Taking Measure
Just a Standard Blog
Growing the Internet of Things Into a Safe and Responsible Member of Your Household

Technology is supposed to help us, but sometimes it feels like for every step forward we take two steps back. Like many people (and despite my resistance), my family has accumulated a few internet of things (IoT) devices in our home. Our motivation for acquiring them has been to streamline our lives. For instance, when we needed to be able to play our newborn son’s music anywhere in the house, a Bluetooth speaker seemed a natural fit — and it was! Inspired, we adopted a “voice assistant” for the kitchen to put all the information and entertainment of the internet at our fingertips while we prepared meals. This works great most of the time. The rest of the time, the voice assistant (who shall remain nameless) just ignores me! And if my wife tries, good luck. She’s ignored more often than not; at least that’s how it seems.
Issues with functionality aside, I was resistant to the haphazard introduction of IoT devices into our home for other reasons. Because I have worked closely with computers and technology for my whole career, the fact that these devices are computers is not lost on me. I also realize the many implications of putting an internet-connected, microphone-equipped computer on my kitchen counter (will a live feed from my house wind up on a sketchy website?). Thinking about how to secure these devices can lead to some interesting situations. We all know we should have strong passwords, but can you even put a password on a voice assistant that can read my emails to me (or anyone else in my home)? I can see all kinds of information about my house, but who else has access to my location and other data? What kind of encryption do these things use to protect my data? Maybe the better question is, how much of my data, if any, is stored on the device or up in the cloud where who can access it and what can be accessed is unclear? I can use a smart refrigerator to check if we need milk while I am on my way home from work, but does that mean someone could hack my fridge? How about my doorbell camera? As IoT grows in popularity, it’s likely that (despite my resistance) the number of “smart” things in my home will skyrocket, leaving me with many devices that will interact with me and each other in very complex ways. How will I manage the security of so many devices?
These kinds of challenges drive the work I do at the National Institute of Standards and Technology (NIST) in our Cybersecurity for IoT program. Our first publication, NISTIR 8228, focused on the many ways the limitations and new uses of IoT devices may affect the ways users (in the case of 8228, we mostly talk about big organizational users) protect their networks from attack and threats. Like the earlier examples, some IoT devices may simply not have the ability to perform some security or privacy actions. If a device’s software needs to be updated, and that device doesn’t notify you or provide a method for you to update it, well, then that device cannot be updated. It seems obvious when you say it that way, but when you’re buying a new coffee maker, the fact that it might need a software update one day may not pop into your head.
On top of that, the list of gaps in how security and privacy are achieved and what is supported in devices may grow long, especially if devices are incorporated before such gaps are considered. NISTIR 8228 draws attention to many of these gaps to help these big organizations think through the challenges of using IoT devices while still using standard security and privacy protections.
As we have worked through these aspects of IoT, we also learned that the creators of these devices could use guidance to help them incorporate more security features. This led to our most recent publication, NISTIR 8259, which is currently available as a draft. This time around, we outlined how manufacturers can identify and implement security features in their devices, as well as some considerations for communicating with their customers about the cybersecurity features in their devices. With this approach, we hope that at least some of the challenges identified in NISTIR 8228 can be alleviated since IoT will begin to support the current ways we protect networks. Beyond those, if manufacturers take these security considerations even further, our hope is even “more” security ends up being built in and delivered in a way that customers can easily make use of since even the best security feature may be ignored if it’s a pain to use.
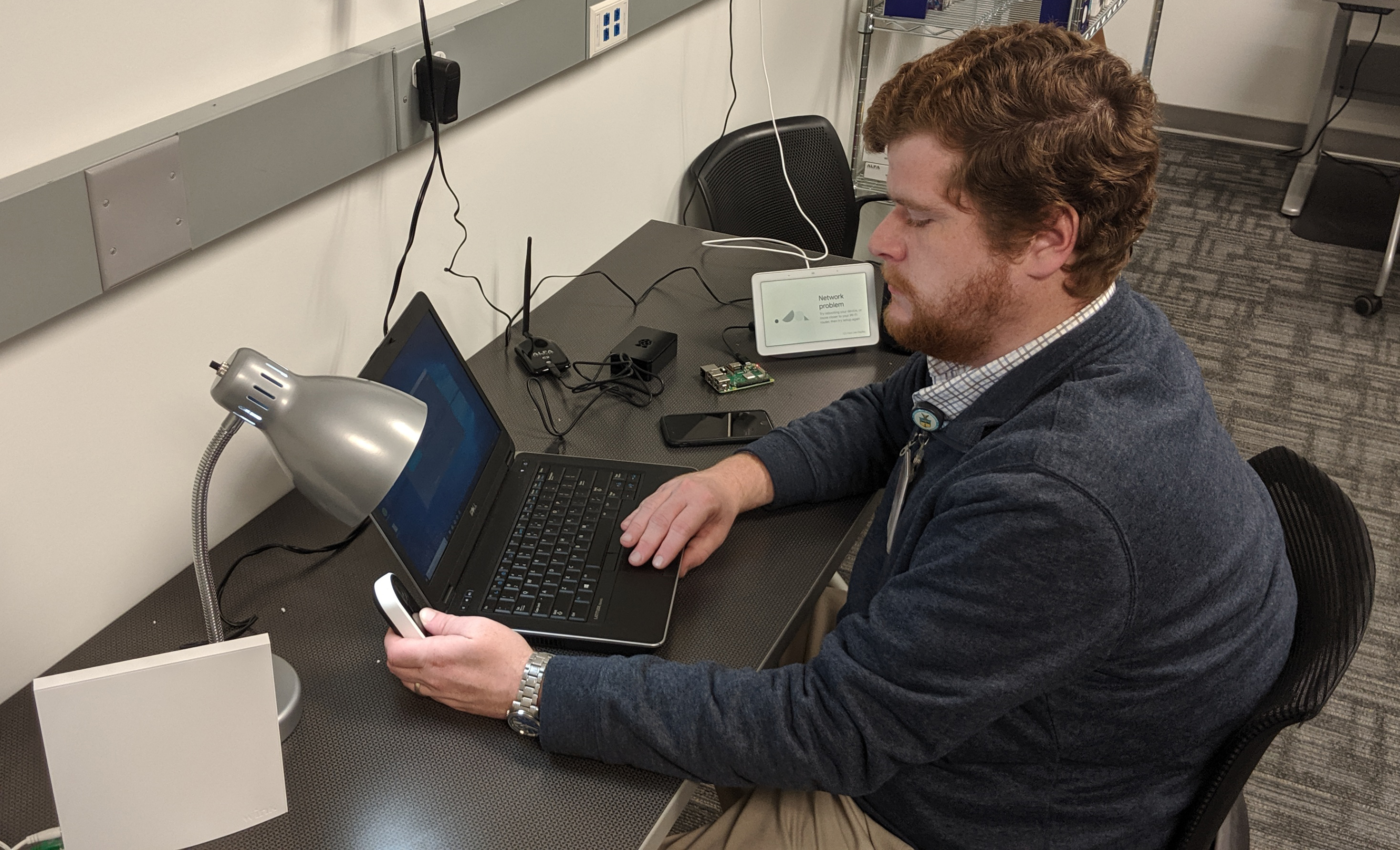
To understand the current state of security in some home IoT products, our team worked at the National Cybersecurity Center of Excellence to do a pilot study on the security of a sampling of small IoT devices marketed and intended to be used in homes, such as lightbulbs, outlets, and security lights, to name a few. Our lab plugged the devices in, hooked them up and, with an eye for good security practice, watched how the devices connected and communicated. We found that many of the devices support features discussed in NISTIR 8259, but in some cases, there were improvements that the makers of these kinds of products could consider adopting, such as having strong requirements for passwords as suggested by NIST. More details about this study and its resulting considerations can be found in the recent draft publication NISTIR 8267, for which we are currently gathering comments! Please note this document is intended for a more technical audience.
We have more work on the way, too, that will continue to help guide all interested parties through these challenges, so maybe I should be more optimistic about the devices I bring into my home. My aversion may be more related to being stuck in my ways more than anything else (I still use a desktop PC after all), and it is hard to argue with the benefits these devices bring when everything is running smoothly. We shouldn’t let fear of the unknown stop such great gains, and so NIST is helping to light the way to an IoT that can be adopted quickly and securely.





