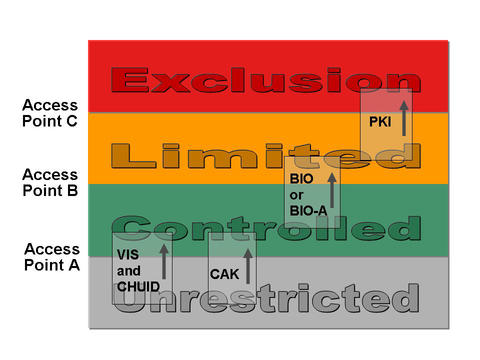
Four areas of increasing security in a facility (unrestricted, controlled, limited, and exclusion) and recommended authentication methods for passing through access points that separate them, including visual authentication (VIS), Cardholder Unique Identifier (CHUID), Card Authentication Key (CAK), biometric authentication supervised by a human attendant (BIO-A), biometric authentication unsupervised by an attendant (BIO) and Public Key Infrastructure (PKI).
Federal agencies have begun issuing a secure form of government-wide ID known as the Personal Identity Verification (PIV) card, mandated in 2004 by Homeland Security Presidential Directive 12 (HSPD-12). The National Institute of Standards and Technology (NIST) has released, for public comment, a draft publication (SP 800-116) outlining best-practice guidelines for making the new cards work with the physical access control systems (PACS) that authenticate the cardholders in federal facilities.
The PIV card is intended to work everywhere across the federal government. Conventional PACS, however, are not fully enabled to work with PIV cards and are not interoperable between agencies. In addition, PACS need to verify the cardholder's identity with an appropriate degree of confidence (denoted SOME, HIGH, OR VERY HIGH) depending upon the level of security needed at the particular location in the federal facility. Current PACS, however, may not be tailored to work at these graduated levels of "authentication assurance."
The draft publication explores methods for verifying identity in a simple model describing four zones of increasing security in a facility. The zones are unrestricted (e.g., outside the fence or walls of the facility), controlled (e.g., inside the fence or front door), limited (e.g., past a security checkpoint for employees in a facility) and exclusion (secure areas granted to individuals for specific needs). It specifies increasingly sophisticated authentication mechanisms for these zones, from visual and CHUID authentication (inspection of the features on the front and back of the PIV card and reading a unique number from the card) to biometrics (for example, the use of distinguishing features in fingerprints known as "minutiae" to grant access) and PKI Authentication (exchange of cryptographic information that requires the user to enter a PIN number).
The report takes into account the many different types of federal facilities, from single agency buildings to multiple-agency campuses. It also explores how PACS systems can work with temporary ID cards for guest employees or visitors. The report is intended for government officials responsible for implementing HSPD-12. It covers the use of PIV cards with PACS, rather than the process for issuing them.
The draft document, Special Publication 800-116, "A Recommendation for the Use of PIV Credentials in Physical Access Control Systems (PACS)," is available from the NIST Computer Security Resource Center. The public comment period for the document ends May 12, 2008. Comments may be submitted via electronic mail at piv_comments [at] nist.gov (piv_comments[at]nist[dot]gov) or via regular mail at 100 Bureau Drive (Mail Stop 8930) Gaithersburg, MD 20899-8930.

