Taking Measure
Just a Standard Blog

They say opposites attract. While my husband and I have many important things in common, we are complete opposites in one area. He’s a “risk taker,” and me … well, not so much. Rather than being labeled as “risk averse,” I prefer the term “caution giver.”
I’m a federal employee. I come from a long line of public servants. I bet that my ancestors probably worked in the service of the king or queen, or at least the local earl or baron, before they came to the U.S. My husband is different story. He’s a small-business owner. Whereas I tend to worry and ask a lot of “what if?” questions, he likes the challenge of being in command and building his business.
In my role as NIST’s Cybersecurity for Small Business Outreach Lead, I’ve met many small-business owners, and most have similar personalities to my husband. They have incredible drive and an unrelenting spirit. Small business owners see opportunities where “caution givers” like me only see risk.
While it might be in your nature to be a risk taker, cybersecurity is one area where you need to listen to the caution givers. Many small businesses might not have the resources to employ an entire IT security team, and that makes them especially vulnerable to attack. Not to fret, though, (leave that up to me) there are some simple things you can do now to help manage cybersecurity risks to your small business.
Train Your Employees
Your employees should know the company policy on computer use. Can they use social media on their work computers? Social media is a great way to interact with your customers and grow your business, but hackers can also use it to do social engineering, potentially fooling your employees into giving away information that they could use to hurt your business’s reputation or even steal from you.
What kinds of applications can they download and use? That free game may be fun to play during your lunch break, but what else is it doing? Games and other “free” applications you find online are a common way that hackers can gain access to computer systems. Only let your employees install applications from trusted sources and only when they need that application to do their work.
How do they handle information that may be sensitive to the business such as tax or payroll information? Your employees need to know that they should not send out sensitive information through unencrypted email.
Aside from these proactive steps, your employees need know what to do when a security incident occurs.
Stay Up to Date
Even the best software isn’t perfect, and hackers are constantly looking for ways to exploit those imperfections. Thankfully, software designers and security researchers are also constantly working to correct those imperfections and plug the holes in their products, so be sure to update your software regularly.
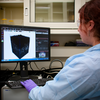
Install and Activate Software and Hardware Firewalls
Firewalls can block unwanted traffic such as malicious emails or browsing to “blocked” websites. You should install a hardware firewall between your small business’s internal network and the Internet.
Secure Wireless Access Point and Networks
If your small business uses wireless networking, make sure that you change the administrative password that was on the device when you bought it. Set the wireless access point so that it does not broadcast its Service Set Identifier (SSID).
Only access wireless networks that you trust and are certain of their security. That free Wi-Fi in the coffee shop may be convenient, but is it secure?
Require Individual User Accounts and Strong Passwords
Each user should have their own individual account and password. Users should not share their passwords with anyone including other employees. Administrative privileges should be limited to a few employees. Your employees should have access only to those systems that they need to do their jobs. Limiting administrative privileges will prevent them from installing unauthorized software. Require your employees use strong passwords and train them on how to select a strong password.
Set Up Web and Email Filters
When you are selecting an email provider make sure they offer filtering for inappropriate messages. Use web browsers that allow web filtering to keep your employees from accessing malware-infected websites.
Make Full Backups of Important Business Data/Information
Do a full, encrypted backup of every computer and mobile device at least once a month. Do this shortly after a complete virus scan. Store your backups away from the office in a protected place, so that if something happens at the office, your data is safe.
Be CyberAware
So, I know that if you’re a small business owner, chances are that you’re a risk taker, too. It only makes sense. But take it from a caution giver, there are some things that you shouldn’t take risks with no matter what, and cybersecurity is one of them. By following these steps, you can steel yourself against attacks and security incidents. And if you’re looking for a more detailed, model cybersecurity blueprint, check out the NIST Cybersecurity Framework and Small Business Information Security: The Fundamentals.
And be careful out there!
*Edited Nov. 28, 2016
About the author
Related Posts
Comments
- Reply