Cybersecurity Insights
a NIST blog

NIST has a history of collaboration between its programs, which helps maximize project impacts and practicality to industry. One great example is between NIST’s National Cybersecurity Center of Excellence (NCCoE) and the Cybersecurity for the Internet of Things (IoT) Program. Recent project reports from the NCCoE include mappings of relevant IoT device cybersecurity capabilities and nontechnical supporting capabilities; these three mappings align NIST’s IoT cybersecurity guidance with real-world implementation approaches:
- Securing Telehealth Remote Patient Monitoring Ecosystem
- Securing Distributed Energy Resources
- Protecting Information and System Integrity in Industrial Control System Environments
Why did we create these mappings, and how can both customers and providers of IoT devices benefit from them? Let’s take a closer look.
The background
The NCCoE is a collaborative hub where organizations across industries, government agencies, and academic institutions work with NIST’s experts to address businesses’ most pressing cybersecurity challenges. Through these collaborations, the NCCoE develops modular, cost-effective, and easily adaptable example cybersecurity solutions—applying standards, best practices, and commercially available technology. Organizations can then adopt and integrate these modular cybersecurity solutions into their businesses without disrupting day-to-day operations.
NIST’s Cybersecurity for IoT Program supports the development of standards, guidance, and related tools to improve the cybersecurity of connected devices and the environments in which they are deployed. To integrate IoT cybersecurity guidance into real-world scenarios, the IoT team has been working closely with the NCCoE. For this collaboration, the IoT team identified NCCoE projects that incorporate IoT devices (and subsequently created IoT-specific cybersecurity guidance for these real-world scenarios). This IoT-specific guidance can be leveraged by organizations looking to implement NCCoE’s modular cybersecurity solutions[1]. But there’s another potential beneficiary of the IoT-specific guidance: the manufacturers of the IoT devices.
What IoT-specific guidance was created for these NCCoE projects?
NIST’s Cybersecurity for IoT Program has defined a catalog of IoT cybersecurity capabilities:
- Device cybersecurity capabilities are cybersecurity features or functions that IoT devices provide through their own technical means.
- Nontechnical supporting capabilities are actions that a manufacturer or third-party organization performs in support of the cybersecurity of an IoT device.
Device cybersecurity capabilities include features like access control and data encryption. Examples of nontechnical supporting capabilities include providing information about software updates, instructions for configuration settings, and supply chain information. Used together, these capabilities can help mitigate cybersecurity risks related to the use of IoT devices while assisting customers in achieving their goals. A subset of the capabilities in the full catalog was used to define a baseline set of cybersecurity capabilities (see NISTIR 8259A and NISTIR 8259B) that manufacturers should consider integrating into their IoT devices and that consumers should consider enabling/configuring in those devices.
Each NCCoE project identifies evaluation criteria–ways to assess how well the project’s reference design addresses the security requirements that it was intended to support. Essentially, the IoT-specific guidance for the NCCoE projects maps both technical capabilities and nontechnical supporting capabilities to the project’s identified evaluation criteria, linking the capabilities to a real-world solution. Basically, the mappings answer the question: what are the IoT technical and nontechnical capabilities that can best help organizations securely implement the NCCoE project solution in their environments?
How were the mappings created?
The IoT team previously mapped each of the device cybersecurity capabilities and nontechnical supporting capabilities to Subcategory outcomes from the NIST Cybersecurity Framework (see SP 800-213A Appendix C). Similarly, each NCCoE project lists key Cybersecurity Framework Subcategory outcomes that are relevant to the overall project and to the project’s evaluation criteria. Using this information, the IoT team identified IoT device cybersecurity capabilities and nontechnical supporting capabilities that align with each of the NCCoE project’s goals and evaluation criteria.
What do the mappings look like?
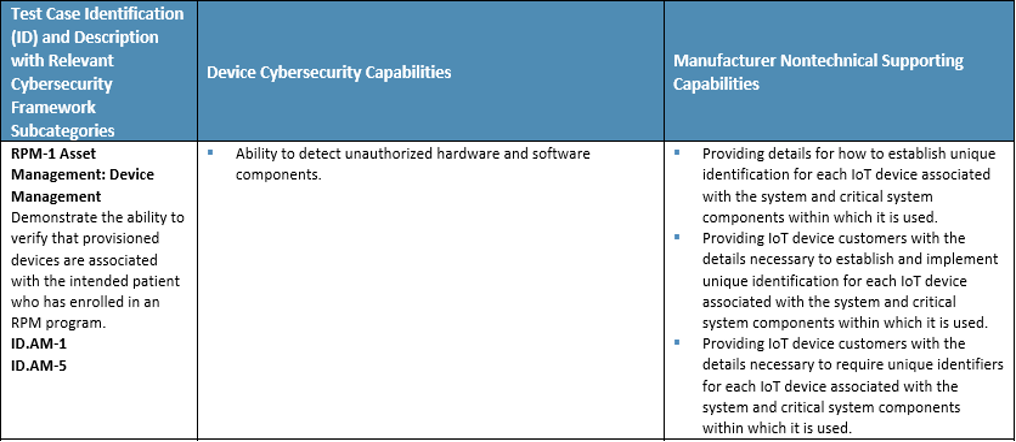
Below is an example mapping from one of the projects: Securing Telehealth Remote Patient Monitoring Ecosystem, showing both device cybersecurity capabilities and manufacturer nontechnical supporting capabilities relevant to one of the project’s evaluation criteria.
Who can benefit from these mappings?
For organizations implementing the NCCoE project’s example solution in their environment, the mapping demonstrates technical capabilities that these organizations should look for in IoT devices. The mapping also lists nontechnical capabilities that they may look for from a manufacturer or third party supporting the IoT device. Selecting devices and manufacturers/third parties that provide these capabilities can facilitate the secure deployment of IoT devices into the organization’s environment.
The mappings can also provide benefits for IoT device manufacturers (they illustrate the technical and nontechnical capabilities that organizations will be looking for in IoT devices and from manufacturers). Manufacturers may benefit from incorporating these technical capabilities into their devices and in developing nontechnical capabilities to provide services for their customers. Manufacturers providing these desired nontechnical capabilities for their customers and designing IoT devices (which provide desired technical capabilities) will demonstrate cybersecurity due diligence; they also may gain a competitive edge.
Moving forward, the Cybersecurity for IoT Program will continue collaborating with the NCCoE to develop IoT-specific guidance for projects containing IoT devices. As always, NIST welcomes your feedback. Contact us at IoTSecurity [at] NIST.gov (IoTSecurity[at]NIST[dot]gov).
[1] The IoT-specific guidance and NCCoE modular solutions are intended to be examples that organizations can adopt while assessing and managing cybersecurity risks or that manufacturers can consider when designing IoT devices. Organizations can adopt the NIST solution or use it to apply a similar thought process to manage cybersecurity risk.


