Cybersecurity Insights
a NIST blog
The NIST Cybersecurity for IoT program published Considerations for Managing Internet of Things (IoT) Cybersecurity and Privacy Risks (NISTIR 8228) in June 2019, nearly 3 years ago. Since then, IoT technology has continued to develop and be adopted across sectors and markets. NIST’s own work, both in and outside IoT, has also progressed since the publication of NISTIR 8228. These developments warrant a new look at the contents of NISTIR 8228 and at future IoT cybersecurity priorities at NIST.
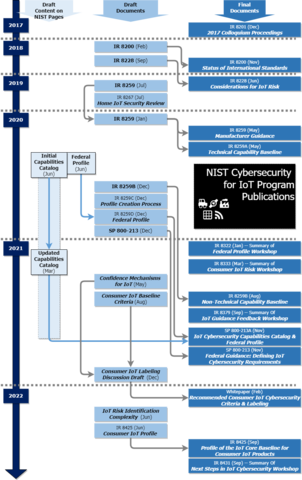
As the Cybersecurity for IoT program has progressed through guidance for IoT device manufacturers (NISTIR 8259), including a technical and non-technical capabilities core baseline (NISTIRs 8259A and 8259B) and IoT cybersecurity guidance for federal agencies (Special Publications (SPs) 800-213 and 800-213A), we received significant feedback across various sectors. This feedback included considerations, challenges, risks, technologies, solutions, and mitigations pertaining to IoT. For any sector, insights for IoT have matured, even to the point that there are now multiple “flavors” of IoT (e.g., IIoT, MIoT, AIoT). The wealth of insights from stakeholders has helped improve the Cybersecurity for IoT Program’s work since 2019, and it has stirred our thinking about how IoT has developed since we published NISTIR 8228.
IoT Device Heterogeneity and Cybersecurity Challenges
Regardless of sector, stakeholders reminded NIST of the diversity and heterogeneity of IoT devices and systems. Our work considers different device types, architectures, and configurations, and it tries to take a technology-agnostic approach whenever possible. At the same time, we have consistently heard about cybersecurity challenges for both manufacturers and customers for particular types of IoT devices and systems, especially those that have constrained hardware (e.g., limited memory or processing power, limited energy supply, limited connectivity). These constraints can make cybersecurity objectives difficult or impossible to achieve.
Devices with constraints may often, but not always, face different, possibly lower risk than other equipment. NIST heard that these challenges are compounded when IoT systems are assembled from many constrained devices (e.g., a distributed sensor network), possibly creating a larger scale break of expectations about the cybersecurity capabilities of the system and its components. Additionally, IoT devices and systems of constrained or highly distributed architectures may face challenges implementing common technical (e.g., cybersecurity state awareness) and non-technical (e.g., documentation) cybersecurity measures. NISTIR 8228 considers some of these aspects, but stakeholders may benefit from more specific considerations based on what NIST has learned.
IoT Risk Assessment and Mitigation
How this diversity and heterogeneity impact IoT risk has also been a common topic of discussion with our stakeholders. IoT devices and systems have multitudes of use cases, and any specific IoT device or system can have different risk considerations in different use cases, including ones well outside the manufacturer’s expectations. We heard about challenges predicting risk for IoT and adapting to IoT risk diversity and scale, even for enterprise systems. In the consumer sector, customer expectations and a moving target related to cybersecurity culture for consumer electronics complicates risk assessment and mitigations within that ecosystem as well. Further discussion of risk in NISTIR 8228 could help define risk or mitigation patterns that can help stakeholders work through these critical questions.
New Guidance and Technologies
The potential benefits of new guidance and technologies that have emerged since the program began its work should also be considered. Documents such as Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations Revision 1 (SP 800-161r1), Guide to Industrial Control Systems (ICS) Security Revision 3 (SP 800-82r3), the Secure Software Development Framework (SSDF) and the Risk Management Framework, and our work documents such as NISTIRs 8259/A/B and SPs 800-213/A can offer different perspectives that help inform the discussion of assessing and mitigating risk when IoT devices and systems are part of the equation. Stakeholders found many technologies (e.g., Manufacturer Usage Description (MUD), hardware root of trust, Software Bill of Materials (SBOM)) that could be useful risk mitigations for IoT use cases and may have a place in the discussions of NISTIR 8228.
All of these ideas almost certainly won’t end up in a revised NISTIR 8228, especially those that have little to no implication for the enterprise sector, but the format, approach, and concepts of NISTIR 8228 could be used to craft considerations for other sectors such as consumer. Expansion of the NISTIR 8259 series may be more appropriate for other ideas that have better applicability to the manufacturing side of the ecosystem of IoT.
With all this exciting work on the horizon, the Cybersecurity for IoT Program will be hosting an event on June 22, 2022, to discuss the IoT landscape and the team’s next steps with others, so mark your calendars! More information about this event will be posted to our program website, where you can learn more about all the Cybersecurity for IoT Program’s prior, current, and upcoming activities.


