Taking Measure
Just a Standard Blog

Cybersecurity, at this point in the technological age, has become a household word. Every week, almost like clockwork, it seems there is a story on the news about a newly discovered hack or data breach often made possible by poor cybersecurity practices. Many of these incidents are focused around stolen data, which resides in our IT, or information technology, infrastructure. However, the breaches that interest me are those that affect the systems and devices that monitor and manipulate much of the world around us and have real-world health and safety consequences if they are compromised. These extremely important systems and devices are known as operational technologies, or OT.
Typically hidden in plain sight, OT controls many of the processes we rely on every day, including traffic signals, power distribution, hydroelectric dams, water treatment, building HVAC, oil and gas distribution, nuclear power plants, and many varieties of manufacturing. Again, the most important characteristic of OT is their ability to reach out from the digital world and manipulate the physical world where we humans reside. It’s not difficult to imagine some of the disasters that could occur if these critical OT processes were to be compromised because of poor cybersecurity practices.

So, how do these systems manipulate the physical world? At the most basic level, they’re not much different from my coffee maker, whose proper function I rely on for my proper function every morning.
Inside the coffee maker there is a tiny computer, a series of valves and heating elements that work together to create, in my opinion, the most delicious and invigorating elixir the world has ever known. If the computer failed to manage the coffee-making process, the consequences can vary from simple disappointment, e.g., no coffee because the water was never heated, to catastrophic, e.g., the heating element stayed on all day, caught fire and burned down my house. The same is true for more elaborate OT systems, like manufacturing machines and robots, which can include thousands of sensors and actuators.
So, what’s the problem with securing these devices? Well, not so long ago, OT systems were built using proprietary hardware and software and their operational details were not well known. Today, however, OT leverages many of the same technologies that were originally created for IT, e.g., networking, the internet, operating systems, user management, USB ports and web servers. Because of this shared technology, it’s easy to assume that any type of cybersecurity technology could be implemented to protect OT, but this is not the case.
For example, cybersecurity devices that filter unauthorized network traffic on an IT network could cripple an OT network simply by preventing important data from reaching its destination, and, in some cases, can cause failures just by delaying data. Software used to scan a network for vulnerabilities may send unfamiliar messages to OT devices and can cause them to fail, which is especially bad if the device is actively controlling a process. Even something as simple as antivirus software can have a detrimental impact on the performance of these critical systems and may be impossible to implement altogether.
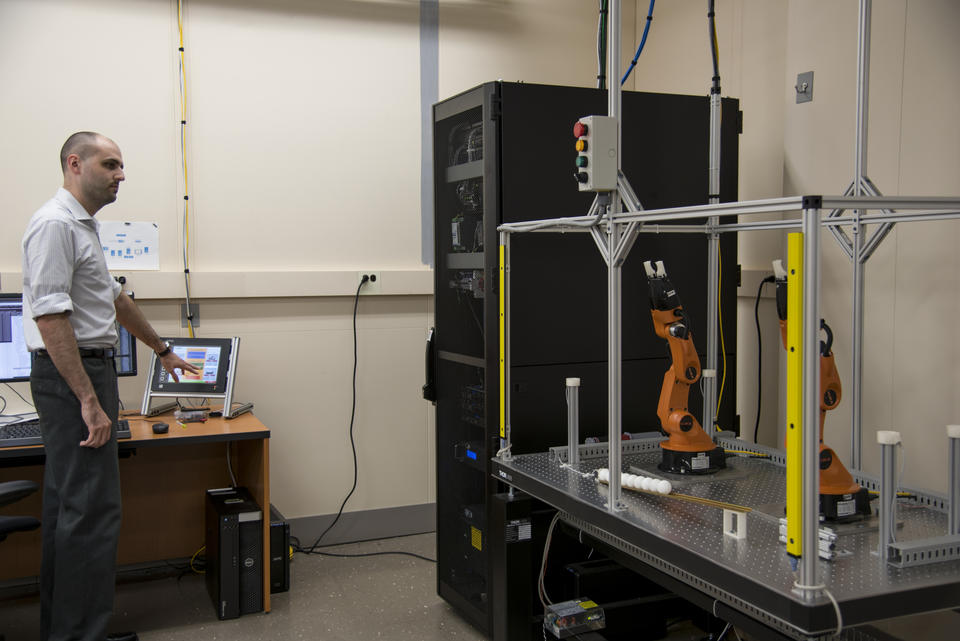
This is where our research begins. In our laboratory testbed, we install, integrate and test these cybersecurity technologies on emulated manufacturing systems. We have all the parts and pieces to reproduce manufacturing systems in the lab, including identical industrial controllers, network hardware, human-machine interfaces and even robots. The main difference between our testbed OT and the real manufacturing processes are the additional measurement devices we use to evaluate their operational characteristics.
Standards and guidelines detailing best practices for protecting IT and OT have already been produced by industry, trade groups and government agencies. However, one thing they are missing is guidance that describes how to balance those protections with potential negative impacts they may have on performance. To fill this gap, my group is working to produce guidelines, test methods, metrics and tools based on measurement science and standards to give industry the confidence it needs to effectively apply cybersecurity protections on their systems without negatively affecting their performance, safety or reliability. Our work has already resulted in a manufacturing profile for the Cybersecurity Framework, which outlines a risk-based approach to help manufacturers implement, manage and improve their cybersecurity posture using industry standards and best practices. And to put the manufacturing profile to the test, we will be using it to protect our robotic and process control testbed under many different configurations and scenarios while measuring the performance impacts to the system.
At this point, we have just begun validating our measurement systems and performed initial testing, but with all the progress we have made so far, I can only see great things coming out of our work. If you’re a manufacturer, I hope our research can help you continue to keep your operations safe, reliable, performing as expected, and more secure.
About the author
Related Posts
Comments
Good Job! This is an awesome post. I couldn't find it anywhere on google.





Thank you for providing us with valuable information