Baseline Tailor
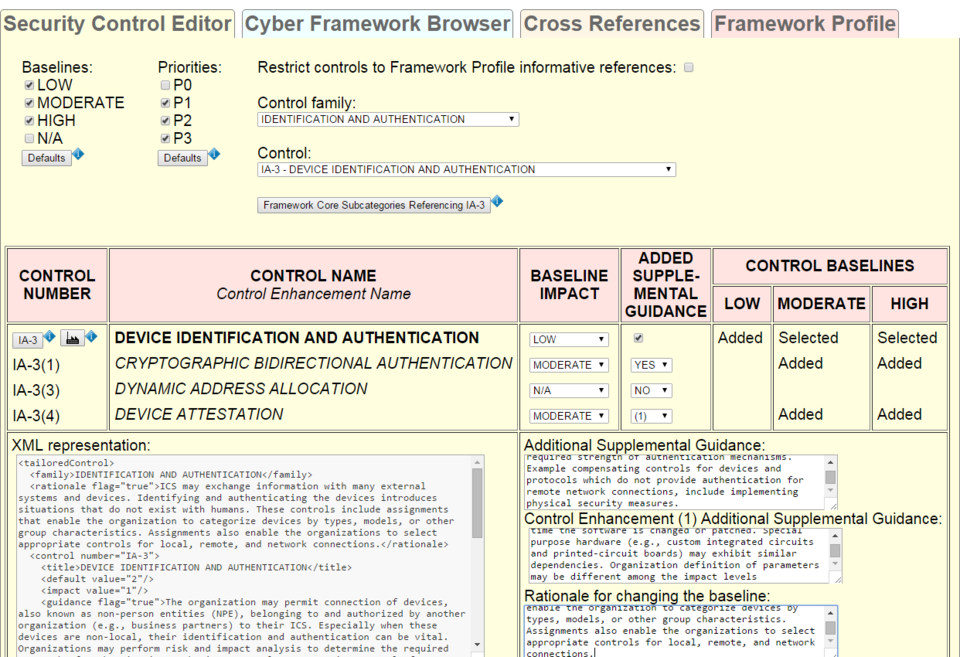
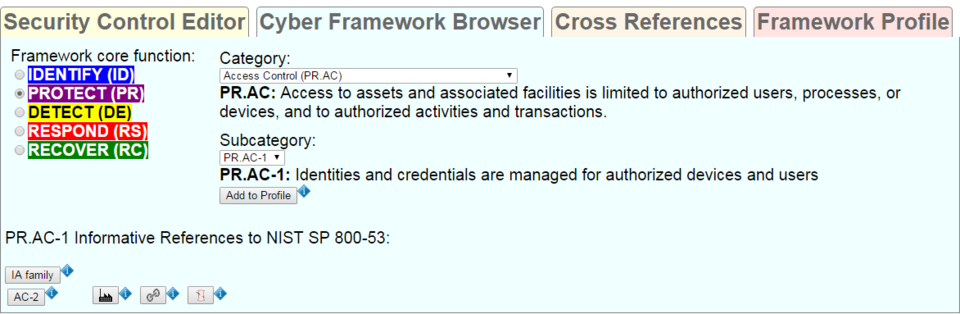
Baseline Tailor is a software tool for using the United States government's Cybersecurity Framework and for tailoring the NIST Special Publication (SP) 800-53 Revision 4 security controls. Baseline Tailor generates output in an Extensible Markup Language (XML) format capturing a user's Framework Profile and tailoring choices.
The Cybersecurity Framework provides a way for organizations to describe their current security posture and target state, and to communicate and assess progress toward meeting goals. The heart of the Cybersecurity Framework is the Framework Core: a taxonomy of cybersecurity activities common across critical infrastructure sectors. A Framework Profile is a subset of the outcomes in the Framework Core representing either an organization's current or target security posture. EL's Cybersecurity for Smart Manufacturing Systems project is developing a Framework Profile for various manufacturing scenarios.
NIST SP 800-53 provides a catalog of tailorable security controls organized into eighteen families. Each control has zero or more control enhancements, each of which adds additional functionality to and/or increases the strength of the control. The catalog specifies three security control baselines: for low, moderate, and high impact information systems. For example, an organization looking to select security controls for a low- impact system (where the consequences of compromised confidentiality, integrity, and availability of information are low) might begin with the controls in the baseline for the low impact level (or more succinctly, the low baseline) and tailor them as appropriate.
NIST SP 800-53 includes guidance for creating and documenting sets of control customizations called overlays to encourage the sharing of best security practices. NIST SP 800-82 (Guide to Industrial Control System Security) specifies an overlay for Industrial Control Systems, which are common in the utility, transportation, chemical, pharmaceutical, process, and durable goods manufacturing industries. Industrial Control Systems are vulnerable to many of the same security threats that affect traditional information systems, yet have unique needs requiring additional guidance beyond that offered by NIST SP 800-53.
Uses
The primary goals of Baseline Tailor are to:
- Make it easier to create and document Framework Profiles, tailored baselines and overlays.
- Enforce constraints on tailoring operations, helping to ensure that the result follows NIST SP 800-53 guidelines.
- Generate XML valid with respect to schemas for Framework Profiles and tailored controls that can be used in conjunction with other XML-encoded security content to achieve security automation.
Related Publications
Sample Screenshots