Manufacturing Innovation Blog
Powered by the Manufacturing Extension Partnership
Cybersecurity Risk Mitigation for Small Manufacturers

Many small manufacturers have limited resources and lack the staff and tools to adequately address cybersecurity needs – leaving them particularly vulnerable to cyberattacks. One cyberattack can cost a small manufacturer a great deal of time and money and cause a great deal of stress.
Because the manufacturing sector is a consistent target of these attacks, new guidance focuses on helping manufacturers enhance their cybersecurity resiliency. NIST’s National Cybersecurity Center of Excellence (NCCoE) manufacturing team recently published a white paper that introduces security segmentation as a cost effective and efficient approach for smaller manufacturers to mitigate their risk and increase resilience.
Using security segmentation to protect assets
Security segmentation protects assets by grouping them based on both their communication and security requirements. Information technology (IT) and operational technology (OT) assets used in manufacturing environments require varying levels of cybersecurity protection. For example, assets involved in mission critical operations or in handling hazardous materials require strong cybersecurity protection whereas supporting systems such as an e-mail server may not.
IT and OT asset managers can more effectively manage cybersecurity by grouping assets according to similar cybersecurity protection needs and then managing the protection at the group level. Assets that need similar cybersecurity protection levels can be identified based on their similar operational functions, mission criticality levels, or data sensitivity levels.
Security zones, trusted communication, and security controls
The three pillars for security segmentation include security zones, trusted communication, and security controls.
- Security zones are groups of assets that have a similar operational function and criticality and share common cybersecurity requirements.
- Trusted communication is the principle that assets within a security zone trust each other but will not inherently trust communication from a different security zone.
- Security controls are cybersecurity practices used to safeguard the availability, confidentiality, and integrity of an organization’s information and systems.
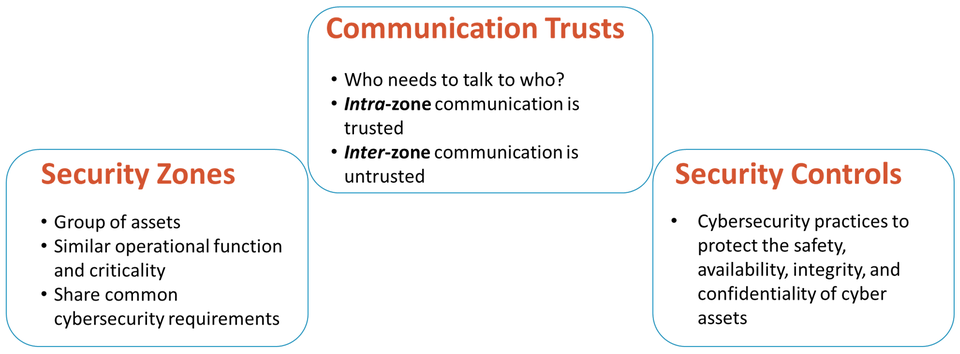
These pillars represent fundamental building blocks for a zone-based security architecture, providing a standardized way of designing a scalable and consistent security architecture.
Why should you implement security segmentation?
The well-defined networks that result from security segmentation lay the groundwork for improving your company’s overall security posture. This includes efficiently managing:
- Asset inventory.
- Communication between assets.
- Privileged access controls.
- Remote access capabilities.
Security segmentation also makes it easier for firms to effectively implement network visibility tools and identify where asset isolation is necessary.
Overall, the scalable and consistent security architecture that security segmentation provides will yield benefits including an adaptable configuration to support flexible manufacturing requirements and increased network resiliency for maintaining acceptable levels of service availability.
How to implement security segmentation
What are the steps for implementing security segmentation into your cybersecurity strategy? In the NIST white paper Security Segmentation in a Small Manufacturing Environment, the NCCoE manufacturing team presents an approach manufacturers can use in their own production environments. The paper walks through six steps using a sample manufacturing environment and shows each step’s output.
A six-step approach

Step 1: Identify list of assets
The first step is to inventory the hardware, software, and sensitive data or information assets involved in your business operations. Not only will an inventory help your organization identify the risk level of your assets, but it will also help you identify process inefficiencies and keep track of which assets need updating and upgrading. When an organization can manage a detailed asset inventory, cyber protections will be more precise and cost effective.
Step 2: Assess risk and create security zones
The second step is to conduct an informal assessment of the risk associated with your hardware assets and group them into security zones based on their operational similarities. Your organization should consider its own capabilities to determine how many security zones are appropriate. On one hand, more security zones will ultimately reduce risk. On the other hand, fewer security zones are easier to implement and manage. Information on the criticality and risks associated with assets may already be available in your organization’s business continuity or disaster recovery plans. You may be able to use information from these critical documents to assist with creating security zones.
Step 3: Determine the risk level for the security zones
It is essential for your organization to determine the risk level for each security zone based on your own categories of risk. The more critical an asset is, and the potential higher risk associated with the loss of assets in a security zone, the greater the protection needed. The paper includes questions and guidance to consider as you determine risk levels fitting your unique organization.
Step 4: Map communication between the security zones
It is important to distinguish between assets that are communicating within the same security zones, and assets that are communicating between different security zones. Validating these traffic flows helps you detect cyberattacks. This information can also be used to configure firewalls and deny traffic between zones except when necessary for manufacturing operation.
Step 5: Determine security controls for the security zones
IT and OT asset managers in your organization determine which cybersecurity controls are needed. This is based on the business goals combined with the impact of a cyber incident. The NISTIR 8183 Cybersecurity Framework for Manufacturing Profile can help your organization determine the cybersecurity practices needed to attain an appropriate security posture based on your business goals and desired risk reduction.
Step 6: Create the logical security architecture diagram
When you apply the building blocks of security segmentation to the target environment, it results in a logical security architecture. This architecture becomes the blueprint for improving the cybersecurity posture of your manufacturing environment. The paper shows a security architecture for a sample manufacturing environment as a result of applying these six steps.
Helping your facility become less vulnerable to a cyberattack
Implementing security segmentation into your manufacturing environment will not be a one-step process. However, it is a worthwhile venture as security zone-based architecture provides a standardized way of designing a scalable and consistent security architecture. Each step in implementing security segmentation will help your facility become more secure and less vulnerable to a cyberattack.
The brief overview in this blog summarized the process. For a better understanding of the security segmentation process, read the NCCoE’s newest white paper: NIST Cybersecurity White Paper Security Segmentation in a Small Manufacturing Environment (opens PDF).
As our team continues to work on topics such as security segmentation, we will communicate with manufacturing stakeholders to identify other cybersecurity challenges that are affecting the sector. If you’d like to get in touch with the NCCoE manufacturing team, contact us at manufacturing_nccoe [at] nist.gov (manufacturing_nccoe[at]nist[dot]gov).
Join an NCCoE community of interest
The NCCoE relies on public and private sector communities of interest to share business insights, technical expertise, challenges, and perspectives to guide our projects and help us advocate for strong cybersecurity. Communities of interest (COIs) are one of the greatest strengths of the NCCoE. We count on our COIs – those experts, innovators, and everyday users of cybersecurity and privacy technologies – to help identify and define the problems to be addressed by the NCCoE. Ultimately, COI members supply insight that supports the cyber resiliency of the U.S. economy. The NCCoE hosts several different communities, including one for the manufacturing sector. Learn more about the NCCoE’s Communities of Interest including the scope of our active COIs and how to join.





