Fingerprints
Fingerprints are the most commonly used biometric trait worldwide. Fingerprints are used to enroll populations into social services, allow individuals to access personal electronic devices, allow building and site access, and as a means for criminal investigation. Fingerprint recognition systems (verification (1:1 comparison) and identification (1:N comparison)) are a commodity, creating a need to develop the metrology to assess the performance of the different components of the fingerprint recognition/identification process. This will support the development and advancement of fingerprinting technology, promoting its further employment, and ensuring products meet the technical requirements of the end user. Fingerprinting technology comprises three primary functions: image capture, feature extraction, and matching. Image capture is provided by several different technologies, including electrical, optical, and the standard rolled ink prints. The optical readers can be both contact and noncontact. Feature extraction and matching are algorithmic.
The Security Technologies Group initiated the development of the metrologies to address the performance of each of the three primary fingerprint functions of image capture, feature extraction, and matching. Fingerprinting was selected as test bed for this new metrology because of its worldwide prevalence and acceptance of this new metrology would provide a similar metrology model for other biometric recognition technologies, such as face, iris, palm print, etc.
Future work includes the development of the measurement uncertainty analyses for image capture, feature extraction, and fingerprint matching; the development of electronic artifacts for assessment of feature extraction and matching algorithms; and the development of 3D physical artifacts for assessing image capture fidelity that can operate with any fingerprint capture device, thus supporting the assessment of the interoperability between reader modalities.
Synthesized fingerprints

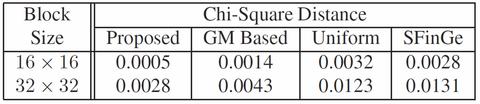
Reproducible and accurate evaluation of the fingerprint functions requires the establishment of a reference fingerprint or set of reference fingerprints. This reference print should be synthesized in such a way so that accurate knowledge of all features is known and, ideally, synthesized using stable open-source computer algorithms. In collaboration with Michigan State University (MSU), a new method has been developed for fingerprint image synthesis that is based on statistical feature models and not an abstraction of an actual print. Compared with the well-known method SFinGe, this method provides more control on the features in synthesized fingerprints by sampling the features from statistical fingerprint models and generating synthesized fingerprint images containing those sampled features. This approach is the first attempt in synthesizing fingerprints based on statistical feature models. The extracted feature sets of these synthesized prints better match that of the target set than do other synthesis methods, as shown in Table 1. Moreover, the known placement of the feature sets facilitates the ability to uniquely assess the performance of feature extractors and to act as a basis for the synthesis of 3D fingerprint artifacts for the assessment of image capture devices.
3D physical fingerprint artifacts
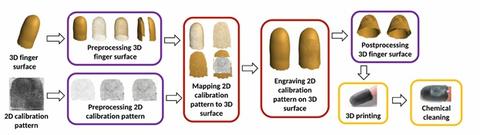
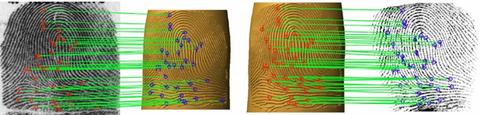
In collaboration with MSU, a novel method for generating 3D physical fingerprint artifacts has been developed, the process of which is shown diagrammatically in Figure 2. The measurement of the fidelity of the constructed 2D calibration pattern to the 3D artifact and of the 3D artifact to a print is shown in Figure 3. More detail can be found in S. Arora et al, “Design and Fabrication of 3D Fingerprint Targets.”

Furthermore, by using known patterns, such as linear or circular gratings, any pattern replication bias can be measured, recorded, and later used to correct the fingerprint image or to adjust the dimensions of the artifact and/or its pattern.
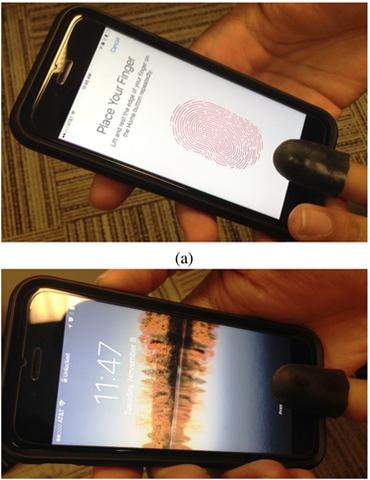
An example of the fidelity of the fingerprint artifact was in its use to gain access to an electronic device by an MSU researcher. Figure 4 shows a gold-plated wearable finger artifact that was used with a capacitive reader to unlock a cell phone (see Figure 5).
PUBLICATIONS
- S. S. Arora, A. K. Jain and N. G. Paulter, "Gold Fingers: 3D Targets for Evaluating Capacitive Readers", MSU Technical Report, MSU-CSE-17-1, 2017.
(https://biometrics.cse.msu.edu/Publications/Fingerprint/Aroraetal_Goldfinger_TechReport_MSU-CSE-17-1.pdf) - S. Arora, K. Cao, A.K. Jain, and N.G. Paulter, “Design and Fabrication of 3D Fingerprint Targets,” IEEE Transactions on Information Forensics and Security, Vol. 11, no. 10, October 2016. (https://doi.org/10.1109/TIFS.2016.2581306)
- S. Arora, A.K. Jain, and N.G. Paulter, “Whole Hand Targets: Evaluating Slap and Contactless Fingerprint Readers,” Proceedings 15th International Conference of the Biometrics Special Interest Group (BIOSIG), 22 to 23 September 2016, Darmstadt, Germany.(https://biometrics.cse.msu.edu/Publications/Fingerprint/Aroraetal_3DWholeHandTargets_BIOSIG2016_camready.pdf)
- S.S. Arora, K. Cao, A.K. Jain, N.G. Paulter, “3D Fingerprint Phantoms,” 22nd International Conference on Pattern Recognition, Stockholm, Sweden, 24 to 28 August 2014. (https://doi.org/10.1109/ICPR.2014.128)
- Qijun Zhao, Anil Jain, Nicholas Paulter, Melissa Taylor, and Yi Zhang, “A generative model for fingerprint minutiae,” 6th International Conference on Biometrics, Madrid, Spain, 4 to 7 June 2013. (https://doi.org/10.1109/ICB.2013.6613020)
- Q. Zhao, A.K. Jain, N.G. Paulter, and M. Taylor, “Fingerprint Image Synthesis based on Statistical Feature Models”, IEEE Fifth International Conference on Biometrics: Theory, Applications and Systems (BTAS 2012), 23 to 26 September 2012, Washington DC, USA. (https://doi.org/10.1109/BTAS.2012.6374554)
LINKS
- To Anil Jain’s programs: https://biometrics.cse.msu.edu/
- To Susan Ballou’s program: NIST Forensic Science Website
- On biometrics: https://biometrics.cse.msu.edu/info/index.html
- FBI on biometrics for identification: https://le.fbi.gov/science-and-lab/biometrics-and-fingerprints/biometrics
- On the Integrated Automated Fingerprint Identification System (IAFIS): https://ucr.fbi.gov/fingerprints_biometrics/biometric-center-of-excellence/files/iafis_0808_one-pager825
- On latent print examination: https://www.nist.gov/publications/latent-print-examination-and-human-factors-improving-practice-through-systems-approach
- Whole hand print: https://www.facebook.com/spartans.msu/videos/10154190971438020/
- Wearable glove with fingerprints:
- https://www.sciencefriday.com/segments/this-glove-fits-you-with-someone-elses-fingerprints/
- https://www.photonics.com/Article.aspx?AID=61247
- https://3dprint.com/153234/3d-printed-fingerprints-security/
- https://indianexpress.com/article/technology/science/indian-origin-scientist-creates-real-3d-hands-in-lab/
- https://qz.com/815103/3d-printed-hand-fingerprint-scanner/
- https://theworld.org/stories/2016/11/04/new-3d-printed-glove-can-dupe-fingerprint-scanners
CUSTOMERS/CONTRIBUTORS/COLLABORATORS
Anil Jain, Michigan State University
Susan Ballou, NIST
Sunpreet Arora, Michigan State University
Josh Engelsma, Michigan State University
Kai Cao, Michigan State University
Melissa Taylor, NIST
Qijun Zhao, Sichuan University, China
Contacts
-
(301) 975-5632

