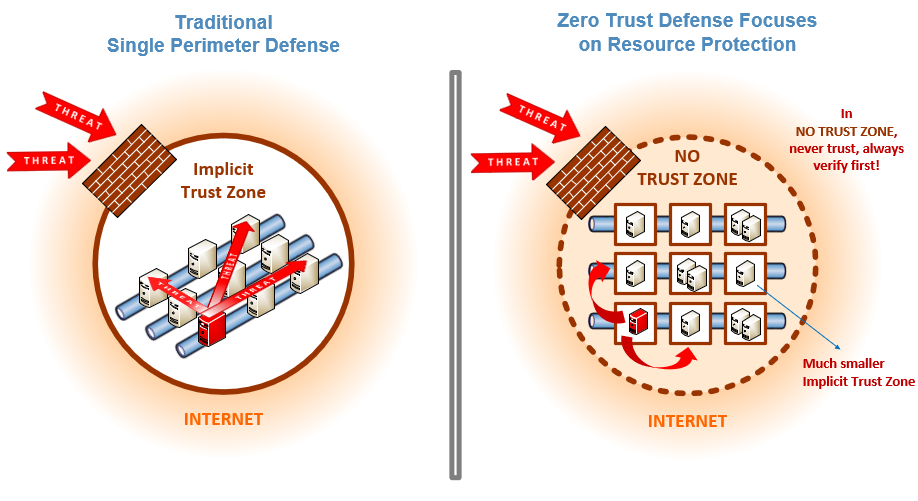
And to stress the point further, the verification process is one of the key aspects of zero trust approach. Every access request to a resource must be thoroughly evaluated dynamically and in real time based on access policies in place and current state of credentials, device, application and service, as well as other observable behavior and environmental attributes, before access may be granted. For example, a member of staff or a contractor, or even a guest user, may be verified and granted access to a specific resource, but they will still need to be reverified to access another resource within a zero-trust-enforced environment. This continuous scrutiny is the security control mechanism that prevents lateral movement of bad actors spreading from compromised systems within network environments, which is basically the essence of any zero trust solution.
I’ve had many amazing working experiences throughout my career, but I have to admit, this experience with our zero trust efforts at NIST/NCCoE definitely tops the chart by far. And what’s really even more gratifying is that our zero trust efforts are being closely followed and highly regarded by other government agencies and many in the industry. And for that, all the kudos go to every member of my team for their awesome support in our zero trust efforts and activities.
About the author
Related Posts
Comments
Great blog article. Love the style of story telling to convey a complex topic of zero trust into easy understandable and digestible.
Zero trust at all that's not bad
I agree 100% in the term, "no trust". I have now learned by cyber attack on every aspect of my life that you now have to check, recheck, and continually check by the hour of every day if the certificates are valid. If you do nothing, you will become a victim of cyber security and you will lose everything, in the blink of an eye! The Global World needs to be aware of this.
Good morning Mr. Kerman. First thank you for sharing such an important blog I read carefully all your efforts and experience, I can only say "Honestly" Kudos to you and the rest of your team to work on this "Priority Task" that we need so desperately. I know the Government and NIST management will be pleased to see this document to his full completion. Every one in the IT business should not only read but understand what ZTA means. Congratulations !! We can not forget that Code of Ethics goes hand in hand with ZTA effort. Thank You.
Very interesting way to explain a useful security concept. Never trust but verify is best answer to inherently insecure systems and services
I think something like zero-trust is part of Linux/Ubuntu. I hope the Feds are aware of this.
how to counter high tech serveillance to ensure zero trust cybersecurity
Zero Trust has shifted from a niche concept to a foundational cybersecurity strategy - and this article captures that evolution perfectly. As traditional perimeters dissolve and threats grow more sophisticated, “never trust, always verify” is no longer optional. Continuous authentication, least-privilege access, and strong east–west traffic controls are exactly what modern networks need to stay resilient.





The implementation of never trust, always verify the access to the system. A network would need to subdivided within a VLAN into specific group type or individual systems with a AI/smart firewall and encryption ticket within the message traffic to verify authorization or need to access that system. Other words using the "something you have, something you know, and something you are"; so the message protocol would have to provided these items.